What is Proxy Server?
Last Updated :
31 Jan, 2024
A proxy server refers to a server that acts as an intermediary between the request made by clients, and a particular server for some services or requests for some resources. There are different types of proxy servers available that are put into use according to the purpose of a request made by the clients to the servers. The basic purpose of Proxy servers is to protect the direct connection of Internet clients and Internet resources. There are many Proxy providers in the market that provide services to both individuals and businesses.
For example, Smartproxy has been offering unique solutions for online anonymity and web data collection since 2018. It has a 55M+ residential proxy pool that opens horizons for block-free web scraping and geo-targeting. They provide access to 195+ locations worldwide, including city-level and 50 US states targeting You can check out Smartproxy’s official website to uncover more of its unique features.
The proxy server also prevents the identification of the client’s IP address when the client makes any request to any other servers.
- Internet Client and Internet resources: For Internet clients, Proxy servers also act as a shield for an internal network against the request coming from a client to access the data stored on the server. It makes the original IP address of the node remain hidden while accessing data from that server.
- Protects true host identity: In this method, outgoing traffic appears to come from the proxy server rather than internet navigation. It must be configured to a specific application such as HTTP or FTP. For example, organizations can use a proxy to observe the traffic of their employees to get the work efficiently done. It can also be used to keep a check on any kind of highly confidential data leakage. Some can also use it to increase their website rank.
Need Of Private Proxy
- Defeat Hackers: To protect an organization’s data from malicious use, passwords are used and different architects are set up, but still, there may be a possibility that this information can be hacked in case the IP address is accessible easily. To prevent such kind of misuse of Data Proxy servers are set up to prevent tracking of original IP addresses instead data is shown to come from a different IP address.
- Filtering of Content: By caching the content of the websites, Proxy helps in fast access to the data that has been accessed very often.
- Examine Packet Headers and Payloads: Payloads and packet headers of the requests made by the user nodes in the internal server to access social websites can be easily tracked and restricted.
- To control internet usage of employees and children: In this, the Proxy server is used to control and monitor how their employees or kids use the internet. Organizations use it, to deny access to a specific website and instead redirecting you with a nice note asking you to refrain from looking at said sites on the company network.
- Bandwidth savings and improved speeds: Proxy helps organizations to get better overall network performance with a good proxy server.
- Privacy Benefits: Proxy servers are used to browse the internet more privately. It will change the IP address and identify the information the web request contains.
- Security: Proxy server is used to encrypt your web requests to keep prying eyes from reading your transactions as it provides top-level security.
Types Of Proxy Server
- Reverse Proxy Server: The job of a reverse proxy server to listen to the request made by the client and redirect to the particular web server which is present on different servers.
Example – Listen for TCP port 80 website connections which are normally placed in a demilitarized zone (DMZ) zone for publicly accessible services but it also protects the true identity of the host. Moreover, it is transparent to external users as external users will not be able to identify the actual number of internal servers. So, it is the prime duty of reverse proxy to redirect the flow depending upon the configurations of internal servers. The request that is made to pass through the private network protected by firewalls will need a proxy server that is not abiding by any of the local policies. Such types of requests from the clients are completed using reverse proxy servers. This is also used to restrict the access of the clients to the confidential data residing on the particular servers.
- Web Proxy Server: Web Proxy forwards the HTTP requests, only URL is passed instead of a path. The request is sent to particular the proxy server responds. Examples, Apache, HAP Proxy.
- Anonymous Proxy Server: This type of proxy server does not make an original IP address instead these servers are detectable still provides rational anonymity to the client device.
- Highly Anonymity Proxy: This proxy server does not allow the original IP address and it as a proxy server to be detected.
- Transparent Proxy: This type of proxy server is unable to provide any anonymity to the client, instead, the original IP address can be easily detected using this proxy. But it is put into use to act as a cache for the websites. A transparent proxy when combined with gateway results in a proxy server where the connection requests are sent by the client , then IP are redirected. Redirection will occurs without the client IP address configuration. HTTP headers present on the server-side can easily detect its redirection .
- CGI Proxy: CGI proxy server developed to make the websites more accessible. It accepts the requests to target URLs using a web form and after processing its result will be returned to the web browser. It is less popular due to some privacy policies like VPNs but it still receives a lot of requests also. Its usage got reduced due to excessive traffic that can be caused to the website after passing the local filtration and thus leads to damage to the organization.
- Suffix Proxy: Suffix proxy server basically appends the name of the proxy to the URL. This type of proxy doesn’t preserve any higher level of anonymity. It is used for bypassing the web filters. It is easy to use and can be easily implemented but is used less due to the more number of web filter present in it.
- Distorting Proxy: Proxy servers are preferred to generate an incorrect original IP address of clients once being detected as a proxy server. To maintain the confidentiality of the Client IP address HTTP headers are used.
