The Importance of Security Testing in Today’s Digital Age
Last Updated :
04 Dec, 2023
Security testing intends to detect flaws in the security mechanisms of information systems. This article focuses on discussing safety testing, its essential steps, and why it is so vital in the digital age.
What is Security Testing?
Security testing is an essential thing of the software development method. It specializes in figuring out and addressing capability vulnerabilities in packages or structures, ensuring they remain resilient to unauthorized rights of entry, information breaches, and cyber-assaults.

Steps Involved in Security Testing
Step 1: Defining Objectives
Before starting up safety testing, it’s crucial to outline clear goals. You want to specify what elements of the device you want to evaluate, which areas are most essential, and what types of threats you’re safeguarding against.
Step 2: Threat Modeling
Threat modelling is a systematic method to spotting ability threats and vulnerabilities. It involves reading the machine’s structure, how information flows within it, and in which attackers might discover openings. Creating a hazard version facilitates prioritising protection testing efforts.
Step 3: Vulnerability Scanning
Vulnerability scanning equipment mechanically discovers acknowledged vulnerabilities in the machine. These equipment take a look at the code, network, and configurations to pinpoint weaknesses that might be exploited.
Step 4: Penetration Testing
Penetration checking out, regularly called ethical hacking, entails simulating real-world attacks to become aware of vulnerabilities that automatic tools may leave out. Penetration testers try to exploit those weaknesses to benefit insights into ability dangers.
Step 5: Code Review
A thorough code assessment inspects the software’s source code to discover vulnerabilities that won’t be apparent at some stage in dynamic testing. This step entails manual code reviews and the use of automatic static analysis tools.
Step 6: Remediation
Once vulnerabilities are identified, they need to be addressed right away. The development crew have to repair those problems and cling to first-class practices for secure coding.
Step 7: Re-testing
After remediation, it is vital to re-test the utility to ensure that the identified vulnerabilities have been successfully resolved. This iterative technique may additionally keep till the utility is deemed secure.
Importance of Security Testing
Now that we’ve got explored the vital steps of security checking out, allow’s delve into why it’s so essential in modern day digital age:
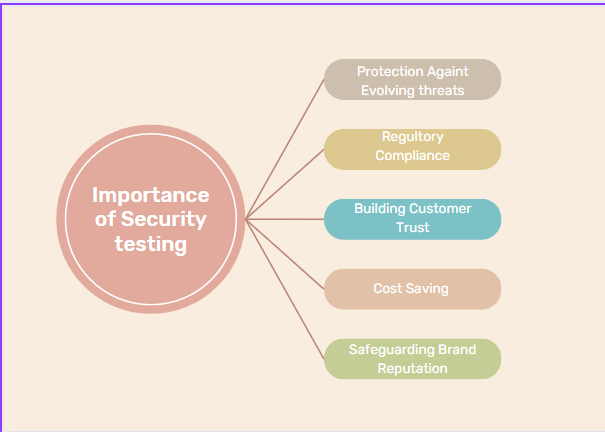
Importance of Security Testing
1. Protection Against Evolving Threats
Cyber threats are always evolving, and new vulnerabilities are observed regularly. Security checking out enables agencies stay in advance via identifying and mitigating these threats earlier than they may be exploited.
2. Regulatory Compliance
Many industries have strict regulatory necessities regarding data protection. Failure to comply can cause extensive fines and damage to a business enterprise’s popularity. Security trying out is essential for assembling these compliance requirements.
3. Building Customer Trust
In an generation wherein statistics breaches frequently make headlines, clients are getting an increasingly number of involved approximately the safety in their statistics. A stable utility no longer most effectively protects touchy information however also fosters belief and self assurance amongst users.
4. Cost Savings
Addressing safety problems early in the improvement manner is greater cost-powerful than managing a breach after it happens. Security checking out helps save you steeply-priced statistics breaches and their associated fees.
5. Safeguarding Brand Reputation
A security breach can critically damage a employer’s recognition and erode client trust. The effect may be lengthy-lasting, making safety trying out a essential thing of shielding a brand’s recognition.
