Protocol and Standard in Computer Networks
Last Updated :
08 Apr, 2024
Computer networks depend on protocols and standards, which play a vital role, in enabling communication between different devices and systems that share data consistently. Network protocol ensures that different technologies and components of the network are compatible with one another, reliable, and able to function together. In this article, we are going to discuss every point about protocols and standards in computer networks.
What is Protocol?
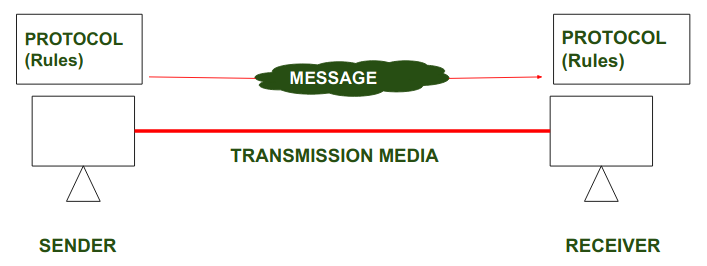
To make communication successful between devices, some rules and procedures should be agreed upon at the sending and receiving ends of the system. Such rules and procedures are called Protocols. Different types of protocols are used for different types of communication.
Protocols
In the above diagrams, Protocols are shown as a set of rules. Such that Communication between the Sender and Receiver is not possible without Protocol.
Key Element of Protocol
- Syntax: Syntax refers to the structure or the format of the data that gets exchanged between the devices. Syntax of the message includes the type of data, composition of the message, and sequencing of the message. The starting 8 bits of data are considered as the address of the sender. The next 8 bits are considered to be the address of the receiver. The remaining bits are considered as the message itself.
- Semantics: Semantics defines data transmitted between devices. It provides rules and norms for understanding message or data element values and actions.
- Timing: Timing refers to the synchronization and coordination between devices while transferring the data. Timing ensures at what time data should be sent and how fast data can be sent. For example, If a sender sends 100 Mbps but the receiver can only handle 1 Mbps, the receiver will overflow and lose data. Timing ensures preventing of data loss, collisions, and other timing-related issues.
- Sequence control: Sequence control ensures the proper ordering of data packets. The main responsibility of sequence control is to acknowledge the data while it get received, and the retransmission of lost data. Through this mechanism, the data is delivered in correct order.
- Flow Control: Flow control regulates device data delivery. It limits the sender’s data or asks the receiver if it’s ready for more. Flow control prevents data congestion and loss.
- Error Control: Error control mechanisms detect and fix data transmission faults. They include error detection codes, data resend, and error recovery. Error control detects and corrects noise, interference, and other problems to maintain data integrity.
- Security : Network security protects data confidentiality, integrity, and authenticity. which includes encryption, authentication, access control, and other security procedures. Network communication’s privacy and trustworthiness are protected by security standards.
Types of Protocol
- Network Layer Protocols : Network layer protocols operate in the network layer which is also known as the Layer 3 of the network architecture. Network layer protocols are responsible for packet routing, forwarding, and addressing of data packets throughout the network. IP and ICMP are the network layer protocols.
- Transport layer Protocols: Transport layer protocols work in the transport layer which provides end-to-end service ensuring data transfer across apps on different devices. TCP and UDP are the most popular transport layer protocols.
- Application Layer Protocol: Application layer protocol working in the application layer of the network architecture provides communication between applications running on different devices. The application layer protocols enable cross-device communication. They format, exchange, and interpret application data. HTTP, FTP, and SMTP are examples.
- Wireless Protocols: Wireless protocols basically used in wireless communication which enables data transfer through wireless networks. Bluetooth, Wi-Fi, and LTE protocols are examples.
- Routing Protocols: Routing protocol establishes the best/optimal network pathways throughout the network for fastest data transmission. Routers share information to develop and maintain routing tables. RIP, OSPF, and BGP are examples.
- Security Protocols : security protocol protects data confidentiality, integrity, and authenticity while transmission of data over the network. They include SSL and TLS, encryption methods, and authentication protocols for providing data security.
- Internet Protocols : IP identifies devices uniquely. Internet protocol provides data communication through routing and forwarding data packets from one device to another by unique addressing scheme.
What is Standards?
Standards are the set of rules for data communication that are needed for the exchange of information among devices. It is important to follow Standards which are created by various Standard Organizations like IEEE, ISO, ANSI, etc.
Types of Standards
- De Facto Standard: The meaning of the work ” De Facto ” is ” By Fact ” or “By Convention”.These are the standards that have not been approved by any Organization but have been adopted as Standards because of their widespread use. Also, sometimes these standards are often established by Manufacturers.
For example : Apple and Google are two companies that established their own rules for their products which are different. Also, they use some same standard rules for manufacturing their products.
- De Jure Standard: The meaning of the word “De Jure” is “By Law” or “By Regulations”.Thus, these are the standards that have been approved by officially recognized bodies like ANSI, ISO, IEEE, etc. These are the standards that are important to follow if it is required or needed.
For example : All the data communication standard protocols like SMTP, TCP, IP, UDP etc. are important to follow the same when we need them.
Protocol and Standard Compliance in Network Security
- Interoperability: Protocols and standards allow devices and systems to communicate. These protocols ensure network components can function together, avoiding risks and security gaps produced by incompatible or unsupported systems.
- Security Baseline : Protocols and standards contain security principles and best practices that help secure network infrastructure. These protocols allow organizations to protect sensitive data via encryption, authentication, and access controls.
- Vulnerability Management : Network security protocols and standards help organizations find and fix vulnerabilities. Many standards requires regular security assessments, vulnerability scanning, and penetration testing to discover network infrastructure flaws. Organizations can prevent cyberattacks and address vulnerabilities by following these compliance criteria.
Best Practices for Ensuring Protocol and Standard Compliance
- Use cryptography tools to secure personal data transported across your network, making sure that data encryption methods exceed industry requirements.
- Perform frequent security checks on all network devices to discover vulnerabilities and verify they fulfil compliance standards.
- Restrict user access to specified network zones to ensure secure data sharing and prevent unauthorized access.
Conclusion
Protocols and standards enable secure and efficient computer network communication. They regulate data exchange, formatting, endpoints, and reliable device communication. These protocols and standards ensure network security and performance. Compliance can prevent data breaches and system breakdowns.
Frequently Asked Question on Protocol and Standards – FAQs
What is the role of organizations like the IEEE and the IETF in protocol development?
Organizations such as the IEEE and the IETF play important roles in defining and maintaining networking protocols and standards. They provide platforms for experts to cooperate, analyze suggestions, and reach agreements on new protocols or changes to current ones.
Why are protocols and standards important in networking?
Protocols and standards ensure that devices from multiple companies may communicate with one another effectively. They also contribute to consistent and reliable data transfer, resulting in efficient networking operations.
What are some common networking protocols?
How do protocols ensure data integrity and security?
Protocols usually include systems for error detection, correction, and encryption to assure data integrity and security during transmission. TCP, for example, uses sequence numbers and acknowledgment messages to ensure that data is delivered reliably.
Share your thoughts in the comments
Please Login to comment...