Goblyn – Enumeration and capture of website files metadata
Last Updated :
22 Nov, 2021
Metadata can consist of some sensitive information. steganography is the technique in which the sensitive data is been hidden into pdf, png, or sometimes video files. So to get this metadata we can use various automated tools. Goblyn tool is a python language-based tool that can extract the various types of files from target domains like .pdf,.xml and also display its information like size, permissions, encoding, MIME type, and many more. Sometimes this information can give sensitive data like usernames and passwords. This tool is also available on the GitHub platform for free.
Note: Make Sure You have Python Installed on your System, as this is a python-based tool. Click to check the Installation process: Python Installation Steps on Linux
Installation of Goblyn Tool on Kali Linux OS
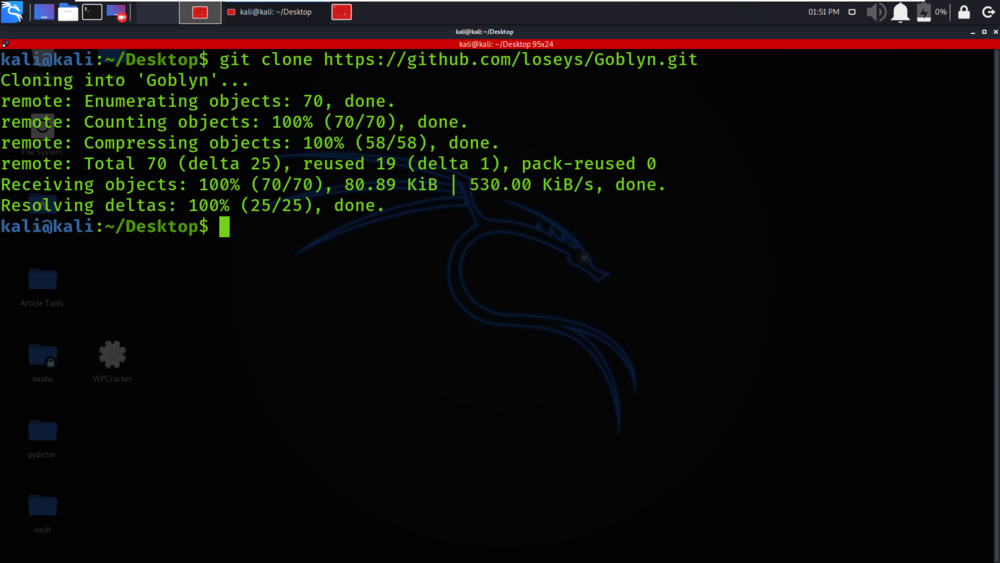
Step 1: Use the following command to install the tool in your Kali Linux operating system.
git clone https://github.com/loseys/Goblyn.git
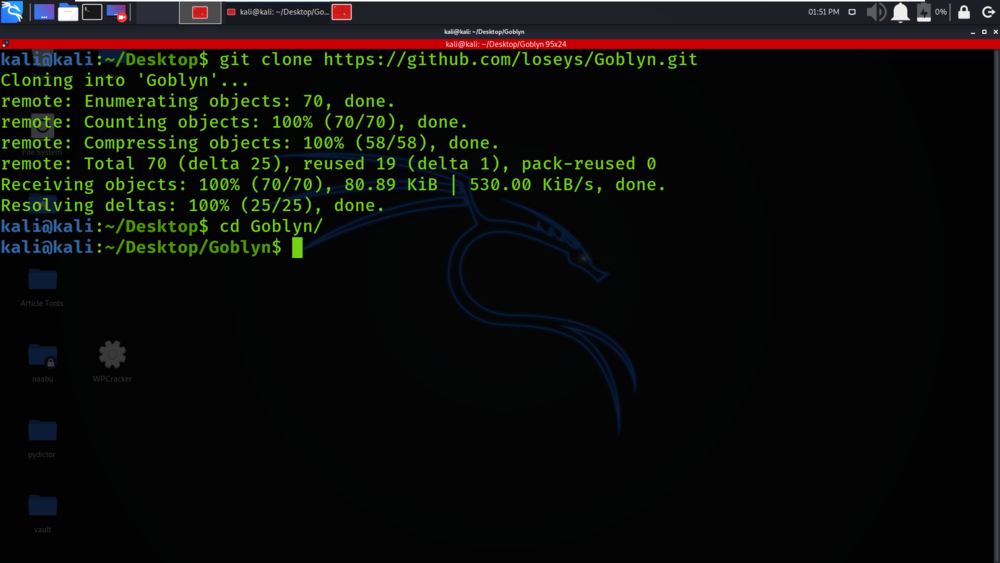
Step 2: Now use the following command to move into the directory of the tool. You have to move in the directory in order to run the tool.
