Web Server, Proxies and their role in Designing Systems
Last Updated :
03 May, 2024
In system design, web servers and proxies play crucial roles in ensuring efficient communication and scalability. Web servers, like Apache or Nginx, serve as the backbone of client-server interactions, handling requests and delivering content. Proxies act as intermediaries, managing traffic flow, improving performance, and enhancing security by caching and load balancing. Together, they form the core infrastructure of distributed systems. Understanding their roles and integration is fundamental for designing resilient and high-performing systems.

Important Topics for Web Server, Proxies and their role in Designing Systems
Webservers
Every website sits on a computer that is known as a web server. Web server is a computer system that hosts websites and runs web server software. It is responsible for hosting websites. (Websites in themselves are collections of web pages). Some of the popular web servers these days are Apache HTTP and Microsoft IIS. Also, the machine(normal computer) to act as a web server should possess two traits:
- Machine should be able to run web server software.
- Machine should throughout be connected to the internet so as to serve clients being available all time.
Every web server connected to the internet is given a unique address of 4 digits that are separated by dots as shown below:
68.122.31.125

Types of Webservers
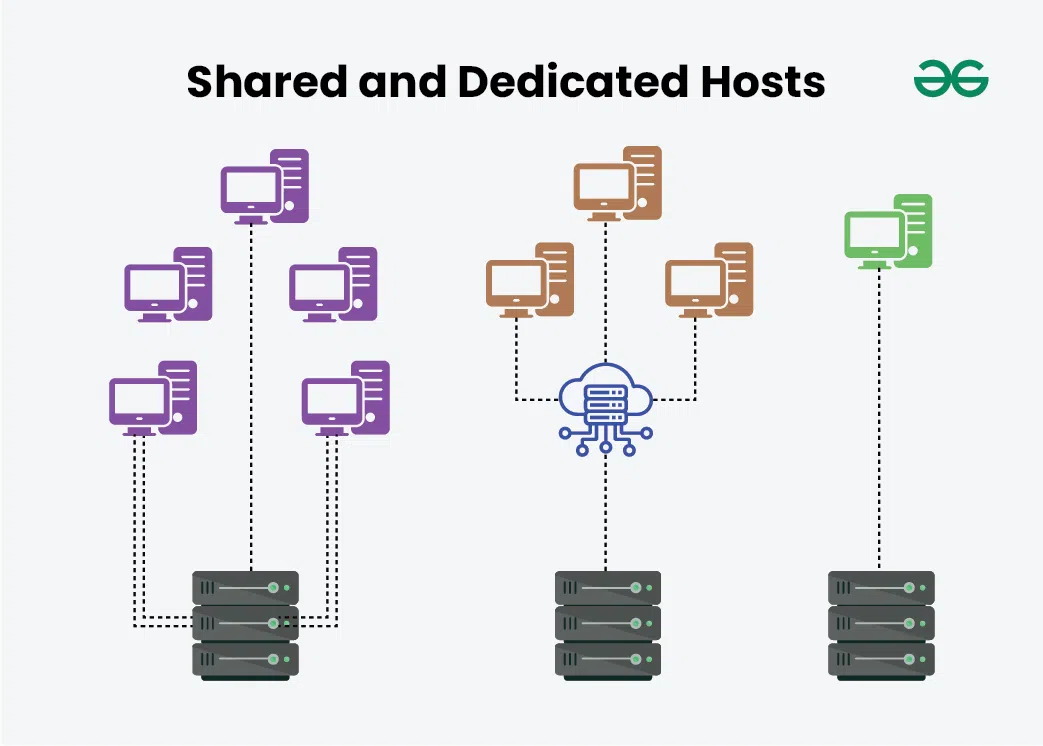
Web servers are categorized as per hosting websites into:
- Shared Hosts: Designed to host over 100+ websites.
- Dedicated Hosts: Designed to host only 1-2 websites
- Custom Hosts: Specifically designed as per internal requirements for any large-scale websites.
That’s why personal websites or indeed generic small websites uses shared hosts while on the other hand large-scale organization that generates tremendous traffic load uses dedicated and even if there is a requirement for custom server modification then we do even use custom hosts.
How web server Work?
- Web client sends a request to the web server via an HTTP request.
- Note here there are two scenarios:
- If the data is present for the HTTP request in the static database within the web server then immediately corresponding HTTP response will be sent.
- If data is not present then the web server will send a servlet request for processing to the application server.
- Now it will not look up into static DB rather a web server will send a servlet request to the application server.
- In processing, the application server will look up the application datastore in order to run the servlet and fetch the required information.
- Now it will send back a servlet response to the web server. Hence this built-in response from the web server will be sent to the web client.
