Today, the Internet is the most-used human-built technology and even growing more with its full potentialities day by day. This Internet is not only an important real-life technology but also the backbone of this largest networking system in the world today. Though, the Modern Internet is not only limited to the general using-purposes, but it also becomes a part of the crime world too.
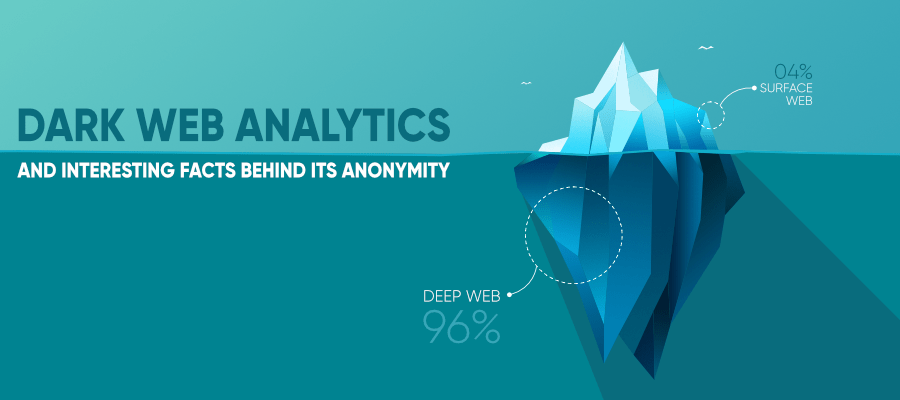
Many people today are aware of this fact that the Internet is divided into different layers in which each layer of the Internet has its specific purpose of existence. The most common and first part is the Surface Web, therefore the Deep Web comes and at last, the most hidden part of the Internet aka the subset of the Deep Web comes which is named the Dark Web.
Difference Between the Layers of the Internet
Before delving into the Dark Web, we should have to know first how deep it is actually!! The Internet has three layers such as Surface Web, Deep Web and Dark Web(a derived subset of Deep Web.) If we try to imagine the Layers as a simple Internet Architecture then we can see that these layers are like almost positioned in a linear sequence where the Surface Web belongs to the upper level, Deep Web in the middle level and at last the deeper you dig you will get the tail of Dark Web. These three layers of the Internet carry different working features. All the working qualities are described as follows:
1. Surface Web: The Common Accessible Level of the Internet
Surface Web is the top-most layer of the Internet. Everything we surf on the Internet for our daily needs are lying under the Surface Web. This surface web is the most commonly used surfing area, everything here is publicly accessible, always traffic-crowded by all types of visitors daily and the comparatively safer portion of the Internet, built for every regular user/common people. Surface Web is an open-portal, easily available & accessible for anyone from any corner of the World using our regular browsers and this is the only layer whose almost every information is indexed by all the popular Search Engines. In-short, Surface Web is the only Default user-accessible part of the Internet. We can access the Surface Web using the Popular Search Engines like Google, Yahoo, Bing, DuckDuckGo, using the popular browsers like Google Chrome, Mozilla Firefox, Internet Explorer, Netscape Navigator, Microsoft Edge, Opera, UC Browser and more. Surface Web is the purest part of the World Wide Web. Here, the HTTP/HTTPS, TCP or UDP protocols and SSL(Secure Socket Layer)/TLS(Transport Layer Security) Certified websites are found.
The Surface Web is filled with plenty of contents indexed by its automated AI-based Web-Crawlers, those contents are the several types of website URLs, lots of images, videos, GIFs, and such data or information are indexed in the large databases of those Search Engines respectively. These contents are indexed legally and verified by Search Engines.
