A local Area Network (LAN) is a data communication network connecting various terminals or computers within a building or limited geographical area. The connection between the devices could be wired or wireless. Ethernet, Token rings, and Wireless LAN using IEEE 802.11 are examples of standard LAN technologies.
What is Ethernet?
Ethernet is the most widely used LAN technology and is defined under IEEE standards 802.3. The reason behind its wide usability is that Ethernet is easy to understand, implement, and maintain, and allows low-cost network implementation. Also, Ethernet offers flexibility in terms of the topologies that are allowed. Ethernet generally uses a bus topology. Ethernet operates in two layers of the OSI model, the physical layer and the data link layer. For Ethernet, the protocol data unit is a frame since we mainly deal with DLLs. In order to handle collisions, the Access control mechanism used in Ethernet is CSMA/CD.
Although Ethernet has been largely replaced by wireless networks, wired networking still uses Ethernet more frequently. Wi-Fi eliminates the need for cables by enabling users to connect their smartphones or laptops to a network wirelessly. The 802.11ac Wi-Fi standard offers faster maximum data transfer rates when compared to Gigabit Ethernet. However, wired connections are more secure and less susceptible to interference than wireless networks. This is the main justification for why so many companies and organizations continue to use Ethernet.
History of Ethernet
Robert Metcalfe’s invention of Ethernet in 1973 completely changed computer networking. With Ethernet Version 2’s support for 10 Mbps and an initial data rate of 2.94 Mbps, it first gained popularity in 1982. Ethernet’s adoption was accelerated by the IEEE 802.3 standardization in 1983. Local area networks (LANs) and the internet were able to expand quickly thanks to the rapid evolution and advancement of Ethernet, which over time reached speeds of 100 Mbps, 1 Gbps, 10 Gbps, and higher. It evolved into the standard technology for wired network connections, enabling dependable and quick data transmission for private residences, commercial buildings, and data centers all over the world.
There are different types of Ethernet networks that are used to connect devices and transfer data.
Let’s discuss them in simple terms:
1. Fast Ethernet: This type of Ethernet network uses cables called twisted pair or CAT5. It can transfer data at a speed of around 100 Mbps (megabits per second). Fast Ethernet uses both fiber optic and twisted pair cables to enable communication. There are three categories of Fast Ethernet: 100BASE-TX, 100BASE-FX, and 100BASE-T4.
2. Gigabit Ethernet: This is an upgrade from Fast Ethernet and is more common nowadays. It can transfer data at a speed of 1000 Mbps or 1 Gbps (gigabit per second). Gigabit Ethernet also uses fiber optic and twisted pair cables for communication. It often uses advanced cables like CAT5e, which can transfer data at a speed of 10 Gbps.
3.10-Gigabit Ethernet: This is an advanced and high-speed network that can transmit data at a speed of 10 gigabits per second. It uses special cables like CAT6a or CAT7 twisted-pair cables and fiber optic cables. With the help of fiber optic cables, this network can cover longer distances, up to around 10,000 meters.
4. Switch Ethernet: This type of network involves using switches or hubs to improve network performance. Each workstation in this network has its own dedicated connection, which improves the speed and efficiency of data transfer. Switch Ethernet supports a wide range of speeds, from 10 Mbps to 10 Gbps, depending on the version of Ethernet being used.
In summary, Fast Ethernet is the basic version with a speed of 100 Mbps, Gigabit Ethernet is faster with a speed of 1 Gbps, 10-Gigabit Ethernet is even faster with a speed of 10 Gbps, and Switch Ethernet uses switches or hubs to enhance network performance.
The Manchester Encoding Technique is used in Ethernet.
Using Manchester encoding, data can be transmitted over a physical medium in communication systems. It is a type of line coding where the signal transitions, as opposed to the absolute voltage levels, serve as the data representation.
Each bit of information is split into two equal time periods, or “halves,” in Manchester encoding. If the signal level is higher during the first half of the bit period than it is during the second, the result is a logic high (typically 1), or vice versa.