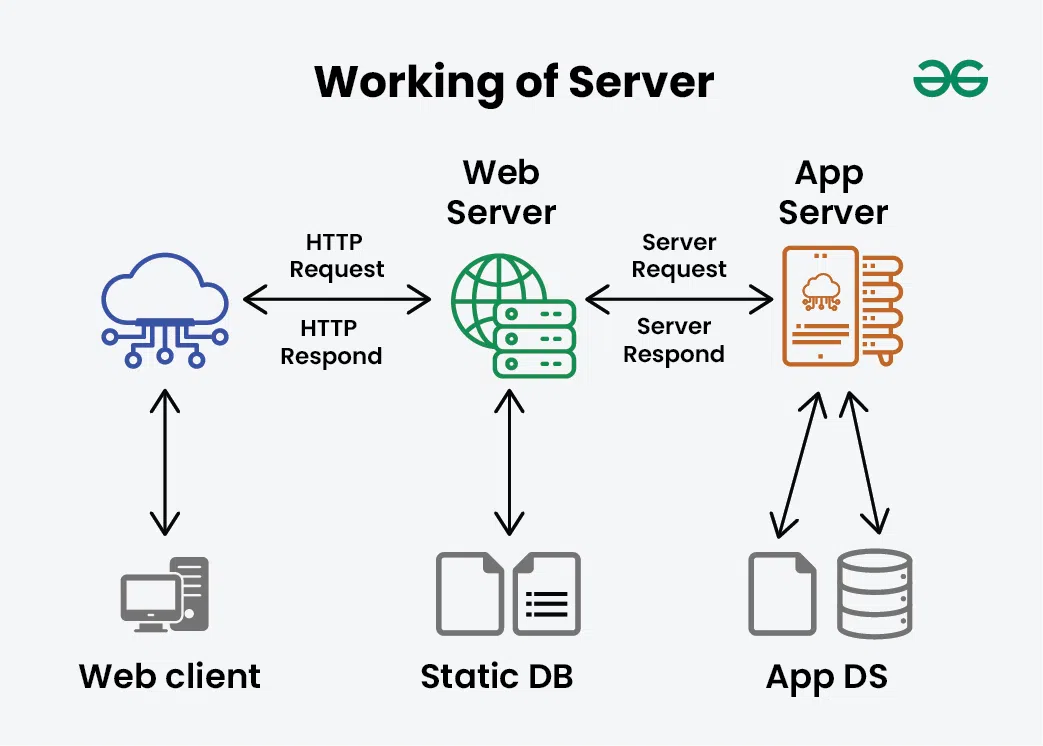
Application Server
Application server is specifically designed to run applications (generally invoking extreme computations) that includes both hardware and software to provide an environment to run the applications.
- Usage: Provides environment to run specific applications such as cloud applications and many more and do provides computational power.
- Note: Application server is only required when there is intense computation required which web server can not handle.
Use Cases of web servers
Below are some of the uses of web servers:
- Hosting websites.
- Processing data sent from another server.
- Hosting hypervisors. (software programs responsible for managing virtual machines)
- Distributing and monitoring software updates.
Examples of Web Servers
Popular Web servers used are as follows:
- Tomcat servers: Tomcat is used for Java web applications that do not need to meet all of the standards of Java EE but still need a dependable solution. Tomcat isn’t regarded as a full application server because it also functions as a Web server and a Servlet container.
- Apache servers, accept directory (HTTP) requests from users of the Internet and deliver the desired data in the form of files and Web pages. The features of Apache are supported by a large portion of the software and code on the Internet. It is developed by Apache Software Foundation.
- Node.js servers: It includes a built-in HTTP module that enables it to transmit data using the HyperText Transfer Protocol (HTTP). An HTTP server can be built using the HTTP module.
Others also include such as Lightpad, Jigsaw Server, Sun Java System Web Server, Internet Information Services(IIS)
Note:
- Apache HTTP is the most popular web server in the world.
- Apache with Tomcat Module is used to have JSP and J2EE support.
Proxies in Distributed Systems
A proxy server is an intermediary piece of hardware/software sitting between the client and the backend server. Prior to discussing types of proxies let us get familiar with a few terminologies to better understand the concept.
- Filter requests: It runs every request through a filter, looking up each address in its database of allowed or disallowed sites, and it allows or blocks each request based on its internal database. A system administrator can configure the proxy server to allow or block certain sites.
- Log requests: Transform requests (encryption, compression, etc)
- Cache: A caching proxy server can also improve web performance by caching frequently used pages so the user request doesn’t have to go all the way out to the Internet at large to get some of the data it needs to display a particular page.
- Batch requests: Collapsed forwarding: enable multiple client requests for the same URI to be processed as one request to the backend server.
Collapse requests for data that is spatially close together in the storage to minimize the reads
- Security: A proxy server can also be used to beef up security for a business. A proxy server can provide network address translation, which makes the individual users and computers on the network anonymous when they are using the Internet. This makes it much harder for hackers to access individual computers on the network.
Types of Proxies
Proxies can sit on the client’s local server side and also somewhere between the client and remote servers which we are going to discuss. Basically, they are of 2 types only because the proxy server can reside on the client’s local server or anywhere between the client and the remote servers.