The big Irony is- It is impossible for a person in one life to surf everything, to know, to learn, to see and to catch in mind or to understand all those information which are available and accessible on the Surface Web!!!!. Because the Surface Web itself is a large area of the Internet, increasing constantly by its huge amount of data-indexing. But the most surprising factor is: As per the basic measurement of the Internet Layers, concerning its data quantities, this Surface Web is the only 4% of the Total Internet!!. Yes, only this 4% is considered as the Surface Web and still, it seems to be like a limitless Internet Web Layer for us, having an uncountable amount of data indexed!!. After the surface web, the rests 96% which is referred to be as the deeper side and hidden part of the Internet is called the Deep Web.
2. Deep Web: The Deep Web-Part Under the Surface Web
The Deep Web arises just where the Surface Web ends. The Deep Web is the deeper part of the Internet. It is the collection of several types of confidential information which consists of the Database information belonging to several Schools, Colleges, Universities, Institutes, Hospitals, Important or Emergency Centres, Voter/Passport details of common people belonging to any Country, Government Offices and Departments, Non-Profit or Non-Government Organizations(NGOs), Multi-National Companies(MNCs), Start-ups/Private Corporations and Local Agencies. Alongside it, the deep web is also the mass storage of all the website-oriented(belongs to Surface Web) server-side information and the huge collection of the database-stacks which are filled with sensitive data regarding online admin-portals/personal-profiles/customer-account details/usernames/email-ids and several Social Media profile-credentials, different companies’ premium/free user-subscription data or premium membership details, money transaction records of many websites, Admin Panel/C-Panel of a website with its database-credentials, political or even the Government-related files(banned publicly), forever closed investigation files or police cases, forbidden torrents with pirated videos, breaching of data or leaked information of any company or website. Some very rare confidential information like most debated or discussed and high-demanded journals or secret/banned research papers belonging to any unpublished and unknown resources, pirated software or a website’s database-oriented files, the Govt. files which are not allowed to be shown publicly, etc.
The Deep Web is not an illegal space to surf but it is not also an open-accessible network. So that, it will be considered as illegal only if any kind of unusual activity, any kind of criminal offense or paralegal activities are done without legal permission. It is the most sensitive part of the Internet, not indexed by Search Engines. In true words, this part is not allowed to be indexed on Search Engines to show publicly. It is the only accessible area to its respective owners who has the proof of having the needed credentials or permissions to access any database information. Journalists and Researchers, Ethical Hackers especially the Forensic department officers, the Database Administrators(DBA) who are allowed to access and manipulate the databases, having the legal permissions given by its owner, the Government Agencies and some partially permitted, condition-applied visitors are granted to access information in this Deep Web to receive such confidential information for their needs. Journalists often visit this area to collect any kind of Political preferences, crime-cases, Government issues, any closed file history, black history of any Royal Family, Military/Defence agency news, illegally leaked or banned Research Papers and much more necessary information.
3. Dark Web: The Most anonymous and deepest part of the Internet
The Dark Web is such a part of the Internet which still makes so much confusion among experts and researchers till today. As it is a very sensitive part of the Internet where mysterious activities are happening all the time and loaded with full of such content which is not imaginable for a normal person. It has been proven by the Scientists and Experts that the 96% of the Internet is hidden in which 90% is considered to be as the Deep Web and the rest 6% is called the most hidden, anonymous, dangerous and the darkest part of the Internet, named as the Dark Web. Though in some cases, several confusions have been found while measuring the layer/boundaries of Dark Web to know its actual size of existence under the Internet, inside the Deep Web.
Because the size of the Dark Web is not constant as there are some other different results are found on the Internet from several types of experimental conclusions, case studies, web-analytical statistics with the probability of the recorded traffics from the regular visits to the Dark Web “Onion URL” sites, many records of uploading/downloading/peering or transferring data and the bitcoin-transactions from one site to another site through the dark web portals in the form of encrypted files whose records are received from different proxy servers, moreover Cyber-crime investigation reports including carding, data bypassing, sim swapping, encrypted file’s records, gathering information and statements from the different Internet researchers, experts where this changeable size of the Dark Web has been noticed.