- Tor Onion Proxy: This server aims at online anonymity to the user’s personal information. It is used to route the traffic through various networks present worldwide to arise difficulty in tracking the users’ address and prevent the attack of any anonymous activities. It makes it difficult for any person who is trying to track the original address. In this type of routing, the information is encrypted in a multi-folds layer. At the destination, each layer is decrypted one by one to prevent the information to scramble and receive original content. This software is open-source and free of cost to use.
- 12P Anonymous Proxy: It uses encryption to hide all the communications at various levels. This encrypted data is then relayed through various network routers present at different locations and thus I2P is a fully distributed proxy. This software is free of cost and open source to use, It also resists the censorship.
- DNS Proxy: DNS proxy take requests in the form of DNS queries and forward them to the Domain server where it can also be cached, moreover flow of request can also be redirected.
- Rotating Proxy: A rotating proxy assign a new or different IP address to each user that connects to proxy. As users connect, the unique address is assign to it.
How Does The Proxy Server Operates?
Every computer has its unique IP address which it uses to communicate with another node. Similarly, the proxy server has its IP address that your computer knows. When a web request is sent, your request goes to the proxy server first. The Proxy sends a request on your behalf to the internet and then collect the data and make it available to you. A proxy can change your IP address So, the webserver will be unable to fetch your location in the world. It protects data from getting hacked too. Moreover, it can block some web pages also. 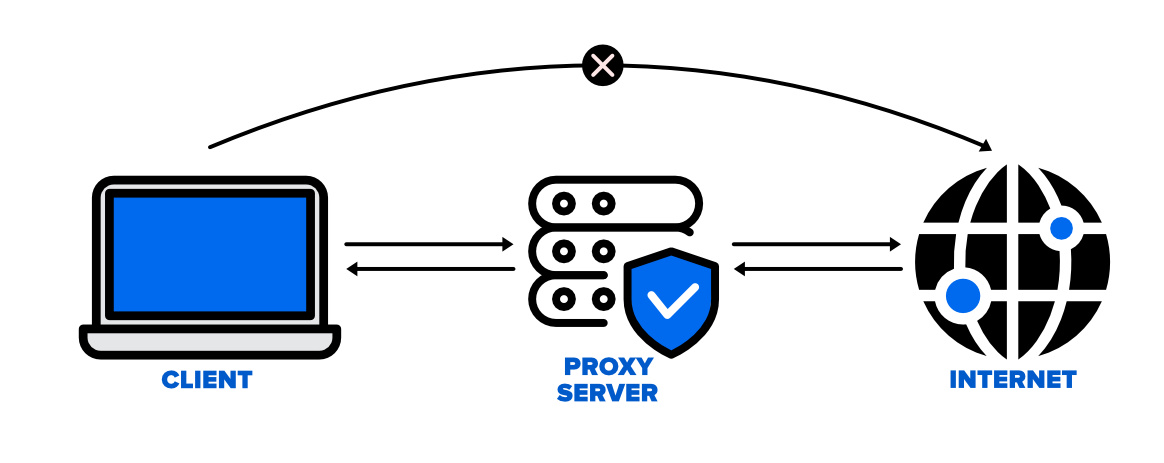
What is the reason of using Proxy Server?
There are some reasons why everyone should proxy server because it provide following advantages including privacy, web scraping, fast speed, saves bandwidth etc.

Proxy Server
Advantages of Proxy Server
Proxy server has multiple benefits like
- Security: Proxy Server provides security between internet and system. They help your system from unauthorized user to access your network
- Saves Bandwidth: A proxy server can save bandwidth, especially in those environments where the same resources are accessed by multiple users.
- Performance: Proxy server improves performance, when a person requests for a resource, then the proxy can serve it from its cache rather than fetching it from the original server this helps to increase performance.
- Filteration: Proxy servers are used to filter content based on keywords or file types.
- Access Control: There are some content which is restricted in various countries, so proxy server helps to control geographical access.
Disadvantages of Proxy Server
- Proxy Server Risks: Free installation does not invest much in backend hardware or encryption. It will result in performance issues and potential data security issues. If you install a “free” proxy server, treat very carefully, some of those might steal your credit card numbers.
- Browsing history log: The proxy server stores your original IP address and web request information is possibly unencrypted form and saved locally. Always check if your proxy server logs and saves that data – and what kind of retention or law enforcement cooperation policies they follow while saving data.
- No encryption: No encryption means you are sending your requests as plain text. Anyone will be able to pull usernames and passwords and account information easily. Keep a check that proxy provides full encryption whenever you use it.
Frequently Asked Question on Proxy Server – FAQs
What is a proxy server?
A proxy server refers to a server that acts as an intermediary between the request made by clients, and a particular server for some services or requests for some resources.
Are proxy Server Secure?
Yes, Proxy Server are very secure they enhance the security of the system.
Can I set up my own proxy?
Yes you ca set up your own proxy but it require server administration skills.
Can we say that VPN is a proxy?
They both are used for the same purpose but they are distinct in term os technology.
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...