Difference between Hashing and Encryption
Last Updated :
07 May, 2023
Encryption and hashing are the two terms used widely in cryptography. In this article, we will learn what is the difference between encryption and hashing.
1. Encryption :
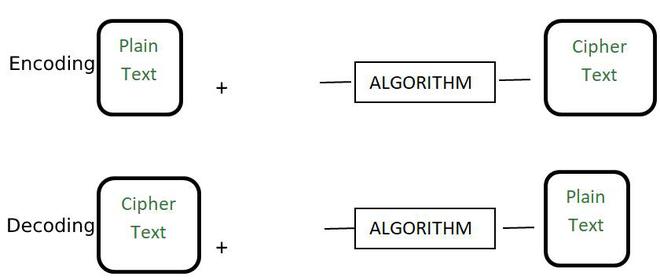
Encryption is the process of converting a normal readable message known as plaintext into a garbage message or not readable message known as Ciphertext. The ciphertext obtained from the encryption can easily be transformed into plaintext using the encryption key. Some of the examples of encryption algorithms are RSA, AES, and Blowfish.
2. Hashing :
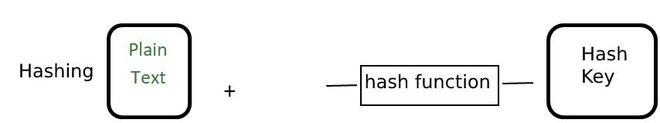
Hashing is the process of converting the information into a key using a hash function. The original information cannot be retrieved from the hash key by any means. Generally, the hash keys are stored in the database and they are compared to check whether the original information matches or not. They are generally used to store the passwords for login. Some of the examples of a hashing algorithm are MD5, SHA256.
Difference between Hashing and Encryption :
| Basis |
Hashing |
Encryption |
| Definition |
It is a process to convert information to a shorter fixed value known as the key that is used to represent the original information. |
It is the process to encode data securely such that only the authorized user who knows the key or password is able to retrieve the original data for everyone else it is just garbage. |
| Purpose |
The purpose of hashing is indexing and retrieving items from the database. The process is very fast. |
The purpose of encryption is to transform data to keep it secret from others. |
| Reverse Process |
The hash code or key can not be reversed to the original information by any means. It can only be mapped and the hash code is checked if the hash code is the same the information is the same otherwise not. The original information can not be retrieved. |
The original information can be easily retrieved if we know the encryption key and algorithm used for encryption. |
| Secure |
It is more secure in comparison to encryption. |
It is less secure in comparison to hashing. |
| Creation of file |
Generally, it tries to generate a new key for each information passed to the hash function but on rare occasions, it might generate the same key popularly known as a collision. |
It will always generate a new key for each information. |
| Example |
MD5, SHA256 |
RSA, AES and Blowfish |
| Output |
The output of a hashing algorithm is a fixed-size hash value |
the output of an encryption algorithm is ciphertext of the same size or larger than the original data |
| Length of information |
The hashed information is generally of small and fixed length. It does not grow with the increase in the information length of information. |
The encrypted information is not of fixed length. It grows with the increase in length of information. |
| key management |
Hashing does not require a secret key or algorithm to produce a hash value |
encryption requires a secret key or algorithm to encrypt and decrypt data. |
Share your thoughts in the comments
Please Login to comment...