cd Goblyn
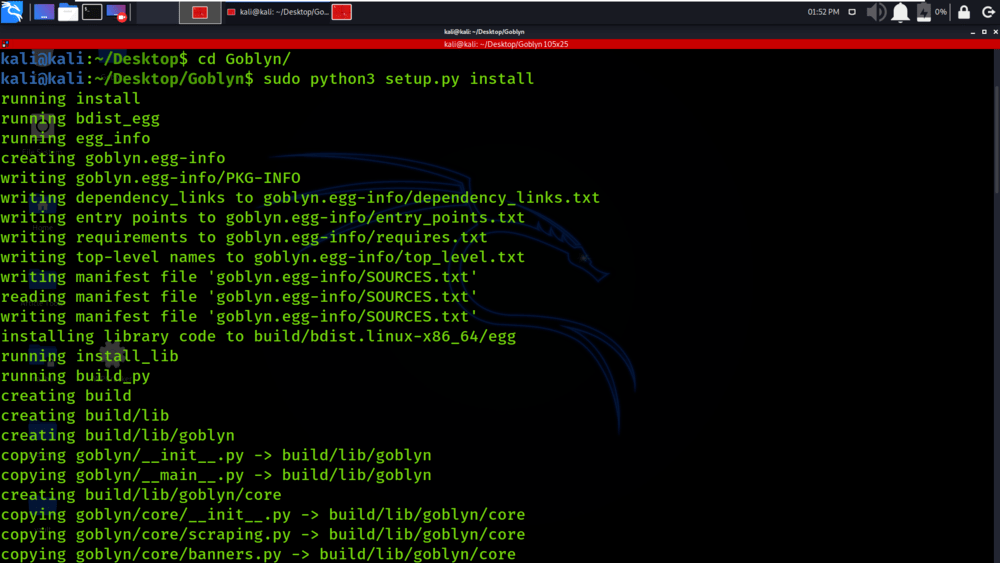
Step 3: You are in the directory of the Goblyn. Now you have to install the Goblyn tool using the following command.
sudo python3 setup.py install
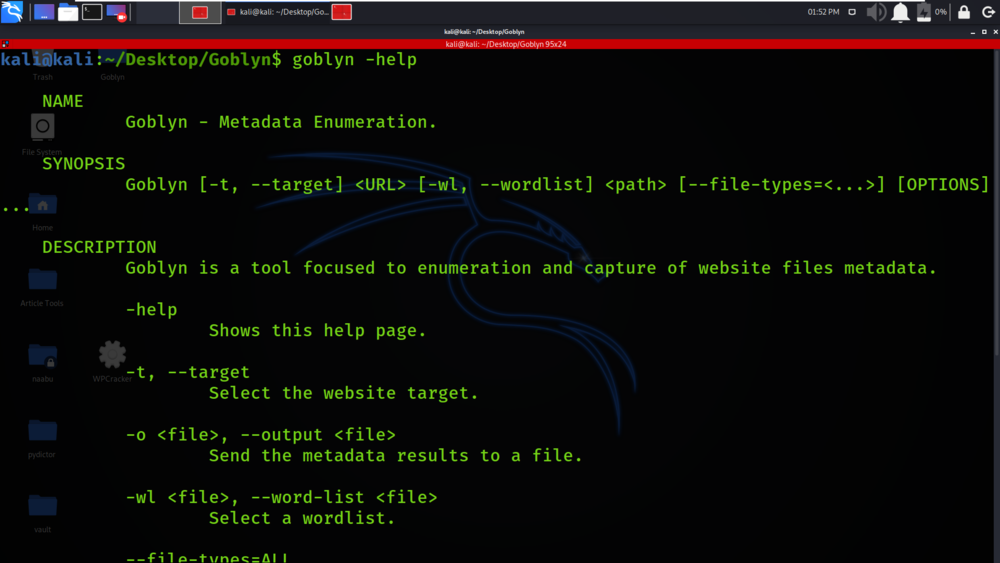
Step 4: All the dependencies have been installed in your Kali Linux operating system. Now use the following command to run the tool and check help section.
