Carrier Sense Multiple Access (CSMA)
Last Updated :
25 Jun, 2023
This method was developed to decrease the chances of collisions when two or more stations start sending their signals over the data link layer. Carrier Sense multiple access requires that each station first check the state of the medium before sending.
Prerequisite - Multiple Access Protocols
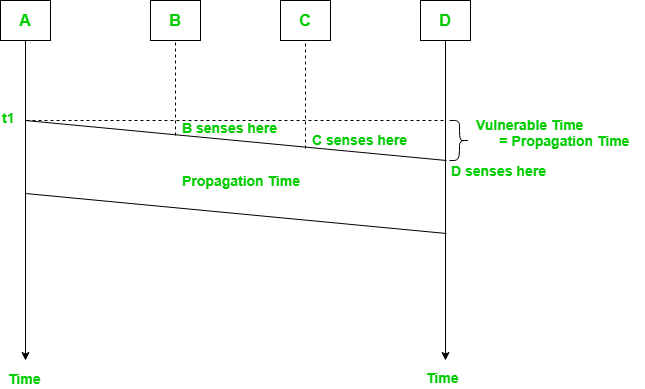
Vulnerable Time:
Vulnerable time = Propagation time (Tp)
The persistence methods can be applied to help the station take action when the channel is busy/idle.
1. Carrier Sense Multiple Access with Collision Detection (CSMA/CD):
In this method, a station monitors the medium after it sends a frame to see if the transmission was successful. If successful, the transmission is finished, if not, the frame is sent again.
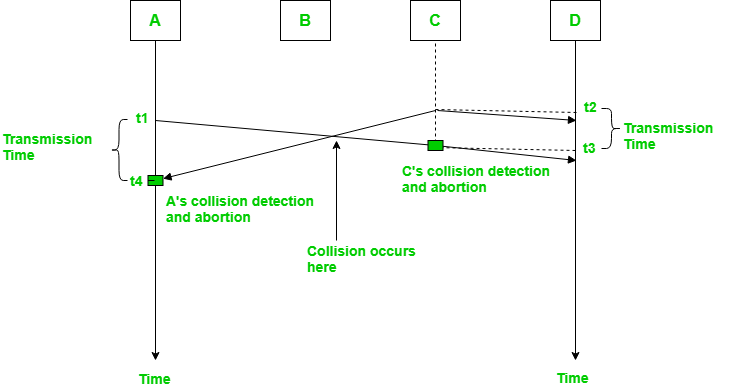
In the diagram, starts sending the first bit of its frame at t1 and since C sees the channel idle at t2, starts sending its frame at t2. C detects A’s frame at t3 and aborts transmission. A detects C’s frame at t4 and aborts its transmission. Transmission time for C’s frame is, therefore, t3-t2 and for A’s frame is t4-t1
So, the frame transmission time (Tfr) should be at least twice the maximum propagation time (Tp). This can be deduced when the two stations involved in a collision are a maximum distance apart.
Process: The entire process of collision detection can be explained as follows:
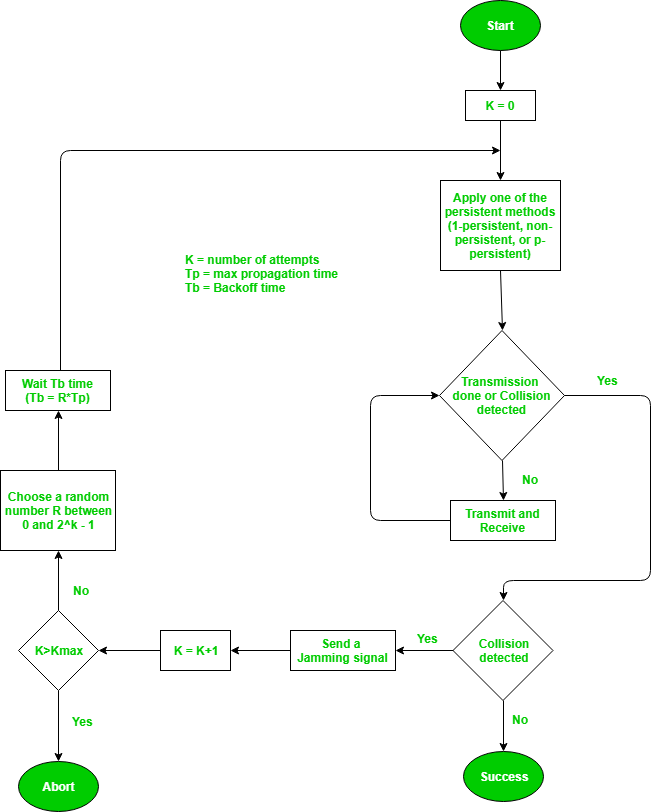
Throughput and Efficiency: The throughput of CSMA/CD is much greater than pure or slotted ALOHA.