The main reason is, all the illegal websites often pass their network-data packets or destination server-requests through the proxy servers in such an encrypted format where the records of those websites traffic often get lost due to the inability of catching all the acknowledgment signals back from the requesting servers in real-time by investigators and researchers. So that reason, several times after examining and researching on it, different reports have been found year by year because of this anonymity. For example, some ethical hackers who are also dark web specialists for investigation purposes and forensic experts regarding the same, have also claimed that Dark Web lies only 0.01% of the Deep Web as per the result of 2018. Though there are some other else also.
Why the Amount of Portion of Dark Web is Changeable?
The Dark Web is the most anonymous place of the Internet, full of mysterious contents. The surprising contrast between the Surface Web and Dark Web is- The Surface web is only the 4% or a lesser amount of portion on the Internet, still for one person it seems to be full of uncountable contents and information to surf the whole Surface Web whereas the Dark Web is larger than the Surface Web but still can’t be surfed properly or easily, nobody can perfectly measure its amount of contents and size. Especially for the common people, it is almost impossible to get access to this web without having any dark web link or accessible URL or experience to surfing it. Because Dark Web is not a static area of the Internet like the Surface Web. Most of the area here is full of illegal activists and criminals and those criminal activities are generally done through the “.onion” suffix added URL/website (Though there are several kinds of URLs there now).
Most of the illegal sites here are temporary for use or has been opened shortly to visit. Means, like in Surface Web, most of the websites are officially launched with legal permission from the respective authority and are 24*7 hours active, which means we can open those websites whenever we want as the working servers behind those websites are always active to control the site’s availability to the public. But in the case of Dark Web, the illegal URLs are launched either from a personal computer of a criminal or the computers which are being operated by any private agencies or by secret groups or from the illegal organizations involved in this fields whose websites become active for a particular time and still opened until their illegal assignments/purposes are fulfilled. After completing all illegal tasks, these websites getting closed by them for a certain time and again get available when they have to do their next illegals tasks. Between this duration of time of getting closed and opened, these websites usually don’t leave any traces of their existence and can’t be tracked easily. This is a common trick by Cyber-criminals inside the Dark Web to get rid of the Forensic officers and ethical hackers.
The most interesting fact is here- Because when cyber-crime investigators like ethical hackers, cyber forensic officers dive into the Dark Web to catch the criminal by tracking those illegal websites, they often get nothing most of the time, they just see a non-existing URL. It happens due to the probability of time and period that doesn’t match often for both the Cyber officers and Cyber-criminals to meet in real-time. So, it gets too hard to trace their illegal activities through the dark web links. Most often!!.
The Black Hat Hackers here are the cleverest persons if somehow they get any clue of any tracking information by the Cyber Police or the currently running investigations of Cyber officers!!! What the black hat hackers do then?!! They simply close the illegal URL immediately, totally delete its database, even delete the whole URL and after a long period, understanding the circumstances, they get started with a new URL with a new identity from different proxy servers and with new databases but they often keep the backup of previous database information if needed. That’s why investigators face difficulties to catch the cyber crimes in the hidden dark web. The URLs don’t stay in the loop for a long time. They are like coming and going URLs!!
Now, this incident happens all-time in the Dark web with its full potentialities of getting up and down. Here, running websites can be closed suddenly, then suddenly can be reopened or recreated. Even sometimes, is has been seen by the forensic experts, suppose a criminal is working through a single website, consisting of several types of illegal tasks or services. After a certain period, just to get rid of the investigators from tracking his URL location, the criminal will shut down his site, therefore they will create three or four new websites with a distribution of those illegal services separately. That means, each newly created website is for only one service and will get shut down after all of it done.
Meanwhile, facing instantly and winning over the difficulties the Cyber-security officers and other Ethical Hackers have been able to trace and catch a lot of criminals inside the Dark Web. Many illegal activities like carding, drug selling, bets, URLs, servers have been prevented by the U.S. Cyber Officers. Especially the U.S. Government has its big role to investigate and catching all those culprits in red hand.