goblyn -help
Working with Goblyn Tool on Kali Linux OS
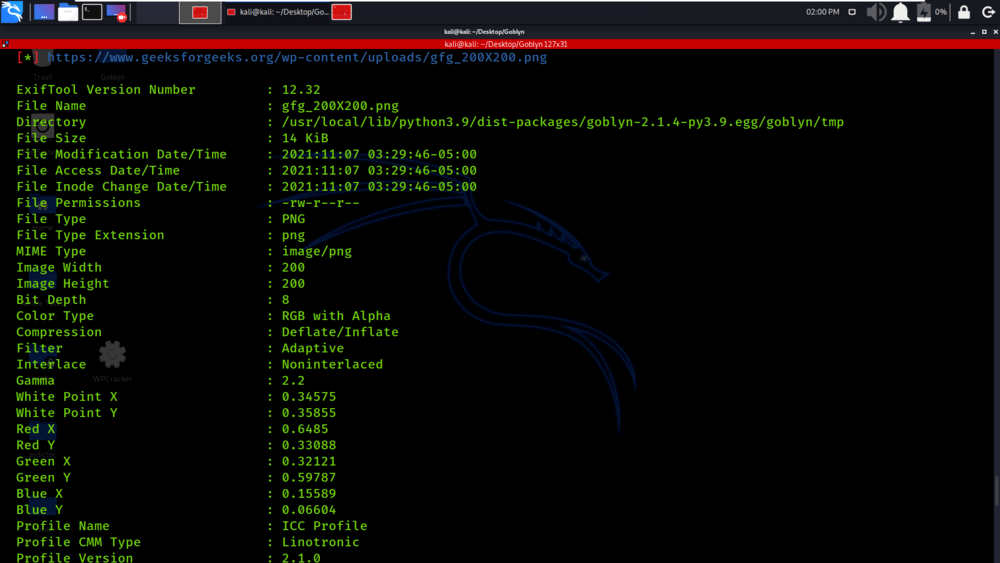
Example: Extracting Metadata from geeksforgeeks.org.
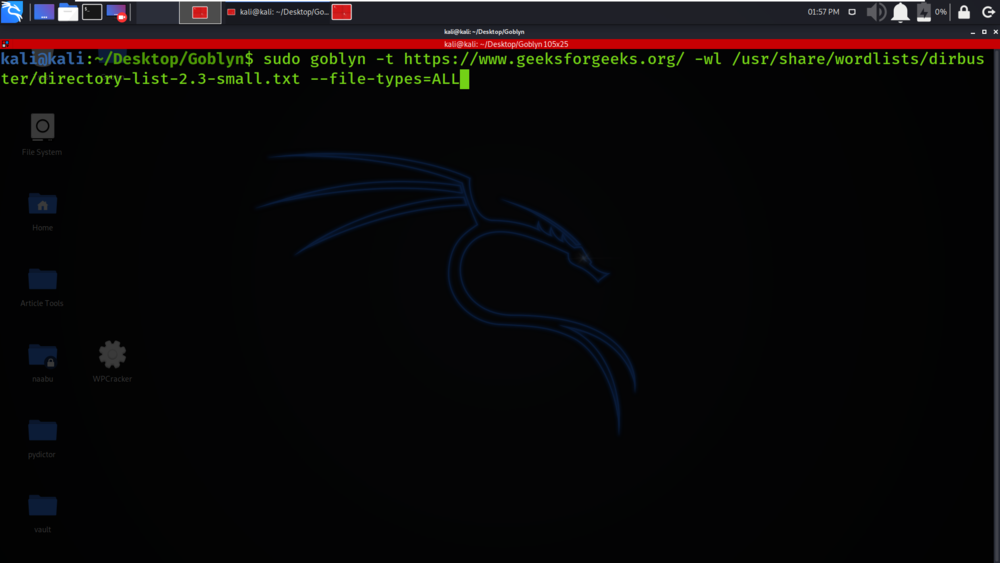
sudo goblyn -t https://www.geeksforgeeks.org/ -wl /usr/share/wordlists/dirbuster/directory-list-2.3-small.txt –file-types=ALL
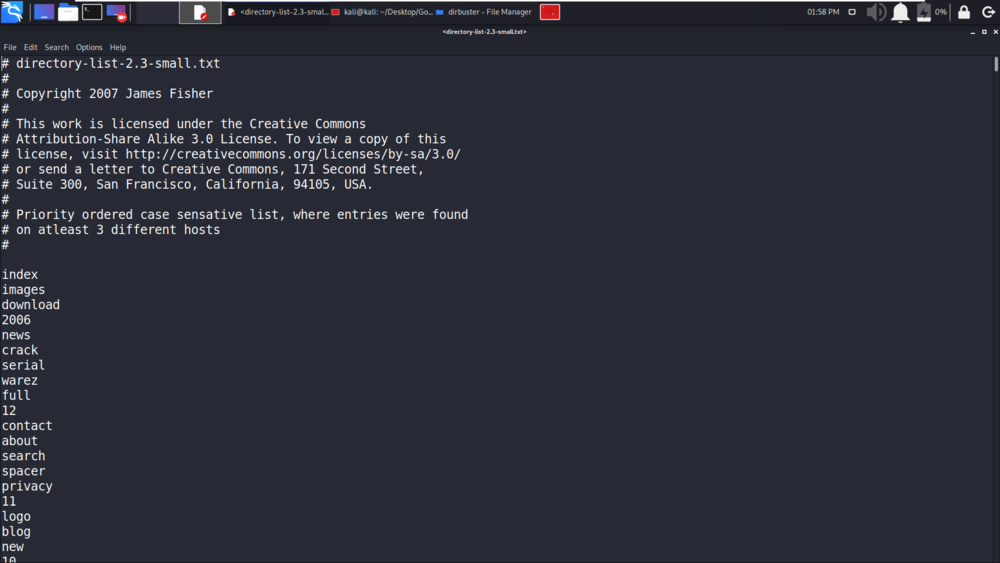