- For the 1-persistent method, throughput is 50% when G=1.
- For the non-persistent method, throughput can go up to 90%.
2. Carrier Sense Multiple Access with Collision Avoidance (CSMA/CA) –
The basic idea behind CSMA/CA is that the station should be able to receive while transmitting to detect a collision from different stations. In wired networks, if a collision has occurred then the energy of the received signal almost doubles, and the station can sense the possibility of collision. In the case of wireless networks, most of the energy is used for transmission, and the energy of the received signal increases by only 5-10% if a collision occurs. It can’t be used by the station to sense collision. Therefore CSMA/CA has been specially designed for wireless networks.
These are three types of strategies:
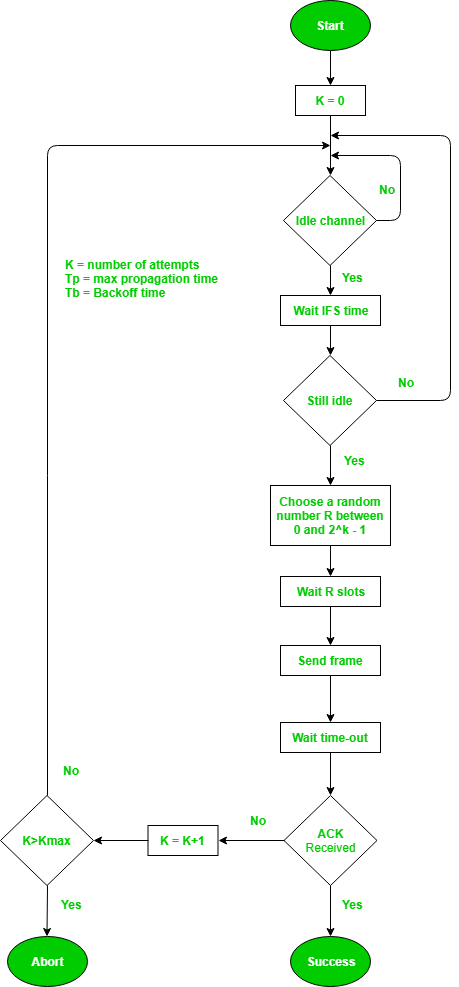
- InterFrame Space (IFS): When a station finds the channel busy it senses the channel again, when the station finds a channel to be idle it waits for a period of time called IFS time. IFS can also be used to define the priority of a station or a frame. Higher the IFS lower is the priority.
- Contention Window: It is the amount of time divided into slots. A station that is ready to send frames chooses a random number of slots as wait time.
- Acknowledgments: The positive acknowledgments and time-out timer can help guarantee a successful transmission of the frame.
Characteristics of CSMA/CA :
- Carrier Sense: The device listens to the channel before transmitting, to ensure that it is not currently in use by another device.
- Multiple Access: Multiple devices share the same channel and can transmit simultaneously.
- Collision Avoidance: If two or more devices attempt to transmit at the same time, a collision occurs. CSMA/CA uses random backoff time intervals to avoid collisions.
