Protection Ring
Last Updated :
24 Feb, 2023
In Computer Science, the ordered protection domains are referred to as Protection Rings. These mechanisms help in improving fault tolerance and provide Computer Security. Operating Systems provide different levels to access resources. Rings are hierarchically arranged from most privileged to least privileged. Use of Protection Ring : Use of Protection Rings provides logical space for the levels of permissions and execution. Two important uses of Protection Rings are :
- Improving Fault Tolerance
- Provide Computer Security
Levels of Protection Ring : There are basically 4 levels ranging from 0 which is the most privileged to 3 which is least privileged. Most Operating Systems use level 0 as the kernel or executive and use level 3 for application programs. A resource that is accessible to level n is also accessible to levels 0 to n and the privilege levels are rings.
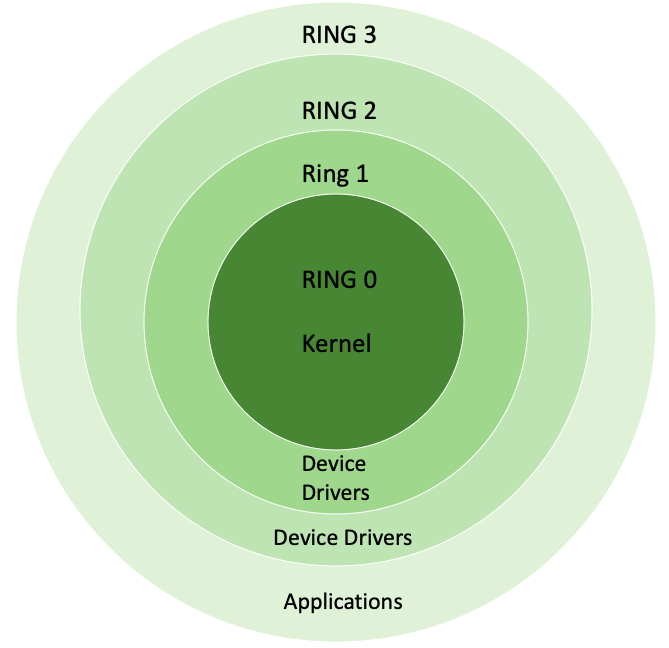
Protection Rings
Modes of Protection Ring : There are basically two modes : Supervisor Mode, and Hypervisor Mode. These are explained as following below in brief.
- Supervisor Mode : Supervisor Mode is an execution mode in some of processors which allows execution of all instructions including privileged instructions. It also gives access to different address space, to memory management hardware, and to other peripherals. Usually, Operating System runs in this mode.
- Hypervisor Mode : Modern CPUs offer x86 virtualization instructions for hypervisor to control “Ring 0” hardware access. In order to help virtualization, VT and Pacifica insert new privilege level below “Ring 0” and Both these add nine new “machine code” instructions that only work on Ring −1 and intended to be used by hypervisor.
Implementation : Protection Rings are combined with processor modes against rule of slave in some systems. Operating system running on hardware that supports such rules can use both methods of protecting or only one of them. Efficient use of architecture of Protection Rings requires close interaction between hardware and operating system. The operating system is designed such that they have worked on a lot of platforms and may have different implementation mechanism rings on each platform. The security model is generally simplified to two levels of access – first is level of “core” and second is level of “user”, even if hardware providing greater granularity of performance levels. Features of Protection Ring :
- Protection Ring follows hierarchy.
- Protection Ring provides layered architecture.
- Protection Ring provides Computer Security.
- Protection Ring provides good Fault Tolerance.
Advantages of Protection Rings:
One of the biggest advantages of using Protection Rings is that it provides better control over the access of system resources. It ensures that the users only have access to the resources they are authorized to access, thus improving computer security. Additionally, the hierarchical arrangement of rings helps in reducing the risk of faults, making the system more fault-tolerant.
Drawbacks of Protection Rings:
One of the major drawbacks of Protection Rings is that it can make the system more complex, making it harder to manage and maintain. Additionally, it can also lead to decreased performance due to the additional layers of security and processing involved.
Conclusion:
Protection Rings provide a highly effective way of ensuring the security and reliability of computer systems. Although it has its limitations, it remains a widely used and popular mechanism for improving fault tolerance and computer security. With continued advancements in technology, it is likely that the implementation of Protection Rings will only become more effective and widespread in the future.
Share your thoughts in the comments
Please Login to comment...