We have displayed the contents of word-lists which will be enumerated to find directories and files.
We have given the command in which we have specified the target as https://www.geeksforgeeks.org/, we have given the absolute path of word-list and we have given the file type as ALL. You can also specify the file type as .pdf, .png, and many more.
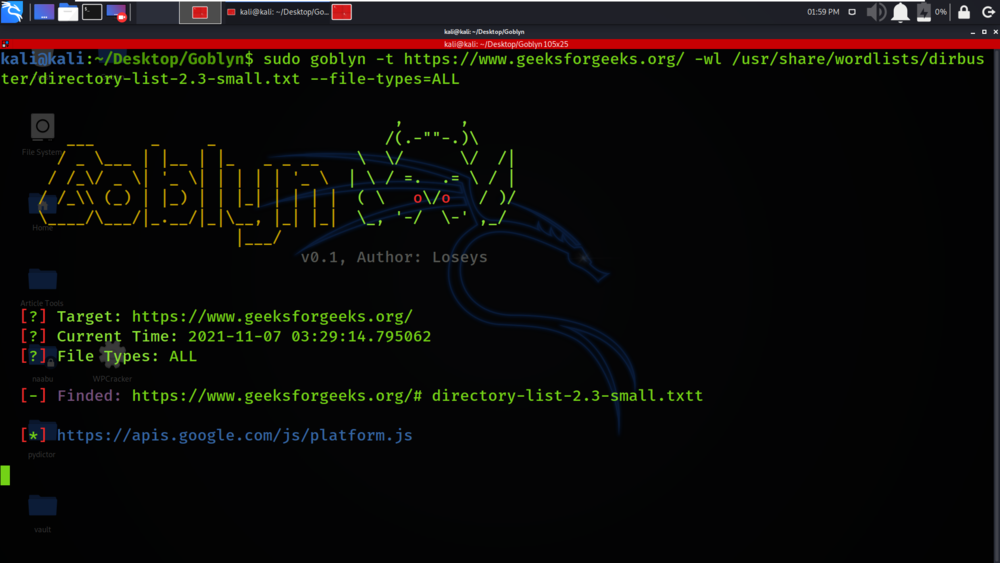
The tool has started the process of extracting metadata.