So these increasing and decreasing of dark web crimes, up and down of dark web traffics, even due to the lost traffics and the different number of site visits for different times became the reasons why Dark Web is getting sometimes confusing to be measured by the experts and researchers.
Getting Access to Surf Dark Web or How Ethical Hackers Get Access to it?!!
As you know, in normal ways, using browsers like Chrome or Firefox is worthless to get access into the dark web but here the special type of browser named TOR can do it easily. So what is TOR?
TOR stands for “The Onion Router”. It was first launched as TOR Project only for the U.S. Defence Organization to send and receive the private information from their spy anonymously. So that they can transfer their secret information and can do private communication through encryption between the way of several proxy servers anonymously by the TOR browser. This TOR was developed at Massachusetts by computer scientists Roger Dingledine, Nick Mathewson and five others in a non-profit organization named TOR.Inc.
After a certain period, it was launched for public use as it was also funded by the general public through donations and other sponsored organizations like the US Department of State Bureau of Democracy, Rose Foundation for Communities and the Environment, Mozilla, Open Technology Fund, Swedish International Development Cooperation Agency, etc.
Working Methodology of TOR browser in a Nutshell
TOR works through several Proxy Servers. Proxy Server is used here to hide your original IP address and to pass your destination-server request in an encrypted form. There are several types of Proxy Servers that work differently whereas the Proxy used for TOR is to cover and protect your original IP address with the different layers several IP addresses of different locations. Now here, TOR uses more than one proxy server. It creates a chain or circuit of Proxy Servers which is known as Proxy-chain or Proxy-circuit and will be working from your personal computer to pass over your request to the destination-server along with your requested data, that will be transferred in an encrypted format.
Your requested data will be encrypted in N number of encryption which will be passed through the N number Proxy servers. Now customization of proxy circuit and encryption is possible. Professional uses Virtual Private Network before activating the TOR. It is highly recommended not to minimize or maximize the TOR Window span otherwise chances to get tracked arise. The Dark Web comprises only 3% of the traffic in the TOR browser.
Rumor Behind Launching TOR Browser Public
Before deciding it to launch publicly, there is an interesting fact also behind it!! You can say it a rumor also!! i.e. after having a long time usage of TOR by the U.S. Defence Department, the U.S. Government planned to launch TOR as public use for free intentionally. A piece of leaked information revealed that there was a hidden purpose of the Government to build a trap for the dangerous Cyber-criminals and for the Black hat Hacktivists of America to get them in red hand and also to investigate throughout the World Wide as much as possible to catch the Cyber-culprits. It was only possible by providing a large space of Internet Anonymity to them. But the question is why?!!
Because, before TOR came for public use, various Cyber Criminals especially the black hat hackers used to create their temporary private Internet from their server or a hacked Internet Service Provider to keep themselves anonymous and their activities secret as much as possible. They don’t use the public Internet to do the crimes in fear of getting arrested so easily, in purpose to keep themselves private all-time with full control over their Internet. The U.S. Government or the Government of other countries know it well but were not capable of stopping those private Internets or trace those private networks to get the criminals in hand. It was not possible to locate the IP of all those temporarily active anonymous Internets at the same time because the criminals also used to apply Proxy Servers over them. So they made TOR became public for all the common people but especially as a kind of trap to provide the anonymity with the free Proxy Server connections including all those cyber-criminals with hidden identity between the common public to become anonymous without any hard work and to let them do their cyber-crimes in a normal flow which made it easy for the U.S. Forensic Officers and ethical hackers to trace the Cyber Criminals by trying to spying their traffics of sites which works inside the U.S. Government’s developed anonymous browser!!
The U.S. Government made the TOR as the key and lock to catch the Black Hat Hackers and Drug Sellers through TOR. The whole mechanism of TOR was in hand of the U.S. Government. So the Government can keep an eye on those Cyber Criminals easily to arrest them as soon as and as much as possible. A new trap to let the Cyber Criminals do their crimes by which the Government Officers can identify the level of crimes.
