Electronic Data Interchange
Last Updated :
08 Aug, 2019
Electronic Data Interchange is a technique for computer to computer exchange of business documents in a standard electronic format between business partners or companies. Companies use EDI systems for exchanging business information automatically by computer systems as transactions without paper and hence minimizes or completely eliminates the human intervention. Electronic data interchange is generally used for B2B transactions.
Common EDI documents:
- Shipping requests
- Invoice
- Acknowledgement
- Purchase order
EDI system:
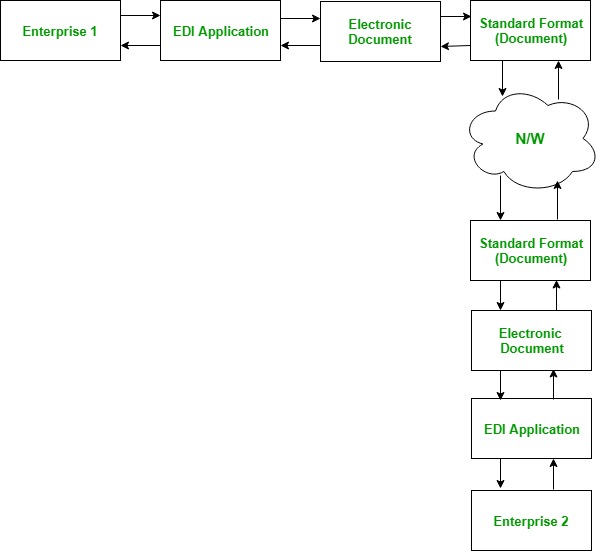
Both the enterprises have EDI applications installed in their systems. Enterprise 1 uses its EDI application to generate an EDI document that it want to share with the other enterprise. The format of this EDI document must be the standard format that has been decided by the two enterprises for sharing EDI documents during their deals. This document is shared with the other enterprise over the network. The document is received by the Enterprise 2 in the standard format on the EDI application. This is how the two enterprises exchanges business documents electronically and minimizes or eliminates the human interventions.
Advantages:
- As it is direct computer to computer transaction system, it is high speed.
- Due to reduced human intervention, it is very accurate.
- Simple to use.
- Highly secure.
- Reduction in paper work.
- Cost effective.
Share your thoughts in the comments
Please Login to comment...