Logcheck Tool – Monitor Kali Linux System Log Activity
Last Updated :
03 Nov, 2022
Logcheck is a package or tool to check system log files for security violations and unusual activity, it utilizes the program called logtail remembering the last position is read from the log file. Analyzes security or unusual activity from syslog to monitor Apache log files for errors caused by PHP Scripts. Logcheck is used to detect problems automatically in logfiles and results are sent via e-mail. It runs as cronjob off the hour and after every reboot
The tool has three modes of filtering:
- Server: Default level containing different daemons
- Paranoid: High-security machines run as service in this level also it is verbose.
- Workstation: Level for Sheltered machines, filtering messages.
Logcheck Installation:
The logcheck package/repository is already installed in Ubuntu/Debian distribution, just use the apt-get command to install Logcheck in Linux then it will automatically start the downloading process and dependencies.
$ apt-get install logcheck
An alternative method to install this is by downloading logcheck-1.1.12.tar.gz version and then installing the logcheck tool by using tar xvf command.
tar xvf logcheck-1.1.12.tar.gz
cd logcheck-1.1.12
make
make install
We can directly use the logcheck from the terminal without installation with the help of sudo or us by which we can change the user ID and also checks the logfiles without offset being updated.
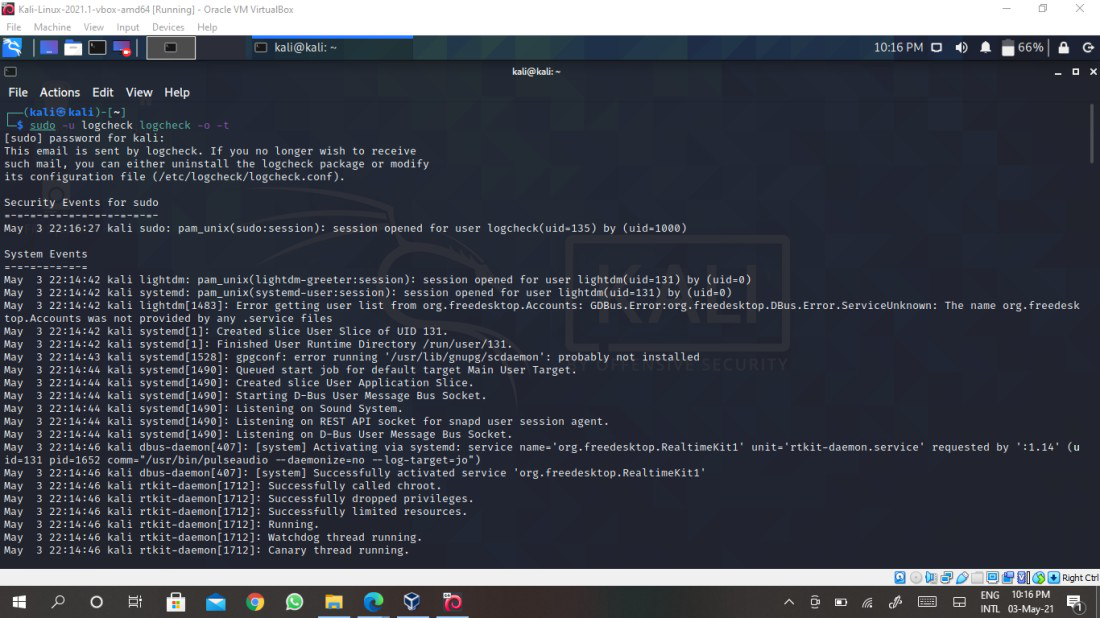
Parameters used here are described as follows,
- -u – syslog summary enabling
- -o – STDOUT mode, not sending mail
- -t – Testing mode does not update offset
$ sudo -u logcheck logcheck -o -t
Configuration:
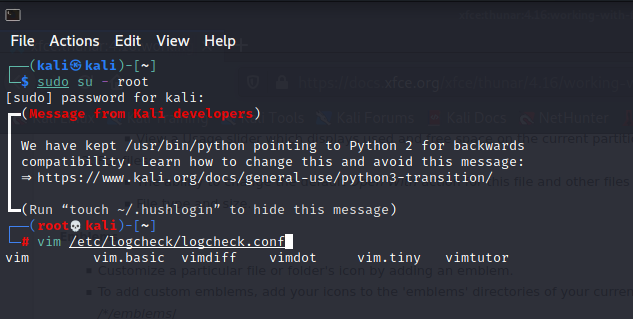
Let’s now look at the configuration file logcheck.conf of logcheck located in /etc/logcheck directory and make the necessary changes in the file.
$ vim /etc/logcheck/logcheck.conf
Change the value for REPORTLEVEL of your choice of level for controlling level of filtering of logs, then change the value SENDMAILTO to your e-mail address, so you can receive the reports and logs on the E-mail ID as shown below.