Different Applications of Security Testing
In addition to the steps mentioned above, security testing covers various subtopics and techniques, including:
1. Web Application Security Testing
Web programs are a commonplace goal for cyberattacks because of their occurrence and the valuable statistics they handle. Web utility safety testing includes various techniques and tactics, along with:
- Cross-Site Scripting (XSS) Testing: This focuses on figuring out and addressing vulnerabilities that might allow attackers to inject malicious scripts into net pages, probably compromising personal information and classes.
- SQL Injection Testing: This is set to detect and stopping SQL injection attacks, in which attackers inject malicious SQL queries into input fields, probably gaining unauthorized get entry to to databases.
- Security Headers Analysis: This evaluates the effectiveness of HTTP safety headers (like Content Security Policy and X-Content-Type-Options) in lowering safety risks.
- Web Application Firewall (WAF) Testing: This includes assessing the performance of a Web Application Firewall in blocking and mitigating numerous styles of attacks, consisting of SQL injection and XSS.
2. Mobile Application Security Testing
With cellular apps being an necessary a part of our every day lives, making sure their security is important. Key aspects of cellular utility security trying out consist of:
- Data Storage Encryption: This assesses how nicely sensitive facts is protected within the cell app, making sure that information at rest is securely encrypted.
- Network Communication Security: It examines how the app handles information transmission to and from servers, including using secure conversation protocols like HTTPS.
- Authentication Testing: This verifies the effectiveness of consumer authentication mechanisms to save you unauthorized get admission to.
- Root and Jailbreak Detection: It tests for vulnerabilities related to rooted (Android) or jailbroken (iOS) gadgets, which can expose apps to higher security risks.
3. Network Security Testing
Network protection checking out focuses on evaluating the security of an enterprise’s community infrastructure. Techniques consist of:
- Vulnerability Scanning: This includes the usage of tools to scan community devices and systems for recognized vulnerabilities and misconfigurations.
- Penetration Testing: It simulates actual global attacks to become aware of weaknesses in community configurations, firewalls, and intrusion detection systems.
- Traffic Analysis: This is about tracking and analyzing community visitors to locate suspicious patterns and ability protection breaches.
4. Cloud Security Testing
As corporations migrate to the cloud, making sure cloud safety becomes crucial. Key areas of awareness encompass:
- Identity and Access Management (IAM) Testing: This guarantees that only legal users have get admission to to cloud sources and data.
- Data Encryption: It verifies that information saved in the cloud is nicely encrypted to shield it from unauthorized access.
- Configuration and Security Group Assessment: This evaluates the configurations and protection group settings of cloud times to save you the exposure of sensitive facts.
5. IoT Security Testing
The Internet of Things (IoT) poses unique security challenges because of the extensive form of IoT gadgets. When it comes to IoT protection testing, numerous key aspects are considered:
- Firmware Analysis: This includes a radical exam of the tool’s firmware to discover vulnerabilities and weaknesses that would be exploited by means of capacity attackers.
- Device Authentication Testing: This assessment focuses on how IoT devices confirm their identity in the network, ensuring that simplest legal devices can establish connections.
- Data Encryption for IoT Communication: Here, the emphasis is on securing the transmission of statistics among IoT devices and the community. Data encryption is critical to prevent unauthorized get entry to and eavesdropping.
- Vulnerability Scanning for IoT Devices: This step revolves around figuring out known vulnerabilities in IoT devices and applying essential patches or updates to mitigate ability dangers.
Conclusion
Software development in the digital age requires security testing as an essential part of the process, to protect against the ever-changing cyber threats, comply with the relevant regulations, and maintain the trust and reputation of the customers and the brand. Security testing covers a broad range of applications, such as web and mobile application security testing, network security testing, cloud security testing, and IoT security testing, to secure sensitive data and prevent potential vulnerabilities. Security testing is not only a requirement but a proactive approach to ensure the safety of the digital environment.
Share your thoughts in the comments
Please Login to comment...