Methodology followed by the Hackers
Last Updated :
02 Jul, 2021
Overview :
In popular media, the term “hacker” refers to someone who uses bugs and exploits to get into someone else’s security, or who uses his technical knowledge to behave productively or maliciously. Hackers are computer specialists who are knowledgeable in both hardware and software. A hacker is a computer enthusiast who is proficient in a programming language, as well as security and network administration. He is the type of person who enjoys learning new technologies and computer system intricacies in order to improve his capabilities and talents.
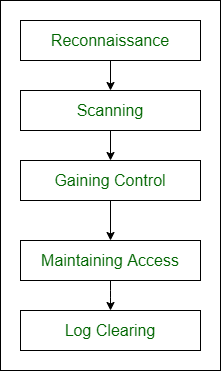
Different types of methodologies :
Here, we will discuss the Different types of methodologies as follows.
- Reconnaissance –
Reconnaissance is the process of gathering information about the target system. Finding vulnerabilities in the computer system, or the methods that are left vulnerable is part of the process. If the hacker is able to get access to the system, he or she will continue the hacking procedure. The hacker has a lot of knowledge at the end of the reconnaissance phase, which he can use to build a promising attack on the target system.
- Scanning –
Before launching an attack, the hacker wants to determine whether the system is operational, which apps are in use, and what versions of those programs are in use. Scanning entails looking for all open and closed ports in order to locate a backdoor into the system. It entails getting the target’s IP address, user accounts, and other information. The information acquired during the reconnaissance phase is utilized to inspect the network using tools such as dialers and port scanners. N-map is a popular, powerful, and freely available scanning tool.
- Gaining Control –
The information obtained in the previous two phases is utilized to enter and take control of the target system over the network or physically in this phase of the hacking method. This stage is often referred to as “Owning the System.”
- Maintaining Access –
After acquiring access to the system in the previous stage, the hacker keeps the access for future attacks and makes changes to the system so that no other security personnel or hacker can acquire access to the compromised system. The attacked system is referred to as the “Zombie System” in this case.
- Log Clearing –
It is the method of erasing any remaining log files or other sorts of evidence on the hacked system that could lead to the hacker’s capture. Penetration testing is one of the instruments in ethical hacking approaches that can be used to catch a hacker.
Share your thoughts in the comments
Please Login to comment...