- Acknowledgment (ACK): After successful transmission, the receiving device sends an ACK to confirm receipt.
- Fairness: The protocol ensures that all devices have equal access to the channel and no single device monopolizes it.
- Binary Exponential Backoff: If a collision occurs, the device waits for a random period of time before attempting to retransmit. The backoff time increases exponentially with each retransmission attempt.
- Interframe Spacing: The protocol requires a minimum amount of time between transmissions to allow the channel to be clear and reduce the likelihood of collisions.
- RTS/CTS Handshake: In some implementations, a Request-To-Send (RTS) and Clear-To-Send (CTS) handshake is used to reserve the channel before transmission. This reduces the chance of collisions and increases efficiency.
- Wireless Network Quality: The performance of CSMA/CA is greatly influenced by the quality of the wireless network, such as the strength of the signal, interference, and network congestion.
- Adaptive Behavior: CSMA/CA can dynamically adjust its behavior in response to changes in network conditions, ensuring the efficient use of the channel and avoiding congestion.
Overall, CSMA/CA balances the need for efficient use of the shared channel with the need to avoid collisions, leading to reliable and fair communication in a wireless network.
Process: The entire process of collision avoidance can be explained as follows:
Types of CSMA Access Modes:
There are 4 types of access modes available in CSMA. It is also referred as 4 different types of CSMA protocols which decide the time to start sending data across shared media.
- 1-Persistent: It senses the shared channel first and delivers the data right away if the channel is idle. If not, it must wait and continuously track for the channel to become idle and then broadcast the frame without condition as soon as it does. It is an aggressive transmission algorithm.
- Non-Persistent: It first assesses the channel before transmitting data; if the channel is idle, the node transmits data right away. If not, the station must wait for an arbitrary amount of time (not continuously), and when it discovers the channel is empty, it sends the frames.
- P-Persistent: It consists of the 1-Persistent and Non-Persistent modes combined. Each node observes the channel in the 1Persistent mode, and if the channel is idle, it sends a frame with a P probability. If the data is not transferred, the frame restarts with the following time slot after waiting for a (q = 1-p probability) random period.
- O-Persistent: A supervisory node gives each node a transmission order. Nodes wait for their time slot according to their allocated transmission sequence when the transmission medium is idle.
Advantages of CSMA:
- Increased efficiency: CSMA ensures that only one device communicates on the network at a time, reducing collisions and improving network efficiency.
- Simplicity: CSMA is a simple protocol that is easy to implement and does not require complex hardware or software.
- Flexibility: CSMA is a flexible protocol that can be used in a wide range of network environments, including wired and wireless networks.
- Low cost: CSMA does not require expensive hardware or software, making it a cost-effective solution for network communication.
Disadvantages of CSMA:
- Limited scalability: CSMA is not a scalable protocol and can become inefficient as the number of devices on the network increases.
- Delay: In busy networks, the requirement to sense the medium and wait for an available channel can result in delays and increased latency.
- Limited reliability: CSMA can be affected by interference, noise, and other factors, resulting in unreliable communication.
- Vulnerability to attacks: CSMA can be vulnerable to certain types of attacks, such as jamming and denial-of-service attacks, which can disrupt network communication.
Comparisonof various protocols:
| Protocol |
Transmission behavior |
Collision detection method |
Efficiency |
Use cases |
| Pure ALOHA |
Sends frames immediately |
No collision detection |
Low |
Low-traffic networks
|
| Slotted ALOHA |
Sends frames at specific time slots |
No collision detection |
Better than pure ALOHA |
Low-traffic networks
|
| CSMA/CD |
Monitors medium after sending a frame, retransmits if necessary |
Collision detection by monitoring transmissions |
High |
Wired networks with moderate to high traffic |
| CSMA/CA |
Monitors medium while transmitting, adjusts behavior to avoid collisions |
Collision avoidance through random backoff time intervals |
High |
Wireless networks with moderate to high traffic and high error rates |
Share your thoughts in the comments
Please Login to comment...