W3brute – Automatic Web Application Brute Force Attack Tool
Last Updated :
14 Sep, 2021
Brute-Forcing is an automated process through which Usernames, Passwords can be detected by querying the possible credentials on the target domain login pages. We can also brute-force hidden files and directories on the target server by specifying the possible word list which contains the phrases that will be tested on the domain. This process saves a lot of time for the tester as manual testing can be very unreliable. W3brute is the tool used for brute-forcing the credentials, admin pages, files, and directories on the target domain server. It also supports Vulnerability scanning like Testing the target domain for SQLi security flaws. A W3brute tool is an automated tool developed in the Python language. W3brute tool is free and available on GitHub. This tool is also Open-source so anyone can contribute to the repository and add some new features to it.
Note: Make Sure You have Python Installed on your System, as this is a python-based tool. Click to check the Installation process: Python Installation Steps on Linux
Installation of W3brute Tool on Kali Linux OS
Step 1: Use the following command to install the tool in your Kali Linux operating system.
git clone https://github.com/mlynchcogent/w3brute.git

Step 2: Now use the following command to move into the directory of the tool. You have to move in the directory in order to run the tool.
cd w3brute

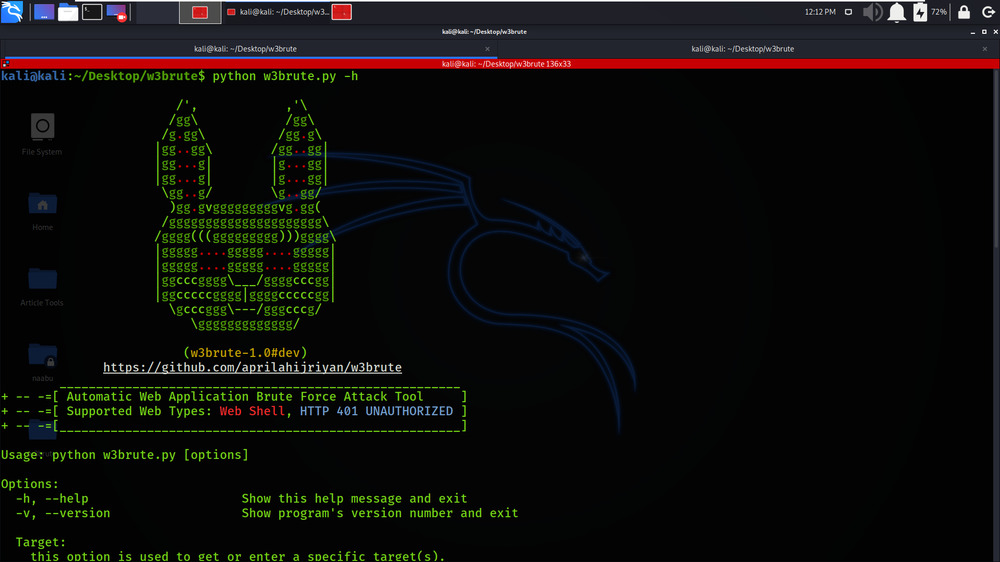
Step 3: All the dependencies have been installed in your Kali Linux operating system. Now use the following command to run the tool and check the help section.
python w3brute.py -h
Step 4: Check the version of the W3brute tool by using the following command.
python w3brute.py -v

Working with W3brute Tool on Kali Linux OS
Example 1: Basic usage
sudo python w3brute.py -t https://ide.geeksforgeeks.org/login.php
In this Example, We are performing simple Brute-Forcing on the target domain https://ide.geeksforgeeks.org/login.php


Example 2: Admin page scanner
sudo python w3brute.py -t https://geeksforgeeks.org --admin
In this Example, We are trying to brute-force on geeksforgeeks.org for finding the admin pages.


Example 3: SQL injection scanner vulnerability
sudo python w3brute.py -t http://testphp.vulnweb.com/search.php?test=query –admin –sqli-bypass
In this Example, We are testing the target domain against SQL Injection Vulnerability. We have specified the tag –sqli-bypass.


Example 4: Disable color for output text in the terminal
sudo python w3brute.py -t http://testphp.vulnweb.com/search.php?test=query –admin –sqli-bypass -nC
In this Example, We are disabling the unwanted color used while displaying the results. We have used the -nC tag for disabling color.


Share your thoughts in the comments
Please Login to comment...