TELNET and SSH in Cisco devices
Last Updated :
17 Nov, 2022
We can take access to a cisco router or switch either through a console cable or taking remote access through well known protocols Telnet or ssh (Secure Shell). Telnet and ssh are both application layer protocols used to take remote access and manage a device. 1. Telnet: As stated, Telnet is an application layer protocol which uses TCP port number 23, used to take remote access of a device. Features –
- It doesn’t support authentication.
- Data is sent in clear text therefore less secure.
- No encryption mechanism is used.
- Designed to work in local networks only.
Configuration – 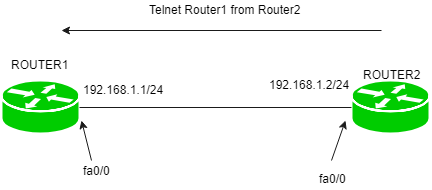 There is a simple topology in which two routers are directly connected to each other namely Router1 and Router2. Router1 have IP address 192.168.1.1/24 on its fa0/0 port and Router2 has IP address 192.168.1.2/24 on its fa0/0 port. Here, we will enable telnet on Router1 and take access through Router2. Configuring telnet on Router1:
There is a simple topology in which two routers are directly connected to each other namely Router1 and Router2. Router1 have IP address 192.168.1.1/24 on its fa0/0 port and Router2 has IP address 192.168.1.2/24 on its fa0/0 port. Here, we will enable telnet on Router1 and take access through Router2. Configuring telnet on Router1:
Router1(config)#line vty 0 4
Router1(config-line)#password GeeksforGeeks
Router1(config-line)#exit
Here, 0 4 means that we can have 5 concurrent sessions at a time. Taking access through Router2:
Router2#telnet 192.168.1.1
Router1>
Note – On Cisco devices, if you want to take access of a device, you have to use vty lines for it. Troubleshooting – While using telnet or ssh, keep these things in mind:
- The (client) device through which you want to take access should be reachable to the (server) device you want to take access.
Note – AAA services can also be used to set password on line vty lines. Either a local database of a device (router) or ACS server can be used for the password for vty lines. But here we are talking about a simple configuration only. 2. Secure Shell (SSH): SSH is also an application client-server protocol used to take remote access of a device. It uses TCP port number 23. Features –
- Unlike telnet, it provides authentication methods.
- The data sent is in encrypted form.
- It is designed to work in public network.
- It uses public key for encryption mechanism.
In short, SSH is more secure than telnet and has almost replaced telnet. Configuration –  We are using the same simple topology. Router1 have IP address 192.168.1.1/24 on its fa0/0 port and Router2 has IP address 192.168.1.2/24 on its fa0/0 port. We will ssh Router1 from Router2 Configuring ssh on Router1.
We are using the same simple topology. Router1 have IP address 192.168.1.1/24 on its fa0/0 port and Router2 has IP address 192.168.1.2/24 on its fa0/0 port. We will ssh Router1 from Router2 Configuring ssh on Router1.
Router(config)#ip domain-name GeeksforGeeks.com
Router(config)#hostname Router1
Router1(config)#line vty 0 4
Router1(config-line)#transport input ssh
Router1(config-line)password GeeksforGeeks
Router1(config-line)#login
Router1(config)#crypto key generate rsa label Cisco modulus 1024
Here, note that it is necessary to give domain name as ssh uses it and password for encryption purpose.If domain-name and hostname are not provided then crypto keys will not be generated. We have provided a password for vty line login and at last we have created key of 1024 bytes and labelled it as Cisco. Note – The last command “crypto key generate rsa label Cisco modulus 1024” will be executed only if your router supports security features like router 3700. If this command is not supported type command:
Router1(config)#line vty 0 4
Router1(config-line)#crypto key generate rsa
After this, it will ask for the size of which you want to generate your key so type 512 or 1024 Now, we will try to ssh from Router2 to Router1.
Router2#ssh -l Cisco 192.168.1.1
Here, -l means login which is followed by the username and then the IP address of the device which we want to take remote access. Troubleshooting – While configuring ssh, take these things into consideration:
- Domain name and hostname should be provided.
- Crypto keys should be generated
- Password on the vty line should be provided (i.e no local database is used).
Note – If using local database of the router i.e username and password configured on router locally and not on vty lines then login local command will be used.
Router1(config-line)#login local
Share your thoughts in the comments
Please Login to comment...