How to Install Chkrootkit Tool in Kali Linux ?
Last Updated :
06 Oct, 2021
The chkrootkit security scanner is a popular security tool that allows administrators to check the local system for evidence of a rootkit infection. A rootkit is a malicious application that may get access to a computer system without the user’s knowledge. This implies that the rootkit may execute files and change system configurations on the target machine, among other things, which can only be done as the Linux computer’s superuser.
The Chkrootkit utility, as you may have guessed, is used to check for the presence of rootkits. Rootkits are a sort of malicious software that allows an unauthorized person to get access to a server. Rootkits can be a concern if you operate a Linux-based server.
Chkrootkit is one of the most widely used Unix-based rootkit detection applications. It detects problems using the Linux tool commands ‘strings‘ and ‘grep‘.
Please bear in mind that while chkrootkit can detect the files and processes connected with a rootkit, you can’t be certain that all of the rootkit’s components have been located and destroyed. You can protect your computer from rootkits by keeping all of your apps and software up to date, as well as keeping the system patched against all known vulnerabilities.
Installation
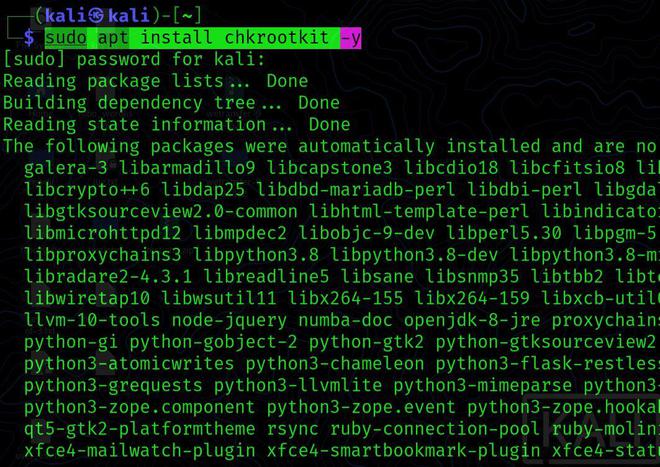
Step 1: Install chkrootkit on Debian and Linux-based distributions to get started.
sudo apt install chkrootkit -y
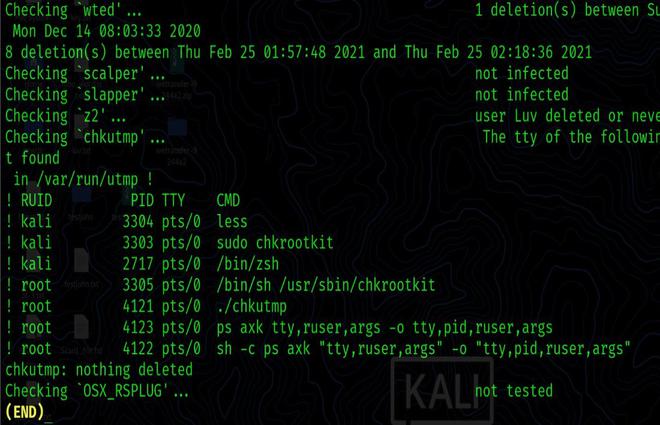
Step 2:
sudo chkrootkit

Throughout the process, you can see that all of the scripts that integrate chkrootkit are running and doing their respective tasks.
Step 3: By scrolling and adding pipes and less, you may achieve a more pleasant view:
sudo chkrootkit | less
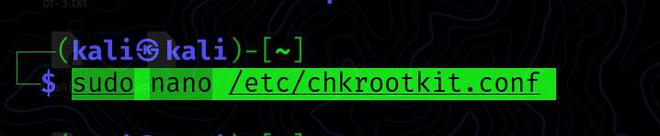
Step 4: By default, you must run chkrootkit manually as described above; however, you may configure daily automated scans by modifying the chkrootkit configuration file found at /etc/chkrootkit.conf, which you may attempt using nano or any other text editor:
sudo nano /etc/chkrootkit.conf
The first line having RUN DAILY=” false” should be updated to RUN DAILY=” true” to ensure daily automated scanning.
