Difference between Spoofing and Phishing
Last Updated :
16 May, 2023
Spoofing: Spoofing is a type of attack on a computer device in which the attacker tries to steal the identity of the legitimate user and act as another person. This kind of attack is done to breach the security of the system or to steal the information of the users.
Example: Hackers normally change their IP addresses to hack a website so that the hacker can’t be traced.
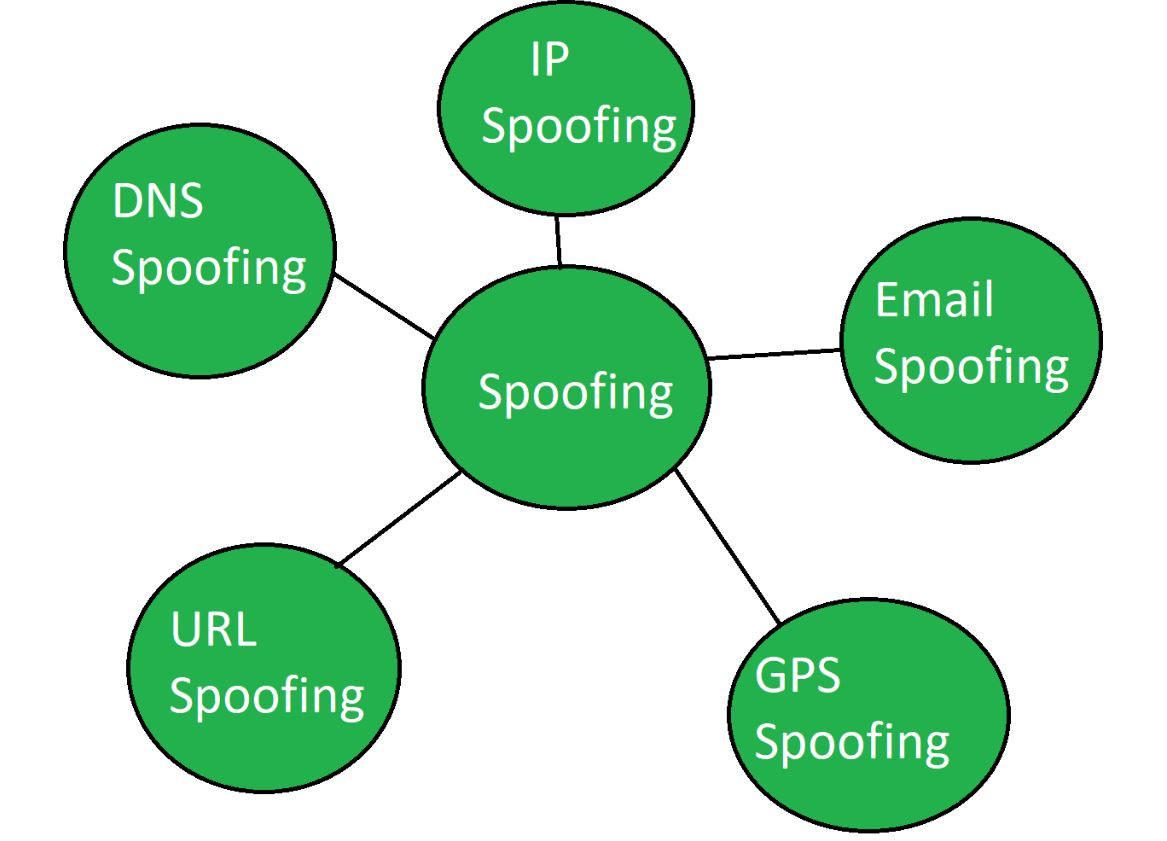
Types of Spoofing attacks:
- Email Spoofing: An attacker sends an email that appears to be from a trusted source, such as a bank or a government agency, to trick the recipient into providing sensitive information.
- DNS Spoofing: An attacker redirects traffic from a legitimate website to a fake website, which is controlled by the attacker, in order to steal sensitive information.
- IP Spoofing: An attacker disguises their IP address with a fake one to bypass security measures and gain unauthorized access to a system.
- Caller ID Spoofing: An attacker manipulates their caller ID to appear as a trusted source, such as a bank, in order to trick the recipient into providing sensitive information.
Phishing: Phishing is a type of attack on a computer device where the attacker tries to find the sensitive information of users in a fraud manner through electronic communication by intending to be from a related trusted organization in an automated manner.
Example: Sometimes hackers through communication ask for OTP or secret PIN of bank transactions by acting as an employee of the bank which is a fraud manner.
