Branch Prediction in Pentium
Last Updated :
05 May, 2023
Why do we need branch prediction?
- The gain produced by Pipelining can be reduced by the presence of program transfer instructions eg JMP, CALL, RET etc
- They change the sequence causing all the instructions that entered the pipeline after program transfer instructions invalid
- Thus no work is done as the pipeline stages are reloaded.
Branch prediction logic: To avoid this problem, Pentium uses a scheme called Dynamic Branch Prediction. In this scheme, a prediction is made for the branch instruction currently in the pipeline. The prediction will either be taken or not taken. If the prediction is true then the pipeline will not be flushed and no clock cycles will be lost. If the prediction is false then the pipeline is flushed and starts over with the current instruction. It is implemented using 4 way set associated cache with 256 entries. This is called Branch Target Buffer (BTB). The directory entry for each line consists of:
- Valid bit: Indicates whether the entry is valid or not.
- History bit: Track how often bit has been taken.
Source memory address is from where the branch instruction was fetched. If the directory entry is valid then the target address of the branch is stored in corresponding data entry in BTB. Working of Branch Prediction:
- BTB is a lookaside cache that sits to the side of Decode Instruction(DI) stage of 2 pipelines and monitors for branch instructions.
- The first time that a branch instruction enters the pipeline, the BTB uses its source memory to perform a lookup in the cache.
- Since the instruction was never seen before, it is BTB miss. It predicts that the branch will not be taken even though it is unconditional jump instruction.
- When the instruction reaches the EU(execution unit), the branch will either be taken or not taken. If taken, the next instruction to be executed will be fetched from the branch target address. If not taken, there will be a sequential fetch of instructions.
- When a branch is taken for the first time, the execution unit provides feedback to the branch prediction. The branch target address is sent back which is recorded in BTB.
- A directory entry is made containing the source memory address and history bit is set as strongly taken.
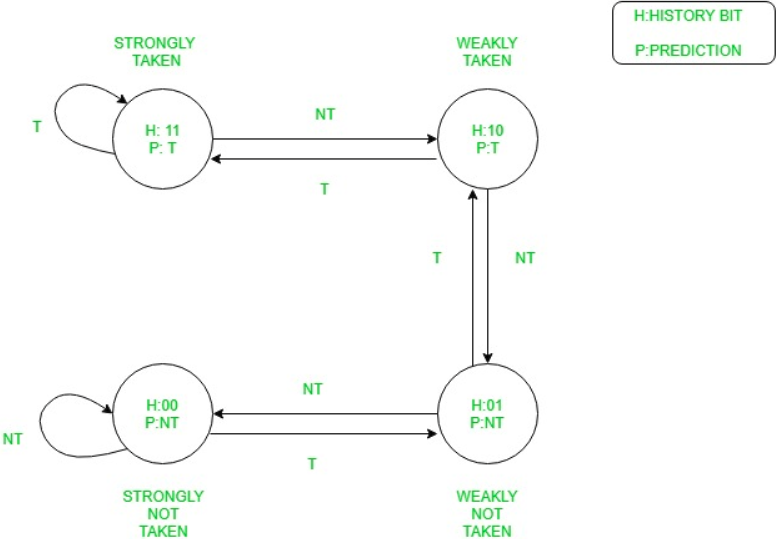 The diagram is explained by the following table:
The diagram is explained by the following table:
| History Bits |
Resulting Description |
Prediction made |
If branch taken |
If branch not taken |
| 11 |
Strongly Taken |
Branch Taken |
Remains in same state |
Downgraded to weakly taken |
| 10 |
Weakly Taken |
Branch Taken |
Upgraded to strongly taken |
Downgraded to weakly not taken |
| 01 |
Weakly Not Taken |
Branch Not Taken |
Upgraded to weakly taken |
Downgraded to strongly not taken |
| 00 |
Strongly Not Taken |
Branch Not Taken |
Upgraded to weakly not taken |
Remains in same state |
Advantages of branch prediction in the Pentium :
Improved performance: By predicting the outcome of conditional branches in advance, the Pentium can fetch and execute the instructions from the predicted path, avoiding the performance penalty associated with mispredicted branches.
Increased instruction throughput: Branch prediction enables the Pentium to maintain a high instruction throughput, by allowing the processor to continue fetching and executing instructions from the predicted path while waiting for the results of earlier instructions.
Reduced branch misprediction penalty: The Pentium’s dynamic branch prediction mechanism can quickly adapt to changes in program behavior, reducing the penalty associated with branch mispredictions.
More efficient use of processor resources: Branch prediction allows the Pentium to utilize processor resources more efficiently by avoiding idle cycles that would otherwise occur due to waiting for branch resolution. This results in better overall system performance.
Better handling of large code bases: The Pentium’s branch prediction mechanism allows it to better handle large code bases with many conditional branches, improving overall system performance and reducing the impact of branch mispredictions.
More accurate predictions over time: The Pentium’s branch prediction mechanism uses historical data to make more accurate predictions over time, which helps to further reduce the penalty associated with branch mispredictions.
Improved pipelining: Branch prediction also enables improved pipelining in the Pentium, as the processor can continue fetching and executing instructions from the predicted path while waiting for the result of the branch instruction. This results in higher instruction throughput and better overall system performance.
Disadvantages of branch prediction in the Pentium :
Increased complexity: Branch prediction adds additional complexity to the Pentium’s design, which can increase the design and manufacturing costs of the processor.
Increased power consumption: Branch prediction can increase the power consumption of the Pentium, as it requires additional hardware and software overhead.
Limited accuracy: Branch prediction is not perfect, and the Pentium’s dynamic branch prediction mechanism can make incorrect predictions, leading to mispredicted branches and reduced performance.
Increased memory usage: Branch prediction requires the Pentium to maintain a history of past branch outcomes, which can result in increased memory usage and cache pollution. This can lead to reduced performance in applications that rely heavily on memory access.
Difficulty predicting indirect branches: Indirect branches, such as those found in switch statements, can be difficult to predict accurately with dynamic branch prediction. This can lead to reduced performance and increased branch misprediction penalties.
Increased vulnerability to side-channel attacks: Branch prediction can make the Pentium more vulnerable to side-channel attacks, where an attacker can use the timing of branch instructions to infer sensitive information about the system. This can be a concern in security-critical applications.
Increased software complexity: The Pentium’s branch prediction mechanism requires additional software overhead to manage and maintain the branch history. This can increase the complexity of software development and maintenance, and may require additional training and expertise for software engineers.
Share your thoughts in the comments
Please Login to comment...