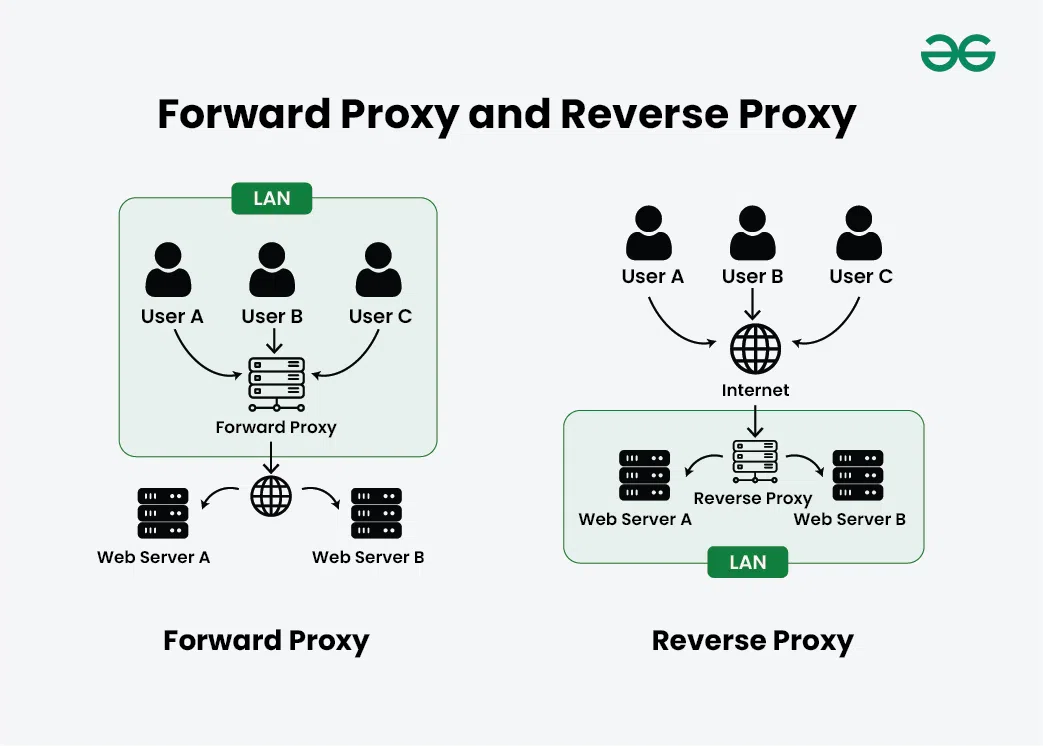
1. Forward Proxy
An open proxy is a proxy server that is accessible by any Internet user. Generally, a proxy server only allows users within a networking group (i.e. a closed proxy) to store and forward Internet services such as DNS or web pages to reduce and control the bandwidth used by the group. With an open proxy, however, any user on the Internet is able to use this forwarding service.
When to use a forward proxy server?
- Forward proxies are in handy when we don’t want the main server to be able to see the client’s IP because it only has the proxy server’s IP.
- Used in scenarios where a large number of clients are present and the proxy server is handling all traffic.
- Used when we block a specific website.
- Putting forward proxy sites in the response’s cache.
Note: Forward proxy is also known as ‘Open Proxy’.
2. Reverse Proxy
A reverse proxy retrieves resources on behalf of a client from one or more servers. These resources are then returned to the client, appearing as if they originated from the proxy server itself. It typically sits behind the firewall in a private network and directs client requests to the appropriate backend server. A reverse proxy provides an additional level of abstraction and control to ensure the smooth flow of network traffic between clients and servers.
When to use a reverse proxy server?
- Management of traffic control.
- Load balancing: Distributes client requests in a certain manner across servers ensuring no server is overloaded leading to higher speed and capacity utilization. If any server goes down the load balancer redirects to other servers available.
- Reducing DDoS attacks. It is because only proxy server is accessible to the outer world where servers are not.
- Caching a server response.
- SSL encryption reduces the strain on the web server and improves client-server architecture performance.
Note: Reverse proxy is also known as ‘Closed Proxy’.
Disadvantages of Proxy Server
Below are the disadvantages of proxy server:
- Proxy Server Risks: Free installation does not invest much in backend hardware or encryption. It will result in performance issues and potential data security issues. If you install a “free” proxy server, treat it very carefully, some of those might steal your credit card numbers.
- Browsing history log: The proxy server stores your original IP address and web request information is possibly unencrypted from and saved locally. Always check if your proxy server logs and saves that data – and what kind of retention or law enforcement cooperation policies they follow while saving data.
- No encryption: No encryption means you are sending your requests as plain text. Anyone will be able to pull usernames and passwords and account information easily. Keep a check that the proxy provides full encryption whenever you use it.
Conclusion
After learning about forward and reverse proxy and the locations of the servers in each case, let us talk about some workrounds:
- In scalable distributed systems, the reverse proxy creates the SPOF scenario since all primary servers are impacted if the reverse proxy server goes down.
- Organizations use forward proxy to set constraints and perform domain operations on the computers assigned to clients (users/employees).
Share your thoughts in the comments
Please Login to comment...