Difference between RSA algorithm and DSA
Last Updated :
31 Aug, 2023
1. Rivest-Shamir-Adleman (RSA) algorithm :
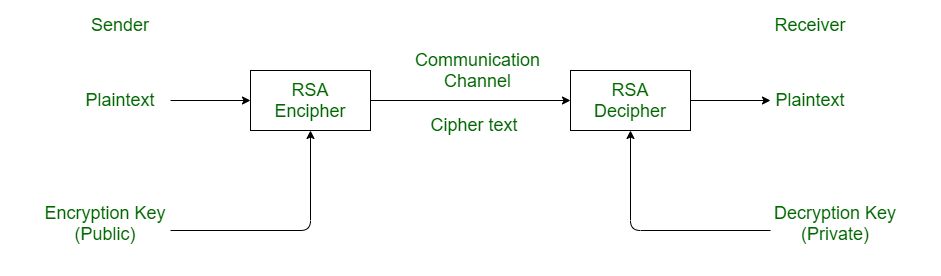
RSA stands for Rivest-Shamir-Adleman. It is a cryptosystem used for secure data transmission. In RSA algorithm, encryption key is public but decryption key is private. This algorithm is based on mathematical fact that factoring the product of two large prime numbers is not easy. It was developed by Ron Rivest, Adi Shamir and Leonard Adleman in 1977.
Here’s an example of how to implement the RSA algorithm in Python:
Python
import random
def is_prime(n):
if n <= 1:
return False
for i in range(2, int(n**0.5) + 1):
if n % i == 0:
return False
return True
def generate_prime(length):
while True:
prime_candidate = random.randint(2**(length-1), 2**length - 1)
if is_prime(prime_candidate):
return prime_candidate
def gcd(a, b):
while b != 0:
a, b = b, a % b
return a
def mod_inverse(a, m):
if gcd(a, m) != 1:
return None
u1, u2, u3 = 1, 0, a
v1, v2, v3 = 0, 1, m
while v3 != 0:
q = u3 // v3
v1, v2, v3, u1, u2, u3 = (
u1 - q * v1,
u2 - q * v2,
u3 - q * v3,
v1,
v2,
v3,
)
return u1 % m
def generate_rsa_keys(key_length):
p = generate_prime(key_length // 2)
q = generate_prime(key_length // 2)
modulus = p * q
phi = (p - 1) * (q - 1)
e = 65537
d = mod_inverse(e, phi)
return (e, modulus), (d, modulus)
def encrypt(message, public_key):
e, modulus = public_key
encrypted = [pow(ord(c), e, modulus) for c in message]
return encrypted
def decrypt(ciphertext, private_key):
d, modulus = private_key
decrypted = [chr(pow(c, d, modulus)) for c in ciphertext]
return ''.join(decrypted)
message = "HELLO"
public_key, private_key = generate_rsa_keys(512)
encrypted_message = encrypt(message, public_key)
decrypted_message = decrypt(encrypted_message, private_key)
print("Original Message:", message)
print("Encrypted Message:", encrypted_message)
print("Decrypted Message:", decrypted_message)
|
This code generates RSA keys, encrypts a message using the public key, and decrypts the ciphertext using the private key. The generate_rsa_keys function generates the public and private keys, encrypt function performs encryption, and decrypt function performs decryption.
Output :
Original Message: HELLO
Encrypted Message: [343, 466, 125, 125, 141]
Decrypted Message: HELLO
In this example, the message “HELLO” is encrypted using the RSA algorithm with a randomly generated public key. The encrypted message is represented as a list of numbers. Then, the ciphertext is decrypted using the corresponding private key, resulting in the original message being retrieved successfully.
2. Digital Signature Algorithm (DSA) :
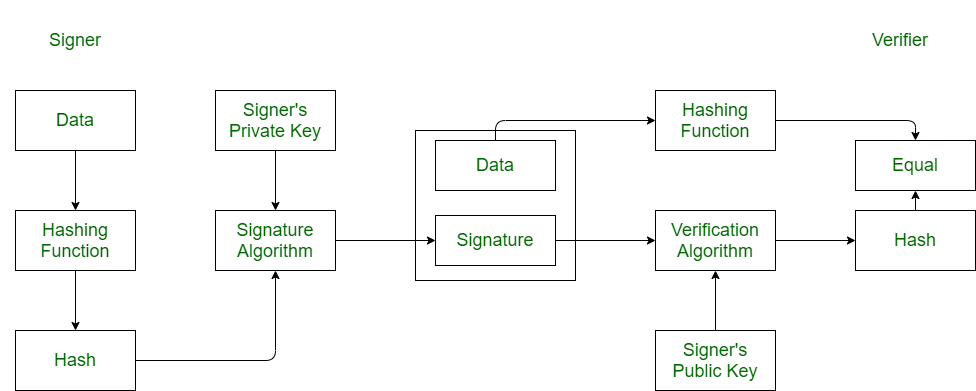
DSA stand for Digital Signature Algorithm. It is used for digital signature and its verification. It is based on mathematical concept of modular exponentiation and discrete logarithm. It was developed by National Institute of Standards and Technology (NIST) in 1991.
It involves four operations:
- Key Generation
- Key Distribution
- Signing
- Signature Verification
Here’s an example of how to implement the DSA (Digital Signature Algorithm) in Python using the ‘cryptography‘ library:
Python
from cryptography.hazmat.primitives import hashes
from cryptography.hazmat.primitives.asymmetric import dsa
from cryptography.hazmat.backends import default_backend
private_key = dsa.generate_private_key(
key_size=1024,
backend=default_backend()
)
public_key = private_key.public_key()
message = b"Hello, world!"
hash_algorithm = hashes.SHA256()
signature = private_key.sign(
message,
algorithm=hash_algorithm
)
try:
public_key.verify(
signature,
message,
algorithm=hash_algorithm
)
print("Signature is valid.")
except:
print("Signature is invalid.")
|
The example showcases the generation of a DSA private key, signing a message using the private key, and verifying the signature using the corresponding public key. Depending on the validity of the signature, it will print either “Signature is valid.” or “Signature is invalid.”
Output :
Signature is valid.
This output indicates that the signature verification was successful, and the signature is valid for the given message and public key.
Difference between RSA algorithm and DSA :
| RSA |
DSA |
| It is a cryptosystem algorithm. |
It is digital signature algorithm. |
| It is used for secure data transmission. |
It is used for digital signature and its verification. |
| It was developed in 1977. |
While it was developed in 1991. |
| It was developed by Ron Rivest, Adi Shamir and Leonard Adleman. |
It was developed by National Institute of Standards and Technology (NIST). |
| It uses mathematical concept of factorization of product of two large primes. |
It uses modular exponentiation and discrete logarithm. |
| It is slower in key generation. |
While it is faster in key generation as compared to RSA. |
| It is faster than DSA in encryption. |
While it is slower in encryption. |
| It is slower in decryption. |
While it is faster in decryption. |
| It is best suited for verification and encryption. |
It is best suited for signing in and decryption. |
Share your thoughts in the comments
Please Login to comment...