But by time to time, the level and the ways of Cyber Crimes has been changed severely, the chances to catch the Cyber-criminals under the dark web also get harder.
More Analytics and Facts on Dark Web
1. The popularity of Dark Web and TOR Browser: As previously mentioned above, Dark Web is the subset of Deep Web that lies in the Deep Web as the most hidden part of the Internet and not publicly accessible by the traditional browsers in the general ways of searching. In that case, experts use TOR Browser which is now used for only Dark Web surfing and mostly for the Dark net activities.
As time passes, common people are also getting aware of Dark Web and hearing the Cyber-crimes happening here desperately from various sources. Now few of them, who are neither criminal nor ethical hackers, eagerly downloading the TOR browser into their devices just in curiosity to get access and to experience the black side of the Internet without even knowing the right path to surfing it and the danger in it!! Curiosity is good for knowledge but the Dark web is something different from it!! Dark Web is not working totally on knowledge but skills and experiences as that silly curiosity cause an accidental attempt to the crime world for some people badly!! As TOR becomes public use for free, it attempts for some people to suffer from cyber-crimes due to landing upon a wrong site, being trapped. Even in android versions, there are two famous applications like ORBOT & ORFOX work as the gateway to access the Dark web from android. But it should not be surfed from Android until you have to surf for a specific and good-for-use dark web URL. TOR is getting now the only one most popular browser to surf the Dark Web.
2. Accessing Dark Web is illegal or not?!: TOR is not illegal or getting access to the Dark Web is not illegal because there are lots of professionals like journalists, ethical hackers from forensics, researchers, writers, some readers, international political groups or agencies surf the dark web for their needs. But the irony is, here the number of illegal activities heavily increases in different forms of crimes where if one type of crime is getting caught and banned by forensic officers, another type arises immediately in a new form. This makes the dark web getting involved in dangerous to more dangerous cyber-crimes all times.
The more black hat hackers arise, the more crimes are happening here. On another hand, unlike we use Search Engines such as Google, Bing, Yahoo in Surface Web, there is no specific Search Engine for Dark Web that you will start surfing anything in the Dark Web by just typing the keyword and then clicking the “Search” button!!! To get access there, you need a specific URL of the onion suffix added. Now for an unprofessional or inexperienced person, if they somehow find out or receive any kind of dark web-accessible link from unknown sources to surf it through the TOR browser, it is difficult for them to understand first if the URL will lead to any right or wrong site!! Because most of the site there is illegal, security less and there is no guarantee what will happen after. There is no “HTTPS” protocol or SSL certified websites to determine whether the site is good or bad!! This is totally outside of WWW.
If the URL is found to be bad, URL visitors can get hacked, their device and all personal data or activities can get hacked, can be threatened, can be forced by black hat hackers to do any illegal task unconsciously at life risk even!!!! Whatever can be happened!! Even sometimes, an experienced professional also get trapped there!! It is not being said that attempting dark web is illegal but need a surety what URL you are going to visit. A lot of daily readers exist there who just like to read confidential articles or reports of international news. Facebook has also its .onion URL there!! Also, Dark Web has some social media sites which are temporary!! There are some specific but temporary search engines also there but not trustworthy like Hidden Wiki- it consists of secret journals that are not open to anyone.
3. Types of crimes happening here: Black Hat Hacking, Bitcoin selling, hacked Social Media account’s IDs and Password Selling of popular or target-based people, Credit or Debit Card’s Number selling(Carding), Driving license selling, Degree or Diploma’s falsified certificate selling, Child Pornography, Forbidden Animal selling, Illuminati or paranormal information transferring, illegal Bitcoin transactions and encrypted files including malware, ransoms, viruses selling, black market medicines selling which are illegal or not allowed for sale in general.
