Deadlock Prevention And Avoidance
Last Updated :
30 Oct, 2023
When two or more processes try to access the critical section at the same time and they fail to access simultaneously or stuck while accessing the critical section then this condition is known as Deadlock.
- Every process needs a few resources to finish running.
- The procedure makes a resource request. If the resource is available, the OS will grant it; otherwise, the process will wait.
- When the process is finished, it is released.
Deadlock Characteristics
The deadlock has the following characteristics:
- Mutual Exclusion
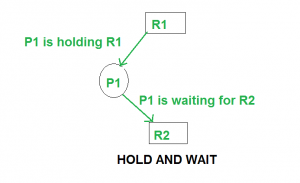
- Hold and Wait
- No preemption
- Circular wait
Deadlock Prevention
We can prevent a Deadlock by eliminating any of the above four conditions.
Eliminate Mutual Exclusion: It is not possible to dis-satisfy the mutual exclusion because some resources, such as the tape drive and printer, are inherently non-shareable.
Eliminate Hold and wait: Allocate all required resources to the process before the start of its execution, this way hold and wait condition is eliminated but it will lead to low device utilization. for example, if a process requires a printer at a later time and we have allocated a printer before the start of its execution printer will remain blocked till it has completed its execution. The process will make a new request for resources after releasing the current set of resources. This solution may lead to starvation.
Eliminate No Preemption : Preempt resources from the process when resources are required by other high-priority processes.
Eliminate Circular Wait : Each resource will be assigned a numerical number. A process can request the resources to increase/decrease. order of numbering. For Example, if the P1 process is allocated R5 resources, now next time if P1 asks for R4, R3 lesser than R5 such a request will not be granted, only a request for resources more than R5 will be granted.
Detection and Recovery: Another approach to dealing with deadlocks is to detect and recover from them when they occur. This can involve killing one or more of the processes involved in the deadlock or releasing some of the resources they hold.
Deadlock Avoidance
A deadlock avoidance policy grants a resource request only if it can establish that granting the request cannot lead to a deadlock either immediately or in the future. The kernal lacks detailed knowledge about future behavior of processes, so it cannot accurately predict deadlocks. To facilitate deadlock avoidance under these conditions, it uses the following conservative approach: Each process declares the maximum number of resource units of each class that it may require. The kernal permits a process to request these resource units in stages- i.e. a few resource units at a time- subject to the maximum number declared by it and uses a worst case analysis technique to check for the possibility of future deadlocks. A request is granted only if there is no possibility of deadlocks; otherwise, it remains pending until it can be granted. This approach is conservative because a process may complete its operation without requiring the maximum number of units declared by it.
Resource Allocation Graph
The resource allocation graph (RAG) is used to visualize the system’s current state as a graph. The Graph includes all processes, the resources that are assigned to them, as well as the resources that each Process requests. Sometimes, if there are fewer processes, we can quickly spot a deadlock in the system by looking at the graph rather than the tables we use in Banker’s algorithm. Deadlock avoidance can also be done with Banker’s Algorithm.
Banker’s Algorithm
Bankers’s Algorithm is a resource allocation and deadlock avoidance algorithm which test all the request made by processes for resources, it checks for the safe state, and after granting a request system remains in the safe state it allows the request, and if there is no safe state it doesn’t allow the request made by the process.
Inputs to Banker’s Algorithm
- Max needs of resources by each process.
- Currently, allocated resources by each process.
- Max free available resources in the system.
The request will only be granted under the below condition
- If the request made by the process is less than equal to the max needed for that process.
- If the request made by the process is less than equal to the freely available resource in the system.
Timeouts: To avoid deadlocks caused by indefinite waiting, a timeout mechanism can be used to limit the amount of time a process can wait for a resource. If the help is unavailable within the timeout period, the process can be forced to release its current resources and try again later.
Example:
Total resources in system:
A B C D
6 5 7 6
The total number of resources are
Available system resources are:
A B C D
3 1 1 2
Available resources are
Processes (currently allocated resources):
A B C D
P1 1 2 2 1
P2 1 0 3 3
P3 1 2 1 0
Maximum resources we have for a process
Processes (maximum resources):
A B C D
P1 3 3 2 2
P2 1 2 3 4
P3 1 3 5 0
Need = Maximum Resources Requirement – Currently Allocated Resources.
Need = maximum resources - currently allocated resources.
Processes (need resources):
A B C D
P1 2 1 0 1
P2 0 2 0 1
P3 0 1 4 0
Conclusion
Operating Systems employ deadlock avoidance to prevent deadlock by using the Banker’s algorithm or the resource allocation graph.
Deadlock avoidance works by informing the operating system of the resources needed by the process to finish execution, and the operating system then determines whether or not the requirements can be met.
The System is said to be in a Safe state if all the resources required by the Process are satisfied with the resources that are currently available.
The System is said to be in an unsafe state if all of the resource requirements of the Process cannot be met by the available resources in any way.
Note: Deadlock prevention is more strict than Deadlock Avoidance.
Frequently Asked Questions
Q.1: What is deadlock prevention?
Answer:
Deadlock prevention is a technique used in operating systems to ensure that deadlocks, which are situations where two or more processes are unable to proceed because each is waiting for the other to release a resource, do not occur. It involves designing the system in such a way that at least one of the necessary conditions for deadlock cannot hold. This typically requires careful resource allocation and tracking, as well as enforcing certain rules and protocols to prevent deadlock formation.
Q.2: What is deadlock avoidance?
Answer:
Deadlock avoidance is another technique used in operating systems to deal with deadlocks. Unlike deadlock prevention, which aims to eliminate the possibility of deadlocks, deadlock avoidance focuses on dynamically detecting and avoiding situations that could lead to deadlocks. It involves analyzing the resource allocation state and resource requests made by processes to determine if granting a request would potentially result in a deadlock. If a potential deadlock is detected, the system can make decisions to avoid it by selectively granting or denying resource requests.
Share your thoughts in the comments
Please Login to comment...