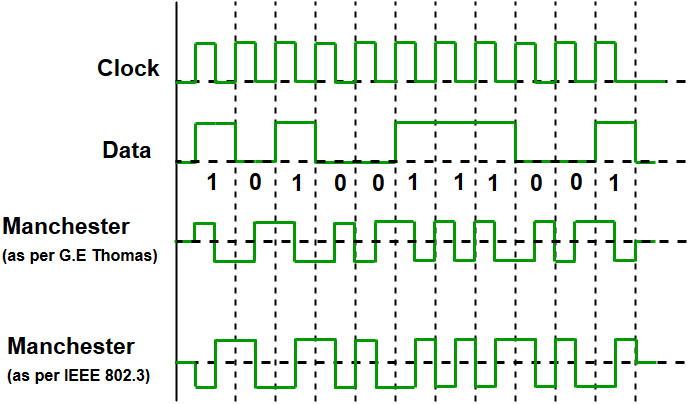
Since we are talking about IEEE 802.3 standard Ethernet, therefore, 0 is expressed by a high-to-low transition, a 1 by the low-to-high transition. In both Manchester Encoding and Differential Manchester, the Encoding Baud rate is double of bit rate.
Key Features of Ethernet
- Speed: Ethernet is capable of transmitting data at high speeds, with current Ethernet standards supporting speeds of up to 100 Gbps.
- Flexibility: Ethernet is a flexible technology that can be used with a wide range of devices and operating systems. It can also be easily scaled to accommodate a growing number of users and devices.
- Reliability: Ethernet is a reliable technology that uses error-correction techniques to ensure that data is transmitted accurately and efficiently.
- Cost-effectiveness: Ethernet is a cost-effective technology that is widely available and easy to implement. It is also relatively low-maintenance, requiring minimal ongoing support.
- Interoperability: Ethernet is an interoperable technology that allows devices from different manufacturers to communicate with each other seamlessly.
- Security: Ethernet includes built-in security features, including encryption and authentication, to protect data from unauthorized access.
- Manageability: Ethernet networks are easily managed, with various tools available to help network administrators monitor and control network traffic.
- Compatibility: Ethernet is compatible with a wide range of other networking technologies, making it easy to integrate with other systems and devices.
- Availability: Ethernet is a widely available technology that can be used in almost any setting, from homes and small offices to large data centers and enterprise-level networks.
- Simplicity: Ethernet is a simple technology that is easy to understand and use. It does not require specialized knowledge or expertise to set up and configure, making it accessible to a wide range of users.
- Standardization: Ethernet is a standardized technology, which means that all Ethernet devices and systems are designed to work together seamlessly. This makes it easier for network administrators to manage and troubleshoot Ethernet networks.
- Scalability: Ethernet is highly scalable, which means it can easily accommodate the addition of new devices, users, and applications without sacrificing performance or reliability.
- Broad compatibility: Ethernet is compatible with a wide range of protocols and technologies, including TCP/IP, HTTP, FTP, and others. This makes it a versatile technology that can be used in a variety of settings and applications.
- Ease of integration: Ethernet can be easily integrated with other networking technologies, such as Wi-Fi and Bluetooth, to create a seamless and integrated network environment.
- Ease of troubleshooting: Ethernet networks are easy to troubleshoot and diagnose, thanks to a range of built-in diagnostic and monitoring tools. This makes it easier for network administrators to identify and resolve issues quickly and efficiently.
- Support for multimedia: Ethernet supports multimedia applications, such as video and audio streaming, making it ideal for use in settings where multimedia content is a key part of the user experience.Ethernet is a reliable, cost-effective, and widely used LAN technology that offers high-speed connectivity and easy manageability for local networks.
Advantages of Ethernet
Speed: When compared to a wireless connection, Ethernet provides significantly more speed. Because Ethernet is a one-to-one connection, this is the case. As a result, speeds of up to 10 Gigabits per second (Gbps) or even 100 Gigabits per second (Gbps) are possible.
