The Network Information Service, or NIS (initially called YP or yellow pages), is a mainframe-client index service convention for circulating server configuration information, for example, client and host names between PCs on a PC network. Sun Microsystems built up the NIS; the innovation is authorized to essentially all other Unix merchants. Since British Telecom PLC claimed the name “Yellow Pages” as an enlisted brand name in the United Kingdom for its paper-based, business phone catalog, Sun changed the name of its framework to NIS, however, all the orders capacities actually start with “yp”. A NIS/YP framework keeps up and disseminates a focal index of the client and gathering information, hostnames, email pseudonyms, and other content-based tables of information in a PC network. For instance, in a typical UNIX climate, the rundown of clients for ID is put in/and so forth/password and mystery verification hashes in/and so on/shadow. NIS includes another “worldwide” client list which is utilized for recognizing clients on any customer of the NIS area. Administrators can arrange NIS to serve secret key information to outside cycles to verify clients utilizing different variants of the Unix crypt(3) hash calculations. In any case, in such cases, any NIS(0307) customer can recover the whole secret phrase information base for disconnected investigation. Kerberos was intended to deal with confirmation in a safer way.
We utilize the Linux NIS mainframe (Network Information Service) for sharing basic information put away in level documents between frameworks on a network. It is frequently ideal to have a mutual archive, (for example, NIS) for putting away clients and gatherings information as opposed to putting away them in level documents like/and so forth/password. So what is the advantage of that? By making such documents accessible through the NIS worker, that would permit any distant NIS customer machine to access or question the information in these mutual records and use them as expansions to the nearby forms.
NIS isn’t for sharing records. We can share any even document which in any event has one section with an extraordinary worth by means of NIS like/and so on/services record. The primary advantage of utilizing the NIS worker is that you keep your information and records, and spread any updates to all clients. A few clients, particularly Windows clients, may think this is a kind of Active Directory like service. The Linux NIS worker is more established than Active Directory and not a reproduce for it.
NIS Introduction:
By running NIS, the framework administrator can disperse administrative information bases, called maps, among an assortment of mainframes (ace and slaves). The administrator can refresh those information bases from a brought together area in a programmed and solid design to guarantee that all customers share a similar naming service information predictably all through the network. NIS was grown freely of DNS and has a marginally extraordinary core interest. While DNS centers around making correspondence less difficult by utilizing machine names rather than mathematical IP addresses, NIS centers around making network administration more sensible by giving unified command over an assortment of network information. NIS stores information about machine names and addresses, yet additionally about clients, the network itself, and network services. This assortment of network information is alluded to as the NIS namespace.
Note — In certain settings machine names are alluded to have had names or machine names. This conversation utilizes a machine, yet some screen messages or NIS map names may utilize host or machine.
NIS Architecture:
NIS utilizes a customer worker plan. NIS mainframes offer types of assistance to NIS customers. The primary workers are called ace workers, and for unwavering quality, they have reinforcement or slave workers. Both ace and slave workers utilize the NIS information recovery programming and both store NIS maps. NIS utilizes domains to mastermind the machines, clients, and networks in its namespace. Nonetheless, it doesn’t utilize an area chain of command; a NIS namespace is level.
A NIS domain can’t be associated straightforwardly to the Internet utilizing just NIS. Notwithstanding, associations that need to utilize NIS and furthermore be associated with the Internet can consolidate NIS with DNS. You can utilize NIS to deal with all neighborhood information and use DNS for the Internet to have queries. NIS gives a sending service that advances have queries to DNS if the information can’t be found in a NIS map. The Solaris working climate additionally permits you to set up the nsswitch.conf record with the goal that has query demands go just to DNS, or to DNS and afterward NIS on the off chance that not found by DNS, or to NIS and afterward DNS if not found by NIS.
NIS Machine Types: There are three kinds of NIS machines:
- Ace mainframe
- Slave mainframe
- Customers of NIS mainframes
Any machine can be a NIS customer, however, just machines with plates ought to be NIS workers, either ace or slave. Workers are likewise customers, ordinarily of themselves.