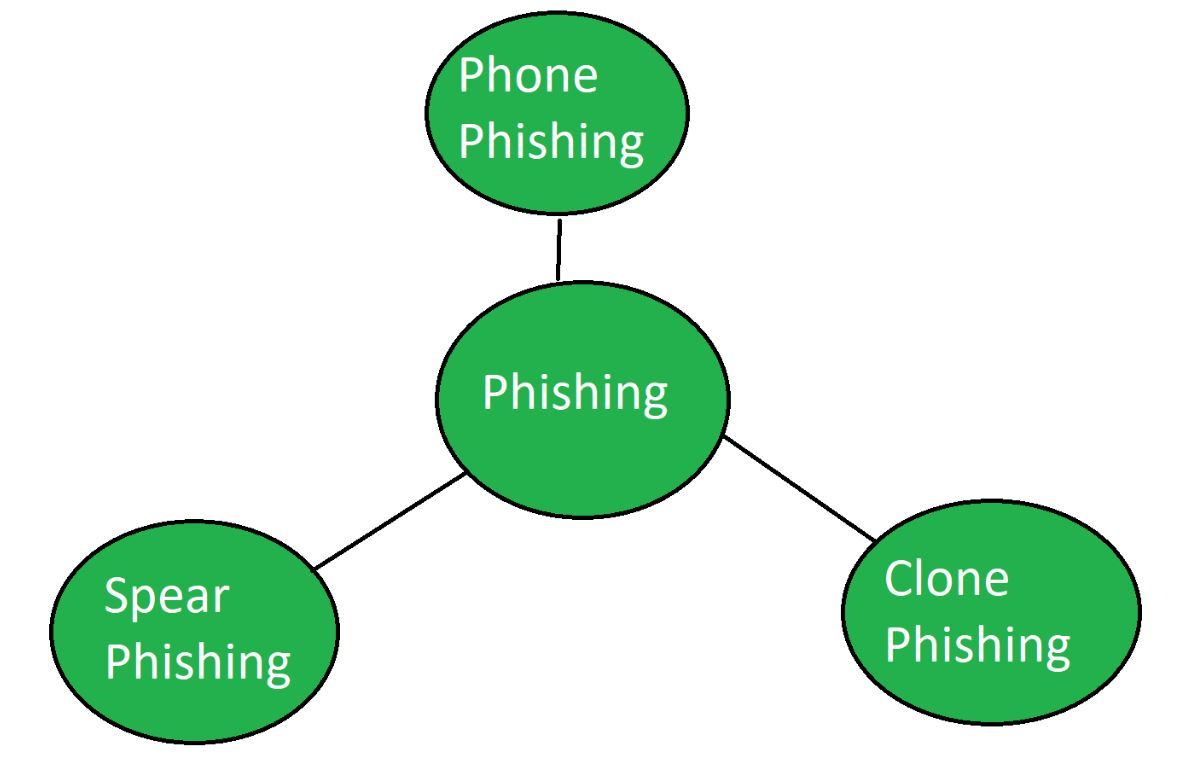
Types of Phishing attacks:
- Spear Phishing: An attacker sends targeted and personalized emails to individuals, such as executives or employees, in order to obtain sensitive information.
- Whaling: Similar to spear phishing, but specifically targets high-level executives or individuals with access to sensitive information.
- Vishing: An attacker uses voice over IP (VoIP) technology to make phone calls and impersonates a trusted source, such as a bank, to trick the recipient into providing sensitive information.
Smishing: An attacker sends text messages that appear to be from a trusted source, such as a bank or a government agency, to trick the recipient into providing sensitive information.
 Similarities between Spoofing and Phishing are:
Similarities between Spoofing and Phishing are:
- Social Engineering: Both Spoofing and Phishing attacks rely on social engineering tactics to deceive the victim into taking an action that could be harmful. They both take advantage of the victim’s trust in the sender of the message to achieve their goals.
- Use of Fake Identity: Both Spoofing and Phishing attacks involve the use of a fake identity to deceive the victim. Spoofing involves using a fake email address or phone number to make it appear as if the message is coming from a trusted source. Phishing involves creating fake websites or using a fake email address that appears to be from a trusted source.
- Theft of Personal Information: Both Spoofing and Phishing attacks aim to steal personal information from the victim. Spoofing can be used to gain access to the victim’s login credentials, while Phishing can be used to steal credit card details, passwords, and other sensitive information.
- Technically Simple: Both Spoofing and Phishing attacks can be executed with basic technical skills. Spoofing involves changing the sender’s email address or phone number, while Phishing can be done by creating a fake website or using a pre-made template.
- Malicious Intent: Both Spoofing and Phishing attacks have malicious intent. The attackers aim to deceive the victim and use their personal information or access to their accounts for financial gain or to cause harm to the victim or their organization.
Difference between Spoofing and Phishing:
| S. No. |
Spoofing |
Phishing |
| 1. |
Hacker tries to steal the identity to act as another individual. |
Hacker tries to steal the sensitive information of the user. |
| 2. |
It doesn’t require fraud. |
It is operated in a fraudulent manner. |
| 3. |
Information is not theft. |
Information is theft. |
| 4. |
Spoofing can be part of the phishing. |
Phishing can’t be the part of the spoofing. |
| 5. |
Needs to download some malicious software on the victim’s computer. |
No such malicious software is needed. |
| 6. |
Spoofing is done to get a new identity. |
Phishing is done to get secret information. |
| 7. |
Types: IP Spoofing, Email Spoofing, URL Spoofing etc. |
Types: Phone Phishing, Clone Phishing etc. |
| 8. |
Examples-
- Hacking of a complete website by modifying its IP Address.
- A banking website appears to be legitimate but it is used to gather sensitive information from user and many more.
|
Examples-
Emails containing these type of terms:
- Click Here
- Verify your personal information
- Payment Failed
- Tax Refunds
|
| 9. |
The best and common way to stop a spoofing attack-
- Ensure the destination of the link received via emails by hovering over the link before clicking on it.
- Delete strange emails like unprofessional emails, alarming messages, misspellings in the message body, etc.
- Open the attached documents or any other type of attachment from reliable source only.
|
The best and common way to stop a phishing attack-
- Be wary of grammatical flaws in the communication’s content.
- Keep a check on spelling mistakes in an email.
- Check for the phrase structure and unusual sentence phrasing.
|
Conclusion :
while both spoofing and phishing are forms of social engineering attacks that use deception to exploit the victim’s trust, they differ in their goals and methods. Spoofing is a technique used to disguise the sender’s identity, while phishing is a method used to trick the recipient into divulging personal information or performing an action. To protect oneself from these attacks, it’s essential to stay vigilant, be cautious of any unsolicited emails or messages, and verify the sender’s identity before providing any sensitive information.
Share your thoughts in the comments
Please Login to comment...