Efficiency: An Ethernet cable, such as Cat6, consumes less electricity, even less than a wifi connection. As a result, these ethernet cables are thought to be the most energy-efficient.
Good data transfer quality: Because it is resistant to noise, the information transferred is of high quality.
Baud rate = 2* Bit rate
Ethernet LANs consist of network nodes and interconnecting media, or links.
The network nodes can be of two types:
Data Terminal Equipment (DTE): Media, Generally, DTEs are the end devices that convert the user information into signals or reconvert the received signals. DTE devices are: personal computers, workstations, file servers or print servers also referred to as end stations. These devices are either the source or the destination of data frames. The data terminal equipment may be a single piece of equipment or multiple pieces of equipment that are interconnected and perform all the required functions to allow the user to communicate. A user can interact with DTE or DTE may be a user.
Data Communication Equipment (DCE):- DCEs are the intermediate network devices that receive and forward frames across the network. They may be either standalone devices such as repeaters, network switches, or routers, or maybe communications interface units such as interface cards and modems. The DCE performs functions such as signal conversion, coding, and maybe a part of the DTE or intermediate equipment.
Disadvantages of Ethernet
Distance limitations: Ethernet has distance limitations, with the maximum cable length for a standard Ethernet network being 100 meters. This means that it may not be suitable for larger networks that require longer distances.
Bandwidth sharing: Ethernet networks share bandwidth among all connected devices, which can result in reduced network speeds as the number of devices increases.
Security vulnerabilities: Although Ethernet includes built-in security features, it is still vulnerable to security breaches, including unauthorized access and data interception.
Complexity: Ethernet networks can be complex to set up and maintain, requiring specialized knowledge and expertise.
Compatibility issues: While Ethernet is generally interoperable with other networking technologies, compatibility issues can arise when integrating with older or legacy systems.
Cable installation: Ethernet networks require the installation of physical cables, which can be time-consuming and expensive to install.
Physical limitations: Ethernet networks require physical connections between devices, which can limit mobility and flexibility in network design.
ALOHA
The Aloha protocol was designed as part of a project at the University of Hawaii. It provided data transmission between computers on several of the Hawaiian Islands using packet radio networks. Aloha is a multiple access protocol at the data link layer and proposes how multiple terminals can access the medium without interference or collision.
There are two different versions of Aloha:
1. Pure Aloha
Pure Aloha is an un-slotted, decentralized, and simple-to-implement protocol. In pure Aloha, the stations simply transmit frames whenever they want data to send. It does not check whether the channel is busy or not before transmitting. In the event that two or more stations transmit simultaneously, a collision occurs and frames are destroyed. Whenever any station transmits a frame, it expects acknowledgment from the receiver. If it is not received within a specified time, the station assumes that the frame or acknowledgment has been destroyed. Then, the station waits for a random amount of time and sends the frame again. This randomness helps in avoiding more collisions. This scheme works well in small networks where the load is not much. But in largely loaded networks, this scheme fails poorly. This led to the development of Slotted Aloha.
To assure pure aloha: Its throughput and rate of transmission of the frame are to be predicted.
For that, let’s make some assumptions:
- All the frames should be the same length.
- Stations can not generate frames while transmitting or trying to transmit frames.
- The population of stations attempts to transmit (both new frames and old frames that collided) according to a Poisson distribution.

Vulnerable Time = 2 * Tt
The efficiency of Pure ALOHA:
Pure Aloha= G * e^-2G
where G is number of stations wants to transmit in Tt slot.
Maximum Efficiency:
Maximum Efficiency will be obtained when G=1/2
(pure aloha)max = 1/2 * e^-1
= 0.184
Which means, in Pure ALOHA, only about 18.4% of the time is used for successful transmissions.
