Collision Detection in CSMA/CD
Last Updated :
24 Mar, 2023
CSMA/CD (Carrier Sense Multiple Access/ Collision Detection) is a media access control method that was widely used in Early Ethernet technology/LANs when there used to be shared Bus Topology and each node ( Computers) were connected By Coaxial Cables. Now a Days Ethernet is Full Duplex and Topology is either Star (connected via Switch or Router) or Point to Point ( Direct Connection). Hence CSMA/CD is not used but they are still supported though.
Consider a scenario where there are ‘n’ stations on a link and all are waiting to transfer data through that channel. In this case, all ‘n’ stations would want to access the link/channel to transfer their own data. The problem arises when more than one station transmits the data at the moment. In this case, there will be collisions in the data from different stations.
CSMA/CD is one such technique where different stations that follow this protocol agree on some terms and collision detection measures for effective transmission. This protocol decides which station will transmit when so that data reaches the destination without corruption.
How CSMA/CD works?
- Step 1: Check if the sender is ready for transmitting data packets.
- Step 2: Check if the transmission link is idle.
Sender has to keep on checking if the transmission link/medium is idle. For this, it continuously senses transmissions from other nodes. Sender sends dummy data on the link. If it does not receive any collision signal, this means the link is idle at the moment. If it senses that the carrier is free and there are no collisions, it sends the data. Otherwise, it refrains from sending data.
- Step 3: Transmit the data & check for collisions.
Sender transmits its data on the link. CSMA/CD does not use an ‘acknowledgment’ system. It checks for successful and unsuccessful transmissions through collision signals. During transmission, if a collision signal is received by the node, transmission is stopped. The station then transmits a jam signal onto the link and waits for random time intervals before it resends the frame. After some random time, it again attempts to transfer the data and repeats the above process.
- Step 4: If no collision was detected in propagation, the sender completes its frame transmission and resets the counters.
How does a station know if its data collide?
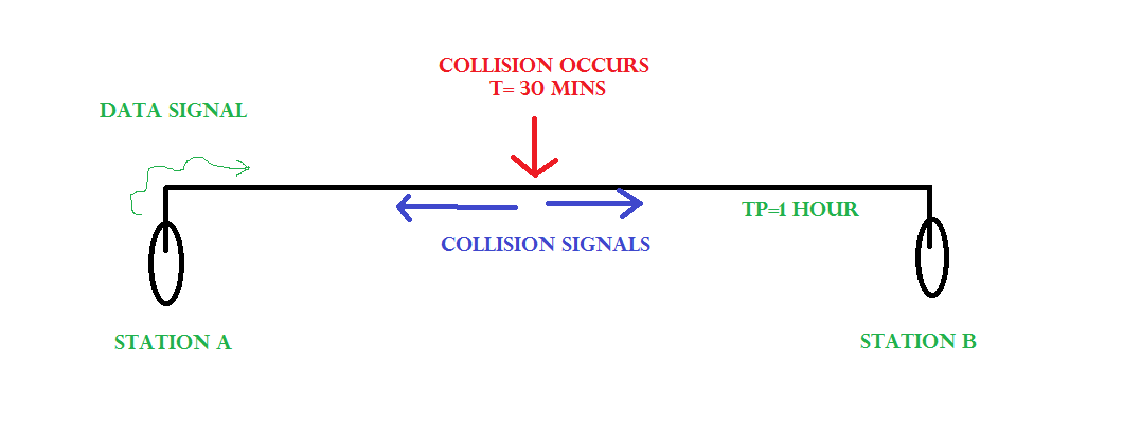
Consider the above situation. Two stations, A & B.
Propagation Time: Tp = 1 hr ( Signal takes 1 hr to go from A to B)
At time t=0, A transmits its data.
t= 30 mins : Collision occurs.
After the collision occurs, a collision signal is generated and sent to both A & B to inform the stations about the collision. Since the collision happened midway, the collision signal also takes 30 minutes to reach A & B.
Therefore, t=1 hr: A & B receive collision signals.
This collision signal is received by all the stations on that link. Then,
How to ensure that it is our station’s data that collided?
For this, Transmission time (Tt) > Propagation Time (Tp) [Rough bound]
This is because we want that before we transmit the last bit of our data from our station, we should at least be sure that some of the bits have already reached their destination. This ensures that the link is not busy and collisions will not occur.
But, above is a loose bound. We have not taken the time taken by the collision signal to travel back to us. For this consider the worst-case scenario.
Consider the above system again.
