Zero Knowledge Proof
Last Updated :
11 May, 2022
Zero Knowledge Proof (ZKP) is an encryption scheme originally proposed by MIT researchers Shafi Goldwasser, Silvio Micali and Charles Rackoff in the 1980s.
Zero-knowledge protocols are probabilistic assessments, which means they don’t prove something with as much certainty as simply revealing the entire information would. They provide unlinkable information that can together show the validity of the assertion is probable.
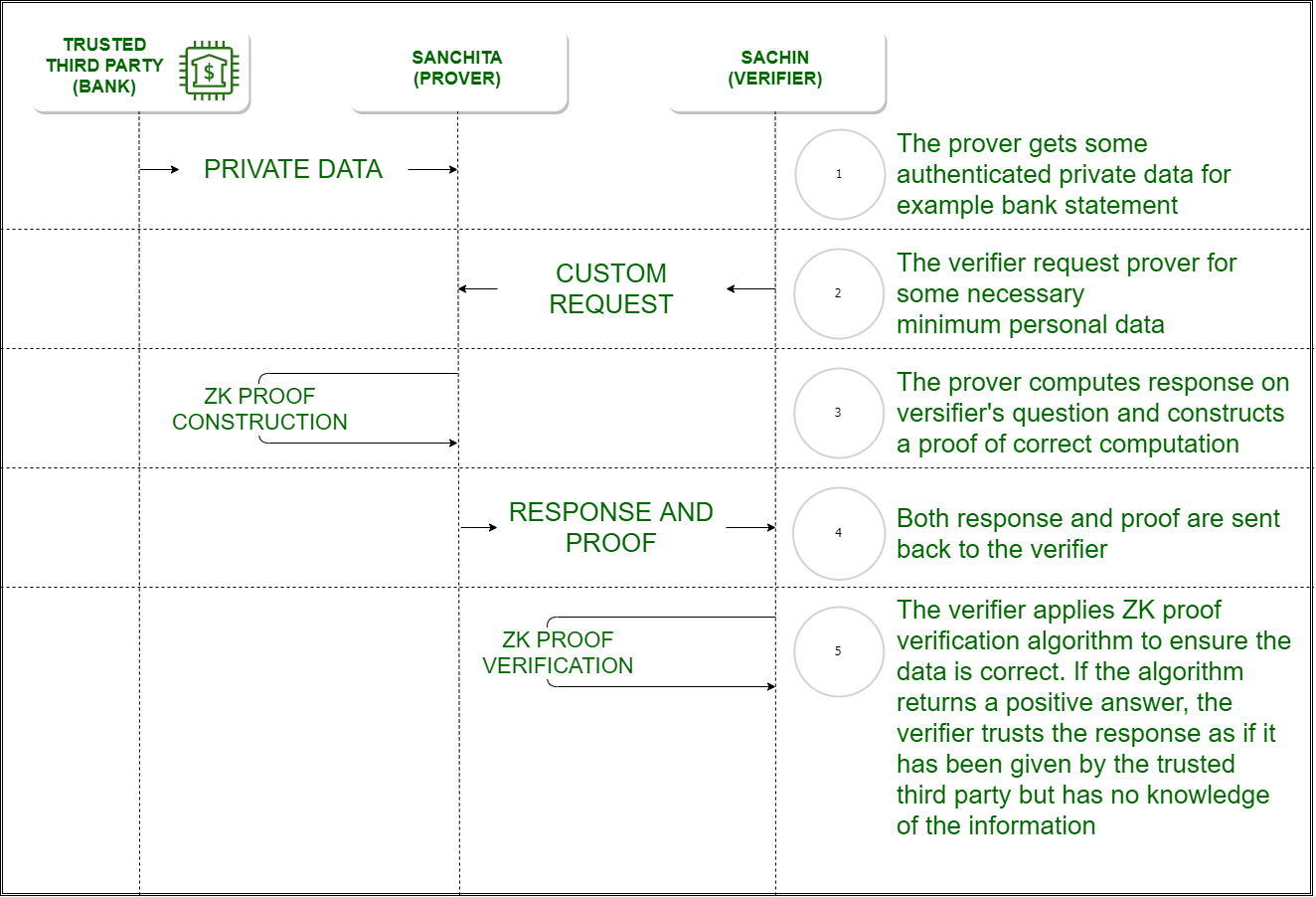
Currently, a website takes the user password as an input and then compares its hash to the stored hash. Similarly a bank requires your credit score to provide you the loan leaving your privacy and information leak risk at the mercy of the host servers. If ZKP can be utilized, the client’s password is unknown the to verifier and the login can still be authenticated. Before ZKP, we always questioned the legitimacy of the prover or the soundness of the proof system, but ZKP questions the morality of the verifier. What if the verifier tries to leak the information?
Example-1: A Colour-blind friend and Two balls :
There are two friends Sachin and Sanchita, out of whom Sanchita is colour blind. Sachin has two balls and he needs to prove that both the balls our of different colour. Sanchita switches the balls randomly behind her back and shows it to Sachin who has to tell if the balls are switched or not. If the balls are of the same colour and Sachin had given false information, the probability of him answering correctly is 50%. When the activity is repeated several times, the probability of Sachin giving the correct answer with the false information is significantly low. Here Sachin is the “prover” and Sanchita is the “verifier”. Colour is the absolute information or the algorithm to be executed, and it is proved of its soundness without revealing the information that is the colour to the verifier.
Example-2: Finding Waldo :
Finding Waldo is a game where you have to find a person called Waldo from a snapshot of a huge crowd taken from above. Sachin has an algorithm to find Waldo but he doesn’t want to reveal it to Sanchita. Sanchita wants to buy the algorithm but would need to check if the algorithm is working. Sachin cuts a small hole on a cardboard and places over Waldo. Sachin is the “prover” and Sanchita is the “verifier”. The algorithm is proved with zero knowledge about it.
Properties of Zero Knowledge Proof :
- Zero-Knowledge –
If the statement is true, the verifier will not know that the statement or was. Here statement can be an absolute value or an algorithm.
- Completeness –
If the statement is true then an honest verifier can be convinced eventually.
- Soundness –
If the prover is dishonest, they can’t convince the verifier of the soundness of the proof.
Types of Zero Knowledge Proof :
- Interactive Zero Knowledge Proof –
It requires the verifier to constantly ask a series of questions about the “knowledge” the prover possess. The above example of finding Waldo is interactive since the “prover” did a series of actions to prove the about the soundness of the knowledge to the verifier.
- Non-Interactive Zero Knowledge Proof –
For “interactive” solution to work, both the verifier and the prover needed to be online at the same time making it difficult to scale up on the real world application. Non-interactive Zero-Knowledge Proof do not require an interactive process, avoiding the possibility of collusion. It requires picking a hash function to randomly pick the challenge by the verifier. In 1986, Fiat and Shamir invented the Fiat-Shamir heuristic and successfully changed the interactive zero-knowledge proof to non-interactive zero knowledge proof.
Share your thoughts in the comments
Please Login to comment...