A process in operating system uses resources in the following way.
- Requests a resource
- Use the resource
- Releases the resource
A deadlock is a situation where a set of processes are blocked because each process is holding a resource and waiting for another resource acquired by some other process.
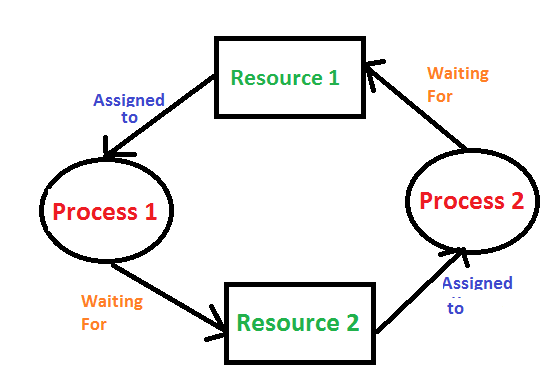
Consider an example when two trains are coming toward each other on the same track and there is only one track, none of the trains can move once they are in front of each other. A similar situation occurs in operating systems when there are two or more processes that hold some resources and wait for resources held by other(s). For example, in the below diagram, Process 1 is holding Resource 1 and waiting for resource 2 which is acquired by process 2, and process 2 is waiting for resource 1.
Examples Of Deadlock
- The system has 2 tape drives. P0 and P1 each hold one tape drive and each needs another one.
- Semaphores A and B, initialized to 1, P0, and P1 are in deadlock as follows:
- P0 executes wait(A) and preempts.
- P1 executes wait(B).
- Now P0 and P1 enter in deadlock.
|
P0
|
P1
|
|
wait(A);
|
wait(B)
|
|
wait(B);
|
wait(A)
|
3. Assume the space is available for allocation of 200K bytes, and the following sequence of events occurs.
|
P0
|
P1
|
|
Request 80KB;
|
Request 70KB;
|
|
Request 60KB;
|
Request 80KB;
|
Deadlock occurs if both processes progress to their second request.
Deadlock can arise if the following four conditions hold simultaneously (Necessary Conditions)
Mutual Exclusion: Two or more resources are non-shareable (Only one process can use at a time)
Hold and Wait: A process is holding at least one resource and waiting for resources.
No Preemption: A resource cannot be taken from a process unless the process releases the resource.
Circular Wait: A set of processes waiting for each other in circular form.
Methods for handling deadlock
There are three ways to handle deadlock
1) Deadlock prevention or avoidance:
Prevention:
The idea is to not let the system into a deadlock state. This system will make sure that above mentioned four conditions will not arise. These techniques are very costly so we use this in cases where our priority is making a system deadlock-free.
One can zoom into each category individually, Prevention is done by negating one of the above-mentioned necessary conditions for deadlock. Prevention can be done in four different ways:
1. Eliminate mutual exclusion 3. Allow preemption
2. Solve hold and Wait 4. Circular wait Solution
Avoidance:
Avoidance is kind of futuristic. By using the strategy of “Avoidance”, we have to make an assumption. We need to ensure that all information about resources that the process will need is known to us before the execution of the process. We use Banker’s algorithm (Which is in turn a gift from Dijkstra) to avoid deadlock.
In prevention and avoidance, we get the correctness of data but performance decreases.
2) Deadlock detection and recovery: If Deadlock prevention or avoidance is not applied to the software then we can handle this by deadlock detection and recovery. which consist of two phases:
- In the first phase, we examine the state of the process and check whether there is a deadlock or not in the system.
- If found deadlock in the first phase then we apply the algorithm for recovery of the deadlock.
In Deadlock detection and recovery, we get the correctness of data but performance decreases.
Recovery from Deadlock
1. Manual Intervention:
When a deadlock is detected, one option is to inform the operator and let them handle the situation manually. While this approach allows for human judgment and decision-making, it can be time-consuming and may not be feasible in large-scale systems.
2. Automatic Recovery:
An alternative approach is to enable the system to recover from deadlock automatically. This method involves breaking the deadlock cycle by either aborting processes or preempting resources. Let’s delve into these strategies in more detail.
Recovery from Deadlock: Process Termination:
1. Abort all deadlocked processes:
This approach breaks the deadlock cycle, but it comes at a significant cost. The processes that were aborted may have executed for a considerable amount of time, resulting in the loss of partial computations. These computations may need to be recomputed later.
2. Abort one process at a time:
Instead of aborting all deadlocked processes simultaneously, this strategy involves selectively aborting one process at a time until the deadlock cycle is eliminated. However, this incurs overhead as a deadlock-detection algorithm must be invoked after each process termination to determine if any processes are still deadlocked.
Factors for choosing the termination order:
– The process’s priority
– Completion time and the progress made so far
– Resources consumed by the process
– Resources required to complete the process
– Number of processes to be terminated
– Process type (interactive or batch)
Recovery from Deadlock: Resource Preemption:
1. Selecting a victim:
Resource preemption involves choosing which resources and processes should be preempted to break the deadlock. The selection order aims to minimize the overall cost of recovery. Factors considered for victim selection may include the number of resources held by a deadlocked process and the amount of time the process has consumed.
2. Rollback:
If a resource is preempted from a process, the process cannot continue its normal execution as it lacks the required resource. Rolling back the process to a safe state and restarting it is a common approach. Determining a safe state can be challenging, leading to the use of total rollback, where the process is aborted and restarted from scratch.
3. Starvation prevention:
To prevent resource starvation, it is essential to ensure that the same process is not always chosen as a victim. If victim selection is solely based on cost factors, one process might repeatedly lose its resources and never complete its designated task. To address this, it is advisable to limit the number of times a process can be chosen as a victim, including the number of rollbacks in the cost factor.
3) Deadlock ignorance: If a deadlock is very rare, then let it happen and reboot the system. This is the approach that both Windows and UNIX take. we use the ostrich algorithm for deadlock ignorance.
In Deadlock, ignorance performance is better than the above two methods but the correctness of data.
Safe State:
A safe state can be defined as a state in which there is no deadlock. It is achievable if:
- If a process needs an unavailable resource, it may wait until the same has been released by a process to which it has already been allocated. if such a sequence does not exist, it is an unsafe state.
- All the requested resources are allocated to the process.
Exercise:
1) Suppose n processes, P1, …. Pn shares m identical resource units, which can be reserved and released one at a time. The maximum resource requirement of process Pi is Si, where Si > 0. Which one of the following is a sufficient condition for ensuring that deadlock does not occur? (GATE CS 2005)

(A) A
(B) B
(C) C
(D) D
For the solution, see Question 4 of https://www.geeksforgeeks.org/operating-systems-set-16/
See QUIZ ON DEADLOCK for more questions.
References:
http://www2.latech.edu/~box/os/ch07.pdf
http://www.cs.uic.edu/~jbell/CourseNotes/OperatingSystems/7_Deadlocks.html
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...