Difference between Tokenization and Encryption
Last Updated :
07 May, 2023
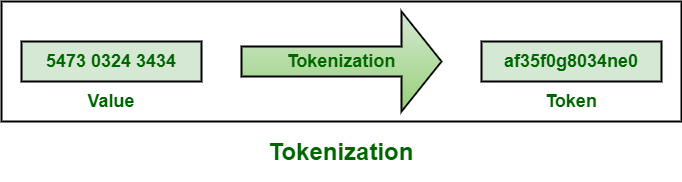
1. Tokenization :
Tokenization, as name suggests, is basically a replacement technique that replace sensitive data with randomly generated code that is known as token. Here, token generally serves as references or placeholders for original data. It simply preserves feel and format of data and also preserves privacy of data subject. It is often used for credit card processing for added security.
Example :
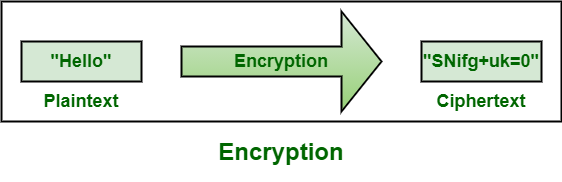
2. Encryption :
Encryption, as name suggests, is a process that combines mathematical algorithm and some other secret information to transform or convert data in a way that is essentially impossible to reverse without appropriate key. It simply uses algorithms to convert plain text information into non-readable form known as cipher text. It can also be reversed so that authorized person can view and use raw and sensitive data. It is considered most effective way to achieve data security.
Example :
Difference between Tokenization and Encryption :
|
Tokenization
|
Encryption
|
| It is a process of turning sensitive data into non-sensitive data usually known as tokens. |
It is a process of encoding message, data, or file so that it can be accessed and read only by certain people. |
| It is important because it helps to reduce risk from data breaches and build trust with customers. |
It is important because it helps to protect private information or sensitive data, and enhance security of communication among servers and client apps. |
| Its main objective is to swap out or substitute sensitive data such as payment card or bank account numbers with randomized number in same format but without any intrinsic value of its own. |
Its main objective is confidentiality such as concealing content of message by translating it into code. |
| It can be offered only via web services. |
It can be offered both locally and as web service. |
| It is best suited for structured data fields and is therefore mostly used to protect sensitive data in payment processing systems like credit card information or social security numbers. |
It is best suited for unstructured fields or databases that are not stored in multiple system and for protecting files such as entire files or emails, and also supports structured data such as payment card numbers. |
| It is difficult to exchange data because of access to token database. |
It is easier to exchange data because on can access original data if needed with decryption key. |
| It uses tokens to protect or secure data. |
It uses secret keys to protect or secure data. |
| In this, if somehow token is intercepted, then it cannot be used to guess real values. |
In this, if somehow key is intercepted, then too it can be used to decrypt all data it was used to secure. |
| It is an irreversible process. |
It is a reversible process. |
| Tokenization is generally considered to be more secure |
Encryption is less secure |
| The output of tokenization is a token, which is a unique identifier that represents the original data. |
The output of encryption is ciphertext, which is the scrambled form of the original data. |
| Tokenization is a one-way process that cannot be reversed to the original data. |
Encryption is a reversible process that can be decrypted back to the original data using a secret key or algorithm. |
| It generates token value randomly for plaintext and stores mapping in database. |
It scrambles data so that only authorized parties can have access to data. |
Share your thoughts in the comments
Please Login to comment...