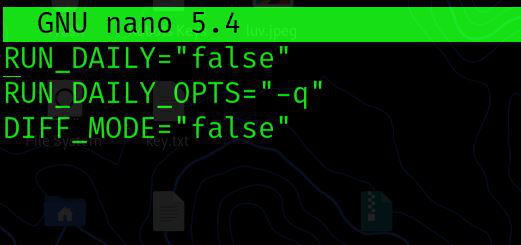
Here’s how it should appear:
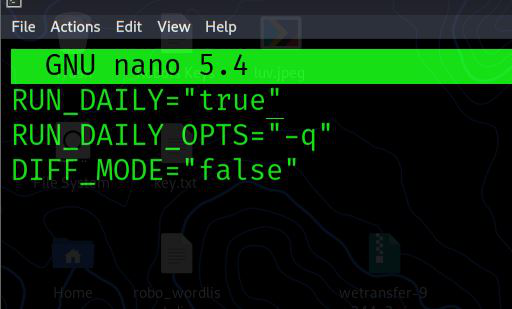
Then, press ctrl+o,Enter, then press ctrl+x.
Usage
The command “chkrootkit -h” as root is the simplest way to launch this tool. All tasks will be completed as a result of this. However, if you wish to select certain settings while running this command, you have the following possibilities:
sudo chkrootkit -h
Outputs
Usage: /usr/sbin/chkrootkit [options] [test …]
Options:
- -h – show this help and exit
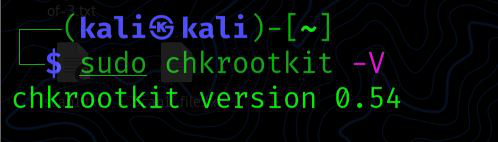
- -V – show version information and exit
- -l – show available tests and exit
- -d – debug
- -q – quiet mode
- -x – expert mode
- -e – exclude known positives. Quoted white space separated list of files/dirs. Please, read /usr/share/doc/chkrootkit/README.FALSE-POSITIVES previously.
- -s – exclude known false positive sniffer (dhcpd, ntop etc) quoted, space separated. Please, read /usr/share/doc/chkrootkit/README.FALSE-POSITIVES previously.
- -r dir – use dir as the root directory
- -p dir1:dir2:dirN path for the external commands used by chkrootkit
- -n – skip NFS mounted dirs
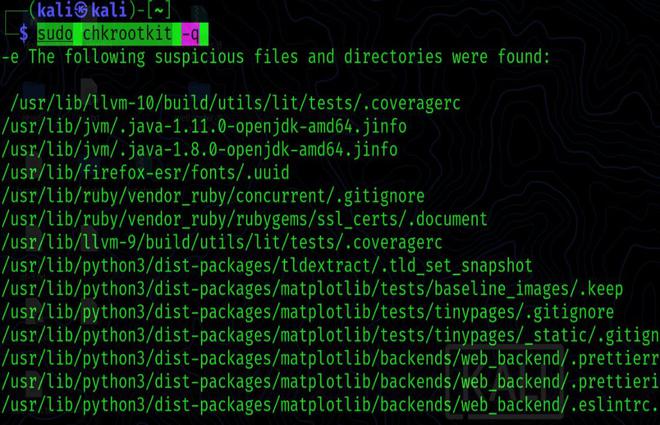
-q: Quiet mode is enabled. Only output messages marked as “infected” are shown in this mode.
sudo chkrootkit -q
sudo chkrootkit -V
Conclusion
Because our systems are now connected across several networks through the internet, it is critical to keep an eye on them for any suspicious attacks or intrusions. Chkrootkit is a simple tool that runs a security check on our servers on a regular basis and protects them from unauthorized access.
Share your thoughts in the comments
Please Login to comment...