Essential Activities of Risk Management
Last Updated :
24 Mar, 2022
Risk management is the area which tries to ensure that the impact of risks on cost, quality and schedule is minimized. The main purpose of risk management is to identify and manage the risks associated with a software project and solve the problem. Estimating the risks that can affect the project schedule or the quality of the software being developed and taking action to avoid the risk is the important task of a project manager. Identifying and preparing plans to reduce their impact on the project is called risk management. The basic motivation of risk management is to avoid disaster or heavy losses. The risk can be categorised as follows.
- Project Risks : These are the risks which affect the project schedule or resources.
- Product Risks : These are the risks which affect the quality or performance of the being developed.
- Business Risks : These are the risks which affect the organization developing or procuring the software.
This classification is not a special classification. If an experienced programmer leaves a project then it is a project risk because the delivery of the system may be delayed, the product may be a risk because the replacement may not be a seasoned one and therefore may be mistakes and business. Risk management is very important for software projects due to the inherent uncertainties that most projects face. The process of risk management is shown in fig. 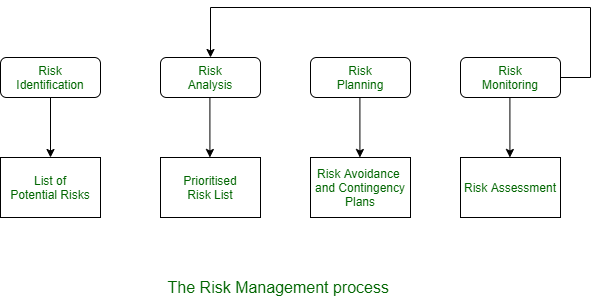 The process of risk management involves several stages are as follows-
The process of risk management involves several stages are as follows-
- Risk Identification : In this stage, the possible project, product and business risks are identified.
- Risk Analysis : In this stage or process, the likelihood and consequences of these risks assessed.
- Risk Planning : In this stage, risk avoidance in either planned to affect the plan or mitigate its effects on the project.
- Risk Monitoring : In this stage, risk assessment is done continuously and the risk reduction plan is revised as more information about risk is available.
Like all other project planning, the risk management process is an iterative process that continues throughout the project. Risk management process results should be documented in a risk management plan. This should include a discussion of the risks that the project faces, analyzing these risks and requiring plans to manage these risks.It may also include some results of the risk management. The risk management has to deal with identifying the undesirable events that may occur, the likelihood of them occurring and the losses that occur when undesirable events occur. knowing this, strategies can be devised to reduce the possibility of reducing the risk or impact of the content. Therefore, risk management revolves around risk assessment and risk control. These are top 10 item techniques for managing them:
| S.No> |
Risk Item |
Risk Management Techniques |
| (1) |
Personnel shortfalls |
Staffing with top talent; Job matching; Team building; Key-personnel agreement; Training; Prescheduling key people. |
| (2) |
Unrealistic schedules and budgets |
Detailed multisource cost and schedule estimation; Design to cost; Incremental development; Software reuse; Requirements scrubbing. |
| (3) |
Developing the wrong software functions |
Organization analysis; Mission analysis; OPS concept formulation; User surveys; Prototyping; Early users’ manuals. |
| (4) |
Developing the wrong user interface |
Prototyping; Scenarios; Task analysis; User characterization (functionality, style, workload). |
| (5) |
Gold plating |
Requirements scrubbing; Prototyping; Cost benefit analysis; Design to cost. |
| (6) |
Continuing stream of requirements changes |
High change threshold; Information hiding; Incremental development (defer changes to later increments). |
| (7) |
Shortfalls in externally furnished components |
Benchmarking; Inspection; Reference checking; Compatibility analysis. |
| (8) |
Shortfalls in externally performed tasks |
Reference checking; preaward audits; Awardfee contracts; Competitive design or prototyping teambuilding. |
| (9) |
Real time performance shortfalls |
Simulation; Benchmarking; Modeling; Prototyping; Instrumentation; Tuning. |
| (10) |
Straining computer science capabilities |
Technical analysis; Cost-benefit analysis; Prototyping; Reference checking. |
Share your thoughts in the comments
Please Login to comment...