Priority Ceiling Protocol
Last Updated :
02 Jan, 2020
Priority Ceiling Protocol is a job task synchronization protocol in a real-time system that is better than Priority inheritance protocol in many ways. Real-Time Systems are multitasking systems that involve the use of semaphore variables, signals, and events for job synchronization.
In Priority ceiling protocol an assumption is made that all the jobs in the system have a fixed priority. It does not fall into a deadlock state.
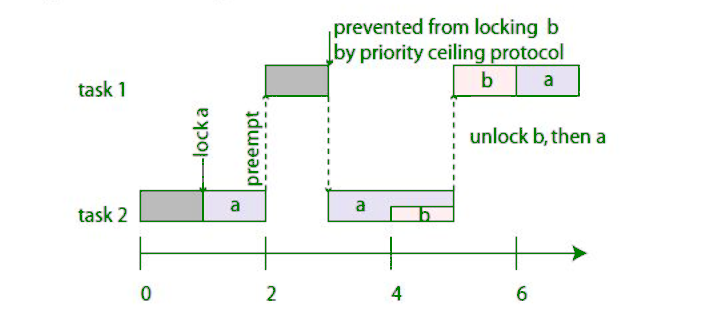
The chained blocking problem of the Priority Inheritance Protocol is resolved in the Priority Ceiling Protocol.
The basic properties of Priority Ceiling Protocols are:
- Each of the resources in the system is assigned a priority ceiling.
- The assigned priority ceiling is determined by the highest priority among all the jobs which may acquire the resource.
- It makes use of more than one resource or semaphore variable, thus eliminating chain blocking.
- A job is assigned a lock on a resource if no other job has acquired lock on that resource.
- A job J, can acquire a lock only if the job’s priority is strictly greater than the priority ceilings of all the locks held by other jobs.
- If a high priority job has been blocked by a resource, then the job holding that resource gets the priority of the high priority task.
- Once the resource is released, the priority is reset back to the original.
- In the worst case, the highest priority job J1 can be blocked by T lower priority tasks in the system when J1 has to access T semaphores to finish its execution.
Priority Scheduling Protocol can be used to tackle the problem of the priority inversion problem unlike that of Priority Inheritance Protocol. It makes use of semaphores to share the resources with the jobs in a real-time system.
Share your thoughts in the comments
Please Login to comment...