We have the link of the file and the details of that file.
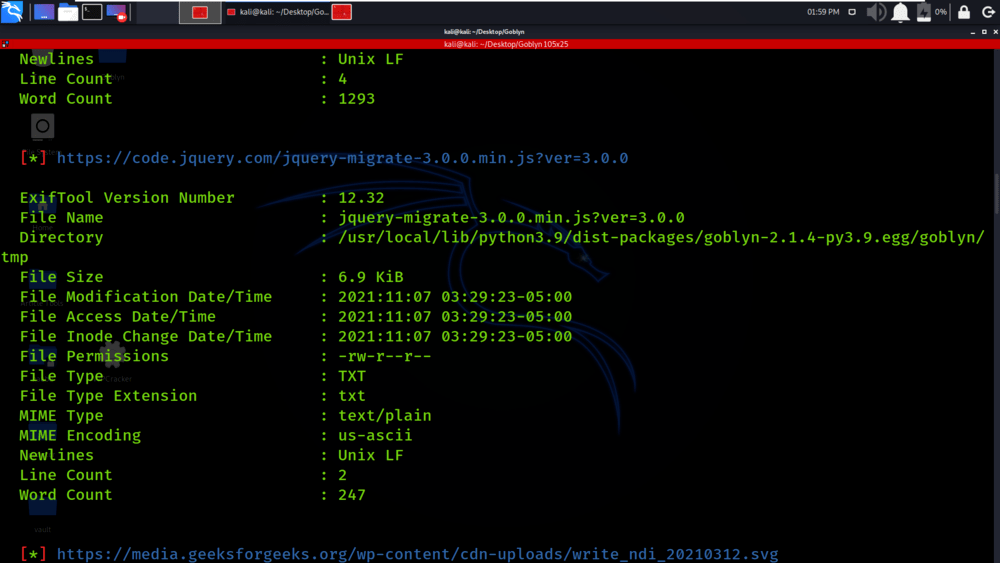
You can see that detailed information about the file is been displayed in the below screenshot.
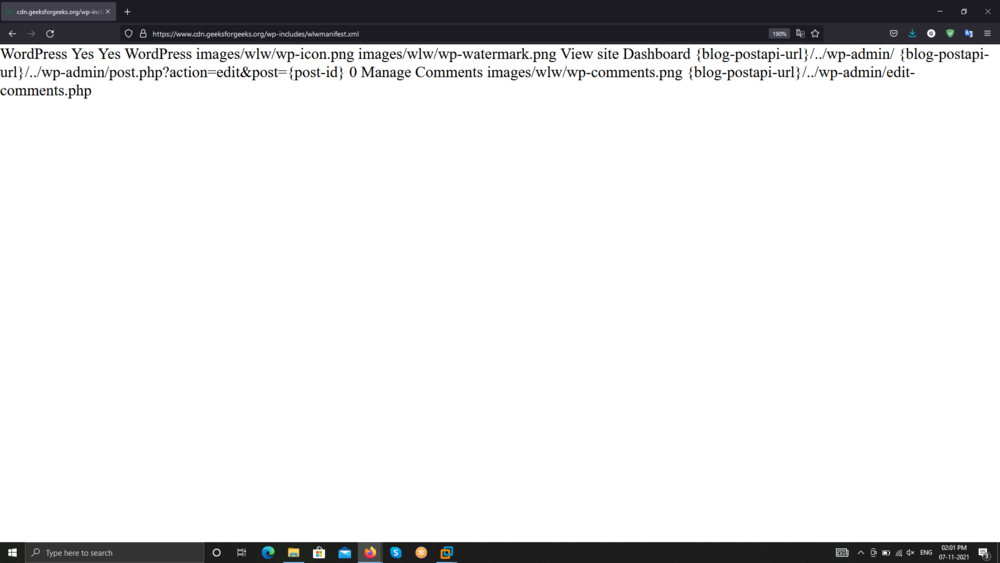
We have opened one of the file on the web browser which is a XML file.
Share your thoughts in the comments
Please Login to comment...