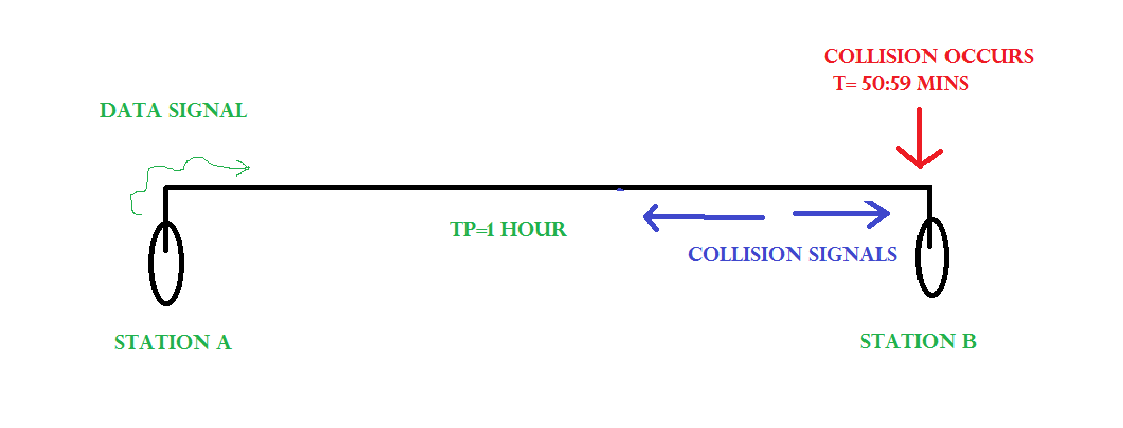
At time t=0, A transmits its data.
t= 59:59 mins : Collision occurs
This collision occurs just before the data reaches B. Now the collision signal takes 59:59 minutes again to reach A. Hence, A receives the collision information approximately after 2 hours, that is, after 2 * Tp.
Hence, to ensure tighter bound, to detect the collision completely,
Tt > >= 2 * Tp
This is the maximum collision time that a system can take to detect if the collision was of its own data.
What should be the minimum length of the packet to be transmitted?
Transmission Time = Tt = Length of the packet/ Bandwidth of the link
[Number of bits transmitted by sender per second]
Substituting above, we get,
Length of the packet/ Bandwidth of the link>= 2 * Tp
Length of the packet >= 2 * Tp * Bandwidth of the link
Padding helps in cases where we do not have such long packets. We can pad extra characters to the end of our data to satisfy the above condition.
Collision detection in CSMA/CD involves the following features:
- Carrier sense: Before transmitting data, a device listens to the network to check if the transmission medium is free. If the medium is busy, the device waits until it becomes free before transmitting data.
- Multiple Access: In a CSMA/CD network, multiple devices share the same transmission medium. Each device has equal access to the medium, and any device can transmit data when the medium is free.
- Collision detection: If two or more devices transmit data simultaneously, a collision occurs. When a device detects a collision, it immediately stops transmitting and sends a jam signal to inform all other devices on the network of the collision. The devices then wait for a random time before attempting to transmit again, to reduce the chances of another collision.
- Backoff algorithm: In CSMA/CD, a backoff algorithm is used to determine when a device can retransmit data after a collision. The algorithm uses a random delay before a device retransmits data, to reduce the likelihood of another collision occurring.
- Minimum frame size: CSMA/CD requires a minimum frame size to ensure that all devices have enough time to detect a collision before the transmission ends. If a frame is too short, a device may not detect a collision and continue transmitting, leading to data corruption on the network.
Advantages of CSMA/CD:
- Simple and widely used: CSMA/CD is a widely used protocol for Ethernet networks, and its simplicity makes it easy to implement and use.
Fairness: In a CSMA/CD network, all devices have equal access to the transmission medium, which ensures fairness in data transmission.
Efficiency: CSMA/CD allows for efficient use of the transmission medium by preventing unnecessary collisions and reducing network congestion.
Disadvantages of CSMA/CD:
- Limited scalability: CSMA/CD has limitations in terms of scalability, and it may not be suitable for large networks with a high number of devices.
Vulnerability to collisions: While CSMA/CD can detect collisions, it cannot prevent them from occurring. Collisions can lead to data corruption, retransmission delays, and reduced network performance.
Inefficient use of bandwidth: CSMA/CD uses a random backoff algorithm that can result in inefficient use of network bandwidth if a device continually experiences collisions.
Susceptibility to security attacks: CSMA/CD does not provide any security features, and the protocol is vulnerable to security attacks such as packet sniffing and spoofing.
Read next – Efficiency of CSMA/CD
Share your thoughts in the comments
Please Login to comment...