Configuring Port Security on Cisco IOS Switch
Last Updated :
06 Sep, 2021
Overview :
Switch is a network device, which is configured to connect and maintain communication channel between various devices. Ethernet ports are present on a switch, which are used to connect devices, such as Router, computer system and Laptop in the network. To connect all these network, Ethernet cables are used. MAC address of these connected devices is used by switch to identify them and provide them with the requested service. It is a crucial task to secure these ports, so that only authorized users are able to connect their systems into the network through a switch. Before configuration of any switch in an organizational network, port security is considered, as it ensures that authentic and authorized user is connected within the network. This security feature of Cisco IOS Switches can only be configured on access ports and by default, this feature is disabled.
Enabling Port Security on Cisco Switch :
Below provided steps and commands can be used to enable Port Security on Cisco Switch, which ensures that data confidentiality, authenticity and integrity is maintained.
Configuration-1 :
Configuration of Port Security –
Step-1 :
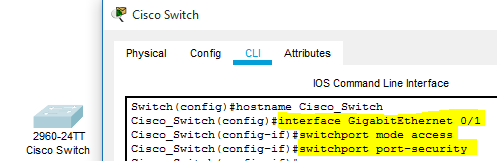
At first, Command Line Interface of Cisco switch is accessed and a port Gigabit Ethernet 0/1 is interfaced using ‘interface Gigabit Ethernet 0/1’ command. Then, ‘switchport mode access’ and ‘switchport port-security’ commands are executed to change the port mode to access and enable security respectively. These commands must be executed, whenever any other port is interfaced and port security needs to be enabled on it.
Step-2 :
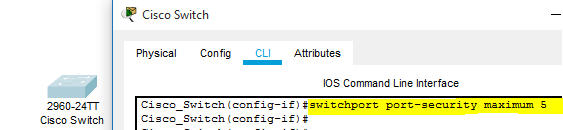
By default, only 1 MAC address is allowed by the Cisco switch on a single port and if any other device tries to connect using that port, switch automatically shutdown its port to restrict unauthorized access. To increase the number of users on a single port, ‘switchport port-security maximum 5’ command is executed. By this, now five devices can be connected to a port and perform their functions.
Step-3 :
Cisco IOS Switch offers a security feature, which is known as violation. This feature is used to define the action, which will be executed by switch, whenever port security is violated. Three primary predefined modes can be used, which are Protect, Restrict and Shutdown.
- Protect Mode –
Under this mode, data packets from defined MAC addresses are only transferred within the network.
- Restrict Mode –
When this mode is enabled and port security is violated, all the data transfer is blocked and packets are dropped. Also, logs are generated simultaneously, to check, which device was connected with Cisco switch.
- Shutdown mode –
This mode is enabled by default and port state is changed to error-disabled, which restricts connected device to perform any function and also disables that particular port.

Configuration of predefined security violation mode
Configuration-2 :
MAC Address Port Security –
Step-1 :
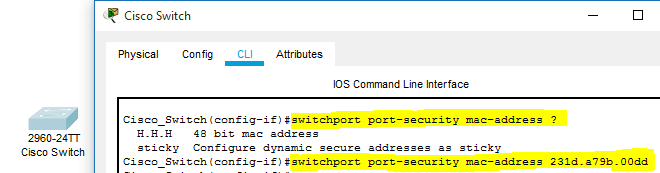
To allow only device with defined MAC address to connect with Cisco Switch ‘switchport port-security mac-address mac_address_of_device’ command can be used. With successful execution of this command, device with specified MAC address will only be authorized by switch to connect through available ethernet port.
Step-2 :
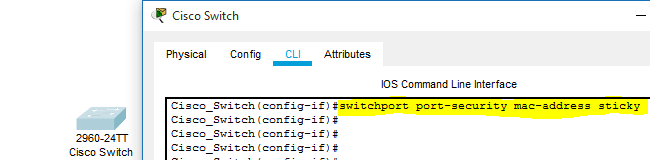
Another mode of mac address command is known as sticky. This mode is enabled to allow switch to learn new MAC addresses and store it in the memory. MAC address of connected device is automatically gathered and stored by the switch.
Configuration-3 :
Check Port Security Configuration –
Step-1 :
To check and analyze the port security configuration on switch, user needs to access privilege mode of the command line interface. ‘show port-security address’ command is executed to check the current port security status.

Command to check status of Port Security
Step-2 :
If the user wants to check port security of a specific interface available on switch, then ‘show port-security interface interface_name’ command can be used.
Step-3 :
In this scenario, security on GigabitEthernet interface is configured and executed command is below displayed for reference.

Port Security Status of a specific port
Share your thoughts in the comments
Please Login to comment...