2. Slotted Aloha
This is quite similar to Pure Aloha, differing only in the way transmissions take place. Instead of transmitting right at the demand time, the sender waits for some time. In slotted ALOHA, the time of the shared channel is divided into discrete intervals called Slots. The stations are eligible to send a frame only at the beginning of the slot and only one frame per slot is sent. If any station is not able to place the frame onto the channel at the beginning of the slot, it has to wait until the beginning of the next time slot. There is still a possibility of collision if two stations try to send at the beginning of the same time slot. But still, the number of collisions that can possibly take place is reduced by a large margin and the performance becomes much well compared to Pure Aloha.
.webp)
Collision is possible only in the current slot. Therefore, Vulnerable Time is Tt.
The efficiency of Slotted Aloha
slotted Aloha= G * e^-G
Maximum Efficiency:
(slotted)max = 1 * e^-1
= 1/e = 0.368
Maximum Efficiency, in Slotted ALOHA, is 36.8%.
How Ethernet Works?
In the Open Systems Interconnection (OSI) model, the Ethernet is located in the lower layers and facilitates the operation of the physical and data link layers. The OSI model consists of seven layers, which are as follows.
The topmost layer, known as the application layer, is what enables users to download and access data from email clients or web browsers. With the aid of the application, users enter their queries, and the request is then sent to the following layer, which is known as a “packet.” The packet contains data about the sender and the destination web address. The packet is transmitted from the application layer until it reaches the bottom layer, also known as the Ethernet frame.
How do I connect an Ethernet Cable?
- Locate the Ethernet ports on both the connected devices and then identify them. These ports are typically marked with an “Ethernet” or “LAN” symbol and resemble slightly larger telephone jacks.
- Verify the cable: Make certain you have the correct Ethernet cable. Cat5e, Cat6, or Cat6a cables are common names for Ethernet cables. These cables are typically terminated with an RJ-45 connector and contain four pairs of twisted wires.
- Remove any protective caps from the connectors on the Ethernet cable to prepare the cable. Look over the cable carefully for any flaws like cuts or frayed wires. It is best to use a new cable if the one you have is damaged.
- Take the Ethernet cable’s one end and insert it to complete the connection.
- Verify the cable: Make certain you have the correct Ethernet cable. Cat5e, Cat6, or Cat6a cables are common names for Ethernet cables. These cables are typically terminated with an RJ-45 connector and contain four pairs of twisted wires.
- Remove any protective caps from the connectors on the Ethernet cable to prepare the cable. Look over the cable carefully for any flaws like cuts or frayed wires. It is best to use a new cable if the one you have is damaged.
Frequently Asked Questions
Q.1: What is Ethernet?
Answer:
Ethernet is a widely used networking technology that allows devices to communicate and share data over a local area network (LAN). It uses a set of protocols and standards to establish a reliable and efficient connection between devices.
Q.2: What are the advantages of Ethernet?
Answer:
Ethernet offers several advantages, including high data transfer speeds, low latency, scalability, and widespread compatibility. It provides a stable and reliable network connection, making it suitable for various applications such as internet access, file sharing, and multimedia streaming.
Q.3:What types of cables are used in Ethernet networks?
Answer:
Ethernet networks commonly use copper cables, such as twisted pair cables (e.g., CAT5, CAT6) and fiber optic cables. Twisted pair cables are more affordable and suitable for shorter distances, while fiber optic cables offer higher bandwidth and are used for longer distances or in environments with electromagnetic interference.
Q.4: How does Ethernet differ from Wi-Fi?
Answer:
Ethernet uses physical cables to establish a wired connection between devices, while Wi-Fi uses wireless signals for communication. Ethernet generally offers faster and more stable connections compared to Wi-Fi, but it requires physical cable connections to each device.
Q.5:What is the maximum distance supported by Ethernet cables?
Answer:
The maximum distance supported by Ethernet cables depends on the type of cable and the Ethernet standard being used. For twisted pair cables like CAT5e or CAT6, the maximum distance is typically 100 meters (328 feet). Fiber optic cables can support much longer distances, ranging from a few hundred meters to several kilometers, depending on the specific type of fiber and equipment used.
Share your thoughts in the comments
Please Login to comment...