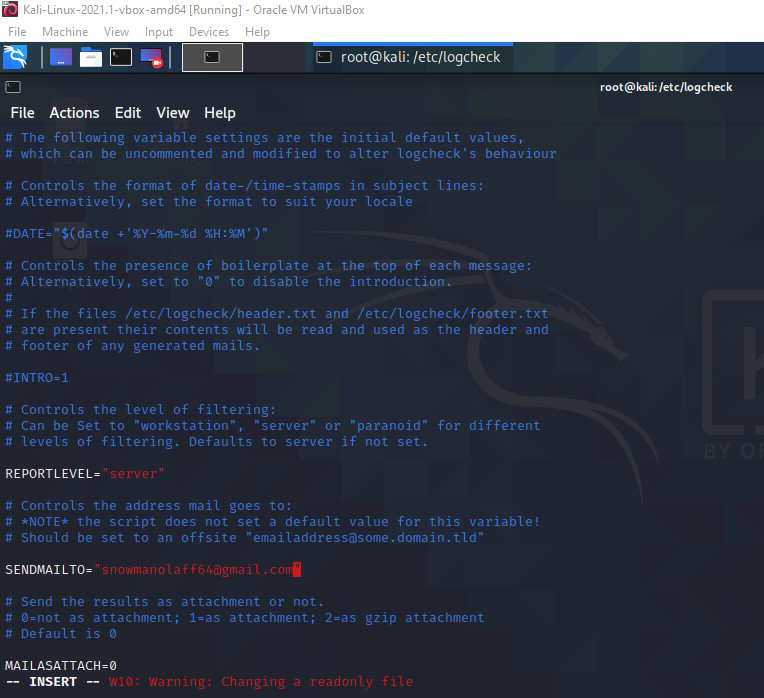
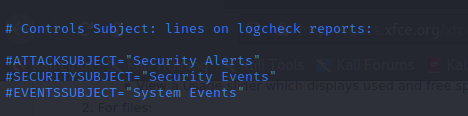
Whenever a mail is generated by logcheck has different subject lines for different events which can also be modified to control the subject.
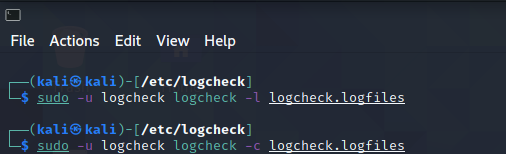
With the help of logfiles stored in /etc/logcheck/logcheck.logfiles for maintaining the list of logfiles that have to be monitored. For defining the list to use another file and in case stored in another location, so to define new PATH modify RULEDIR variable.
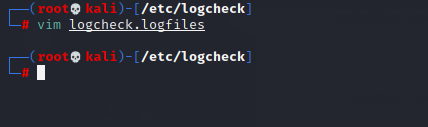
View the configuration files by navigating to /etc/logcheck/logcheck.logfiles or /etc/logcheck/logcheck.files directory for configuring the mail with respect to the report level given by you, these files contain a list of logfiles to be monitored.
# vim logcheck.logfiles
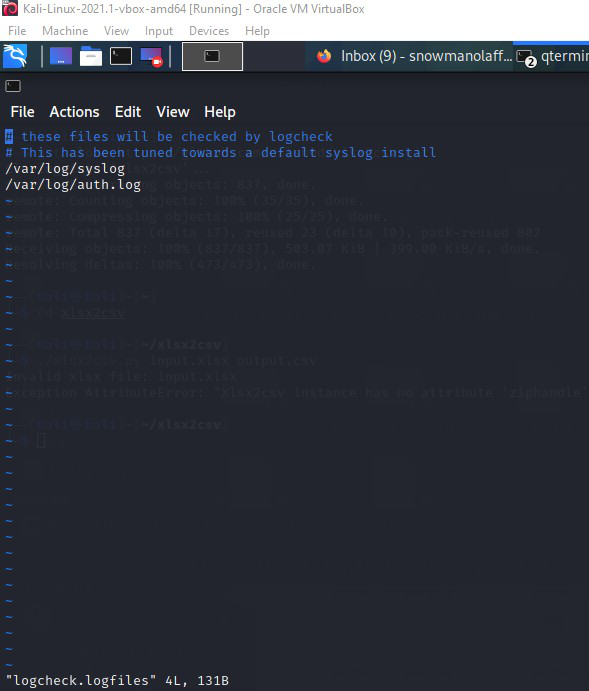
Logcheck works using the files /etc/logcheck/ignore.d.server where it will check for lines that do not match rules in ignore files and then it will include those irregularities in the report which is then sent to the user via e-mail, it also reports unusual activity in log files, hard disk errors, failed authentication attempts and kernel issues.
