Difference between site to site VPN and remote access VPN
Last Updated :
18 Mar, 2023
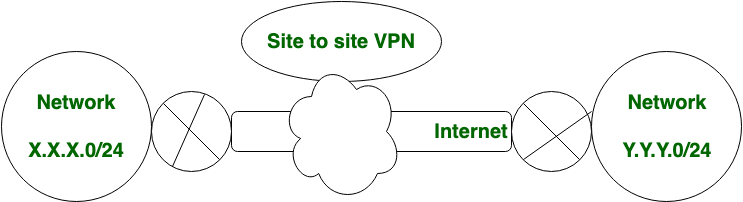
Both Site to site VPN and Remote access VPN are the types of VPN which stands for Virtual Private Network. Site-to-Site VPN is also known as Router-to-Router VPN. In site to site VPN, IPsec security method is used to create an encrypted tunnel from one customer network to remote site of the customer. Multiple users are not allowed in Site-to-Site VPN.
Advantages:
- Provides a secure connection between two or more networks.
- Enables users to access resources located in another location or office.
- Encrypts traffic between networks to enhance security.
- Offers a cost-effective solution for interconnecting networks.
- Provides a high level of network performance and reliability.
Disadvantages:
- Requires more complex configuration and management than remote access VPNs.
- May require additional hardware and software components to implement.
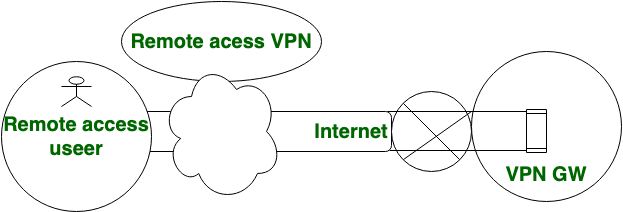
In Remote Access VPN, Individual users are connected to the private network and It allows the technique to access the services and resources of that private network remotely. It is most suitable for the business and home users. In remote access VPN, multiple users are allowed.
Remote Access VPN:
Advantages:
- Enables secure access to a private network from a remote location or device.
- Allows remote workers to access company resources securely.
- Provides a flexible solution that can be accessed from anywhere with an internet connection.
- Requires less complex configuration and management than site-to-site VPNs.
- Provides a high level of user privacy and data protection.
Disadvantages:
- May be slower than site-to-site VPN due to the use of encryption and additional network traffic.
- May require additional software components to be installed on the user’s device.
- May require additional user training and support to ensure proper use.
Similarities between site-to-site VPN and remote access VPN:
- Both site-to-site VPN and remote access VPN use encryption protocols to secure data transmissions over the internet.
- Both site-to-site VPN and remote access VPN can be used to access internal network resources from outside the organization’s network.
- Both site-to-site VPN and remote access VPN provide a secure connection between the user and the organization’s network, protecting against unauthorized access and cyber attacks.
- Both site-to-site VPN and remote access VPN require a form of user authentication to access the network, ensuring that only authorized users are granted access.
- Both site-to-site VPN and remote access VPN require additional hardware or software to be installed to establish the VPN connection.
Let’s see the difference between Site to site VPN and Remote access VPN, which are given below:
| S.NO |
Site to site VPN |
Remote access VPN |
| 1. |
In site to site VPN, IPsec security method is used to create an encrypted tunnel from one customer network to remote site of the customer. |
In remote access VPN, Individual users are connected to the private network. |
| 2. |
Site to site VPN does not need setup on each client. |
Remote access VPN may or may not needed setup on each client. |
| 3. |
Site to site VPN does not require every user to initiate the VPN tunnel setup. |
Remote access VPN require every remote access user to initiate the VPN tunnel setup. |
| 4. |
Site to site VPN supports IPsec technology. |
While Remote access VPN supports SSL and IPsec technology. |
| 5. |
In site to site VPN, multiple users are not allowed. |
In remote access VPN, multiple users are allowed. |
| 6. |
A site-to-site VPN, meanwhile, connects individual networks to each other. |
A remote access VPN connects remote users from any location to a corporate network |
| 7. |
Site-to-Site VPN is widely used in Office LAN users of branch offices that need to connect to servers located at the headquarters. |
Remote Access VPN is used for Roaming users who want to access resources/servers securely. |
Conclusion:
Site-to-site VPN and remote access VPN serve different purposes and have different requirements. Site-to-site VPNs are used to connect multiple networks together, while remote access VPNs are used to provide individual users with secure access to a private network. The choice between these two types of VPNs depends on the specific needs of the organization and its users.
Share your thoughts in the comments
Please Login to comment...