Lightweight Directory Access Protocol (LDAP)
Last Updated :
21 Jun, 2019
Lightweight Directory Access Protocol (LDAP) is an internet protocol works on TCP/IP, used to access information from directories. LDAP protocol is basically used to access an active directory.
Features of LDAP:
- Functional model of LDAP is simpler due to this it omits duplicate, rarely used and esoteric feature.
- It is easier to understand and implement.
- It uses strings to represent data
Directories:
Directories are set of object with similar attributes, organised in a logical and hierarchical manner. For example, Telephonic Directories. It is a distributed database application used to manage attributes in a directory.
LDAP defines operations for accessing and modifying directory entries such as:
- Searching for user specified criteria
- Adding an entry
- Deleting an entry
- Modifying an entry
- Modifying the distinguished name or relative distinguished name of an entry
- Comparing an entry
LDAP Models:
LDAP can be explained by using four models upon which it based:
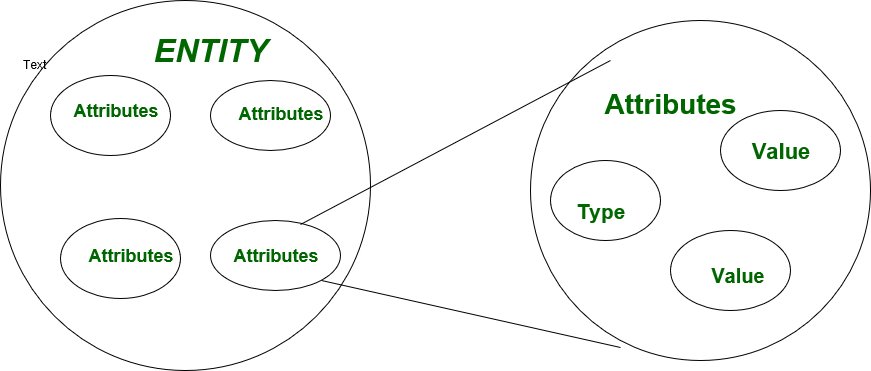
- Information Model:
This model describes structure of information stored in an LDAP Directory.In this basic information is stored in directory is called an entity. Entries here represents object of interest in real world such as people, server, organization, etc. Entries contain collection of attributes that contain information about object.Every attribute has a type and one or more values. Here types of attribute is associated with syntax and syntax specifies what kind of values can be stored
- Naming Model:
This model describes how information in an LDAP Directory is organized and identified. In this entries are organized in a Tree-Like structure called Directory Information Tree (DIT). Entries are arranged within DIT based on their distinguished name DN. DN is a unique name that unambiguously identifies a single entry.
- Functional Model:
LDAP defines operations for accessing and modifying directory entries . In this we discuss about LDAP operations in a programming language independent manner LDAP operations can be divided into following categories:
• Query
• Update
• Authentication
- Security Model:
This model describes how information in LDAP directory can be protected from unauthorized access. It is based on BIND operation. There are several bind operation can be performed.
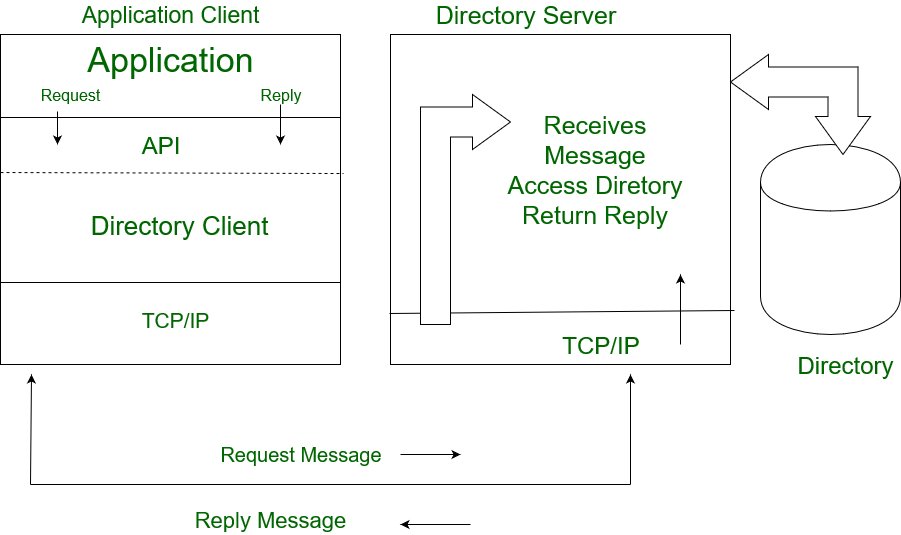
LDAP Client and Server Interaction:
It is quite similar to any other client-server interaction. In this client performs protocol functions against server.The interaction takes place as follows:-
- A protocol request is send to server by client.
- Server perform operations on directory such as search, update, delete, etc.
- The response is sent back to the client.
Microsoft, Open LDAP, Sun, etc can easily be made an LDAP server. if the user don’t want to install directory service but want to use LDAP instruction for available LDAP server then user can use four11, bigfoot etc. Making an LDAP client is quite simple as there are SDK’s in many programming languages such as C, C++, Perl, Java, etc.
User has to perform certain task to be LDAP client:
(i) Go get SDK for your language
(ii) Use function of SDK to connect to LDAP
(iii) Operate on LDAP
LDAP functions / operations:
- (a) For Authentication:
It includes bind, unbind and abandon operations used to connect and disconnect to and from an LDAP server, establish access rights and protect information. In authentication, client session is established and ended using the functions
-> BIND/UNBIND
-> Abandon
- (b) For Query:
It includes search and compare operations used to retrieve information from a directory. In query, server performs action using function
-> Search
-> Compare Entry
- (c) For Update:
It includes add, delete, modify and modify RDN operations used to update stored information in a directory. In update, we can make changes in directories by using function
-> Add an entry
-> Delete an entry
-> Modify an entry
- Client establishes session with server (BIND) using Hostname/IP/and Port Number. For security purposes, user set USER-ID and Password based authentication.
- Server perform operations such as read, update, search, etc.
- Client end session using UNBIND or Abandon function.
Advantages of LDAP:
- Data present in LDAP is available to many clients and libraries.
- LDAP support many types of application.
- LDAP is very general and has basic security.
Disadvantages in LDAP:
It does not handle well relational database.
Share your thoughts in the comments
Please Login to comment...