DNS Spoofing or DNS Cache poisoning
Last Updated :
20 Apr, 2023
Prerequisite – Domain Name Server
Before Discussing DNS Spoofing, First, discuss what is DNS.
A Domain Name System (DNS) converts a human-readable name (such as www.geeksforgeeks.org) to a numeric IP address. The DNS system responds to one or more IP-address by which your computer connects to a website (such as geeksforgeeks.org) by using one of the IP-address.
There is not only one DNS server. There are series of DNS servers used to resolve the domain name. DNS uses cache to work efficiently so that it can quickly refer to DNS lookups it’s already performed rather than performing a DNS lookup over and over again.
Although DNS caching increase the speed of the domain name resolution process But the major change in the domain then takes a day to reflect worldwide.
DNS Spoofing means getting a wrong entry or IP address of the requested site from the DNS server. Attackers find out the flaws in the DNS system and take control and will redirect to a malicious website.
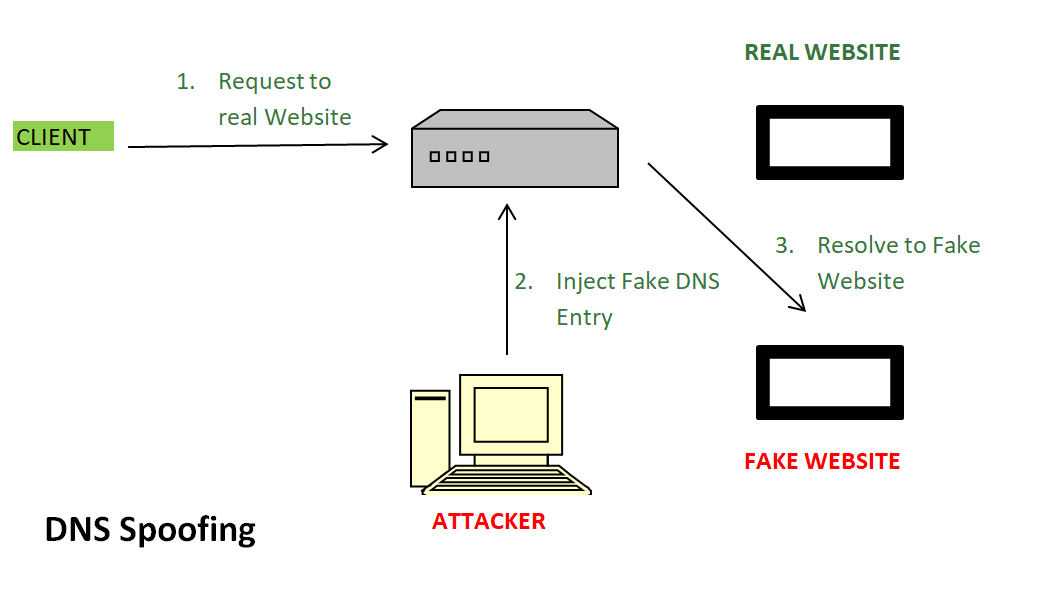
In above image –
- Request to Real Website: User hits a request for a particular website it goes to the DNS server to resolve the IP address of that website.
- Inject Fake DNS entry: Hackers already take control over the DNS server by detecting the flaws and now they add false entries to the DNS server.
- Resolve to Fake Website: Since the fake entry in the DNS server redirect the user to the wrong website.
To Prevent From DNS Spoofing –
- DNS Security Extensions (DNSSEC) is used to add an additional layer of security in the DNS resolution process to prevent security threats such as DNS Spoofing or DNS cache poisoning.
- DNSSEC protects against such attacks by digitally ‘signing’ data so you can be assured it is valid.
- Implement Source Authentication: Source authentication can be used to verify that the source of the DNS request is legitimate. This can be achieved using techniques such as IPsec or TLS to authenticate the requestor and ensure that the request has not been tampered with in transit.
- Use Response Rate Limiting: Response Rate Limiting (RRL) is a technique that limits the rate at which a DNS server responds to queries. This can help prevent DNS amplification attacks by reducing the number of responses that can be generated by a single query.
- Implement DNS Filtering: DNS filtering can be used to block traffic to known malicious domains or IP addresses. This can be done using DNS blacklists or whitelists that are regularly updated with known malicious or legitimate domains.
- Use DNS Monitoring and Analysis: DNS monitoring and analysis can be used to detect anomalies in DNS traffic that may indicate a DNS spoofing attack. This can be achieved using techniques such as packet capture and analysis, log analysis, or real-time monitoring of DNS traffic.
- Regularly Update DNS Software and Patches: Regularly updating DNS software and patches can help prevent known vulnerabilities from being exploited by attackers. This can be achieved by regularly checking for updates and patches from the vendor or using automated patch management tools.
Share your thoughts in the comments
Please Login to comment...