Interim Standard (IS) 95
Last Updated :
08 Aug, 2019
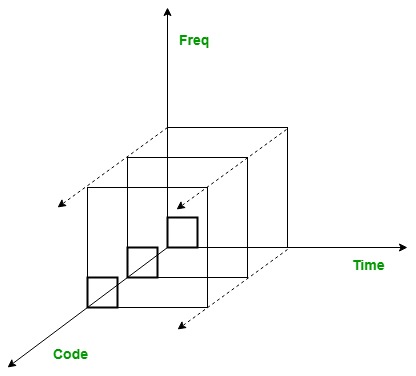
IS-95 stands for Interim Standard 95 and is also known as CDMAOne. It was the first ever CDMA-based digital cellular technology and was developed by Qualcomm. It is an 2G cellular system based on DS-CDMA. To understand IS-95 we need to understand DS and CDMA separately.
DSSS is Direct Sequence Spread Spectrum Technique which is a spread spectrum technique in which the data to be transmitted is encoded using spreading code and received and then decoded using the same code. It is used to avoid interference, spying and jamming. The spreading code used is known to transmitter and receiver only.
CDMA stands for Code Division Multiple Access. It uses the same bandwidth for all the users. However, each user is assigned a separate code which differentiates the from each other.
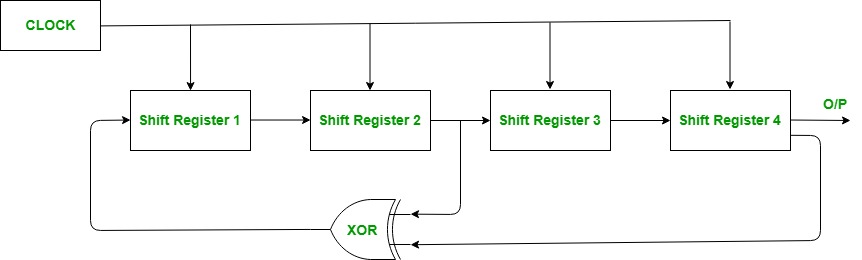
Narrow bandwidth signals are multiplied with a very large bandwidth signals called Pseudo Noise Code Sequence (PN code). Each user has its own PN code which is orthogonal to each other. Auto-correlation is maximum and cross-correlation is zero of these PN codes. They repeats itself after a very large time period and hence, appears to be random. PN Sequence is generated by Linear Feedback Shift Register.
Power Control in IS-95:
It solves the Near-far problem in which transmitters at different distances transmits signal of same power then the power of the signal of Transmitter (nearer to the base station) will be greater than that of Transmitter (farther to the base station). So in power control technique transmitter nearer to the base station transmits less power signal that of the transmitter farther.
It is of two types:
- Open loop power control:
Transmitter senses the power of the received signal at the base station and then adjusts its transmitting power accordingly in subsequent transmissions.
- Closed loop power control:
Base station sends the received signal power information to the transmitter and tells to increment or decrement the transmission power accordingly in subsequent transmissions.
Share your thoughts in the comments
Please Login to comment...