Usage:
We know that logcheck sends mail only when any suspicious activity is found, but we can also get the reports immediately or on an hourly basis by executing the following command,
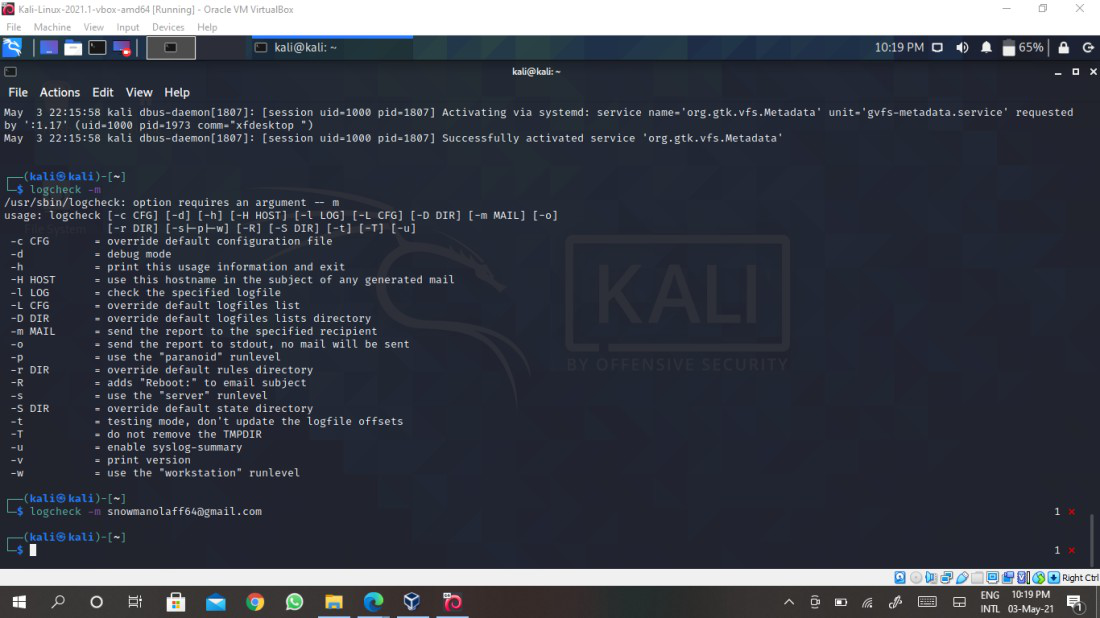
$ logcheck -m
Other parameters to include for sending mail immediately,
- -h – using this we can mention hostname to use it in the subject of the mail
- -o – This option is used to send a report to stdout
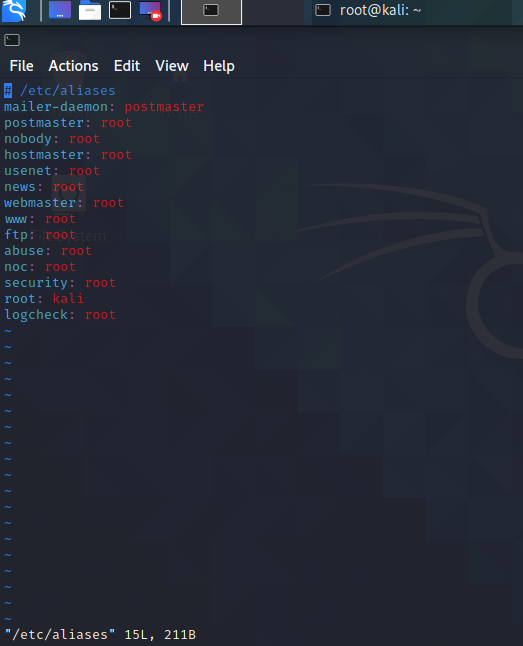
If using a system user it should have valid alias for logcheck and the sender/mailer (mail,sendmail, sSMTP, Postfix) has to be installed,
$ vim /etc/aliases
As we know /etc/logcheck/logcheck.logfiles are used to configure, read and monitor the files. This behavior can also be changed and reading files stored in any different location other than the default location. To do so execute the following command,
$ logcheck -c /etc/logcheck/logcheck.conf
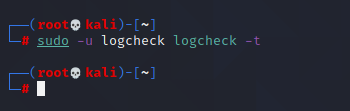
$ logcheck -L /etc/logcheck/logcheck.conf
$ logcheck -t
In the above command, Logtail is a utility command which has a record of positions the tool read from log files. in order to run the tool in testing mode, it can be done by using -t command and offsets will not be updated.
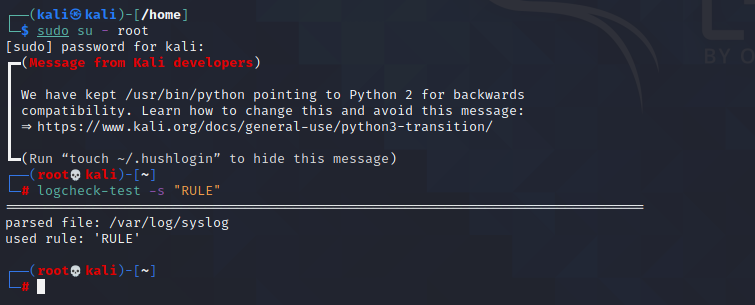
logcheck-test will test logcheck rules quickly and easily. It will parse logfiles to match the logs by single rule or rule file. The testing single rule against /var/log/syslog
$ logcheck-test -s "RULE"
Share your thoughts in the comments
Please Login to comment...