Especially Drugs and Weapon selling, Illegal Property selling, Contacts with the profile of Killers, Hit-man and many more. All of these Dark-net activities are done basically by those cyber-crime professionals (Most of them are Black Hat Hackers/Cyber Criminals) who are selling all the forbidden/restricted/illegal items anonymously to gain a huge profit from the underworld circumstances, takes place in the Dark Web, which can’t be achieved publicly in general ways.
4. What happens after stealing the public information under the Dark Web? Generally, the credentials of target-based Social Media profiles, Personal or Business Emails, stolen Net Banking Details, Credit or Debit Cards details which have been stolen using skimmer in the ATM(s), Government Organizations or Private agencies or IT Industrial related Projects, Confidential files, Database System Information are at first hacked by black hat hackers and then all these information are sold in an encrypted format to its respective buyers anonymously under the Dark Web. These pieces of information are stolen through the networking system in the Surface Web by several Cyber Attacks to get its full access. These data are bypassed in the Dark Web simultaneously. Information Stolen occurs through these types of cyber-attacks:
- Phishing Attack: Sending fake emails which are pretending to be real to create a trap for the victims to steal private credentials.
- Spoofing: Pretending to be real, spoofing means to make fake calls with fake identities to steal personal information, using social engineering.
- Click-Jacking Attack: Almost like phishing but it leads to a fraud application ( or a duplicate website which resembles to the UI/UX of the original website) to steal credentials. In most cases, it steals the credential details/ any official background details of the victims.
- Spamming: Spam calls, messages, emails.
- Ransomware Attack: It is a type of malware which can be installed in a victim’s computer to encrypt all the file and to threat the victim for a certain amount of money to give the hackers otherwise the information will get sold in the Dark Web.
- RAT: Remote Access Trojans are types of Trojan that infects a computer by leaving a backdoor in it for the hacker to get control over that computer remotely.
- Social Engineering: A way to trick the victim’s mind to get his personal information or credentials of the bank account or any other profile.
- SQL Injection: SQL Injection is used to snatch information of a Database of any website or application.
- Data Breaching: Most happens in the IT Industries where information gets leaked in the wrong hand.
- Brute Force Attack, Dictionary Attack, Rainbow-Table Attack, Water hole Attack: These are used to hack victim’s credentials.
- Distributed Denial of Service Attack, Smurf Attack: Used to turn down any website server.
- False Transactions: False Gateways claiming to transfer your money securely.
These are all different ways to steal information from victims in the Surface Web which are then sold in the Dark Web in the form of Cryptocurrency often. There are other ways too!!
What Lies in the Depth of the Darknet?
The hidden nature of The Dark Web can make it difficult to know exactly what goes on there, but it is frequently associated with financial fraud, file sharing and data breaches, including the sale of details from identity theft.
According to the research results from TorStatus, TechRepublic, WIRED, Intelliagg report, SecureWorks Reports, BBCiWonder the following outcomes has been discovered. This record of activities has been found under the dark web
- File Sharing- 29%
- Leaked Data selling- 28%
- Financial Fraud- 12%
- News and Media- 10%
- Promotion of Illegal items- 6%
- Discussion Forums(International Articles with the Government forbidden topics)- 5%
- Drugs selling- 4%
- Internet and computing by Dark Web visitors(Except criminals who are random or occasional visitors just)- 3%
- Hacking- 3%
- Selling of Weapons- 0.3%
Notice that the sum of the percentage is greater than 100% as some of the websites are existing in multiple categories and randomly changing its domain.
So these are all the Analytics of the on the Dark Web with lots of interesting facts which reveal this moral that Dark Web is Dark Side of the Internet not for its Anonymity but because of the criminal minds who are abusing it!! . Staying away is safe always because it is the place, filled up with criminals and their traps. Government Officer, Police, Cyber Security experts are digging the depth on this web to prevent these crimes as much as possible.
Share your thoughts in the comments
Please Login to comment...