NIS Servers:
The NIS mainframe doesn’t need to be a similar machine as the NFS record worker. NIS mainframes come in two assortments, ace, and slave. The machine assigned as ace worker contains the arrangement of guides that the framework administrator makes and updates as important. Every NIS space must have one, and just one, ace worker, which can engender NIS refreshes with the least presentation debasement. We can assign extra NIS workers in the domain as slave workers. A slave worker has a total duplicate of the ace arrangement of NIS maps. At whatever point the ace worker maps are refreshed, the updates are proliferated among the slave workers. Slave workers can deal with any flood of solicitations from the ace worker, limiting “worker inaccessible” mistakes.
Ordinarily, the framework administrator assigns one ace worker for all NIS maps. Be that as it may, on the grounds that every individual NIS map has the machine name of the ace worker encoded inside it, you could assign various workers to go about as ace and slave workers for various guides. To limit disarray, assign a solitary worker as the ace for all the guides you make inside a solitary area. The models in this part expect that one worker is the ace for all guides in the space.
NIS Clients:
NIS customers run measures that demand information from maps on the workers. Customers don’t make a differentiation among ace and slave workers, since all NIS workers ought to have a piece of similar information.
NIS Elements:
The NIS naming service is made out of the accompanying components:
- Domains
- Guides
- Daemons
- Utilities
- NIS Command Set
The NIS is an information base that contains a progression of tables. It makes tables from text records like/and so on/password,/and so forth/services, and some other plain documents. Each table may contain one section or more with a novel key on each line. You can consider it like any typical information base. You can question these tables in two different ways:
- Posting the whole table
- Pulling a particular passage via looking
At the point when a program solicitations to look for a client secret phrase subtleties, the customer checks the/and so on/password record to check on the off chance that the client doesn’t exist there; the customer at that point approaches the NIS worker to look for it in the/and so on/password table from the NIS worker. You can utilize any of the services and applications that accompany the NIS mainframe:
- ypserv: This service sits tight for inquiries and offers responses to NIS customers.
- ypbind: This is the customer side of NIS.
- ypxfrd: You can utilize this service for sending the NIS information bases from ace MIS workers to slave workers.
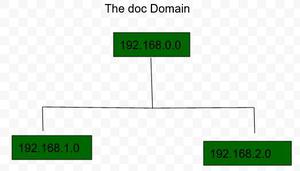
The NIS Domain: A NIS domain is an assortment of machines that share a typical arrangement of NIS maps. Every space has an area name and each machine sharing the basic arrangement of guides has a place with that area. Any machine can have a place with a given area, as long as there is a mainframe for that space’s guides in a similar network. A NIS customer machine acquires its area name and ties to a NIS worker as a component of its boot cycle.
Five daemons are utilized in order to provide the NIS service:
| Daemon |
Function |
| ypserv |
Server process |
| ypbind |
Binding process |
| ypxfrd |
High-speed map transfer |
| rpc.yppasswdd |
NIS password update daemon |
| rpc.ypupdated |
Modifies other maps such as publickey |
A total of 9 utilities support the NIS service:
| Utility |
Function |
| makedbm |
Makes dbm record for a NIS map |
| ypcat |
Records information in a guide |
| ypinit |
Fabricates and introduces a NIS information base and instates NIS customer’s ypservers list |
| ypmatch |
Finds a particular passage in a guide |
| yppoll |
Gets a guide request number from a worker |
| yppush |
Proliferates information from NIS ace to NIS slave worker |
| ypset |
Sets binding to a specific mainframe |
| ypwhich |
Records name of the NIS mainframe and alias interpretation table |
| ypxfr |
Moves information from ace to slave NIS mainframe |
Applications of NIS:
There are some valuable apparatuses that can assist you with dealing with the information in the information base.
- ypcat: You can utilize this to get information from the NIS worker by separating it from the NIS map.
- ypwhich: gets the name of the Linux NIS worker that is reacting to your solicitations.
- ypmatch: instead of snatching the whole guide, or you can look by key to get a particular section.
Share your thoughts in the comments
Please Login to comment...