Dual Mode operations in OS
Last Updated :
29 Aug, 2023
An error in one program can adversely affect many processes, it might modify data of another program or also can affect the operating system. For example, if a process stuck in the infinite loop then this infinite loop could affect the correct operation of other processes. So to ensure the proper execution of the operating system, there are two modes of operation:
User mode –
When the computer system is run by user applications like creating a text document or using any application program, then the system is in user mode. When the user application requests for a service from the operating system or an interrupt occurs or system call, then there will be a transition from user to kernel mode to fulfill the requests.
Note: To switch from kernel mode to user mode, the mode bit should be 1.
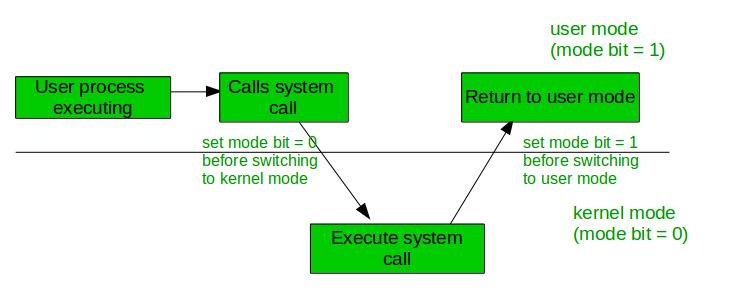
Given below image describes what happens when an interruption occurs:
Kernel Mode: When the system boots, the hardware starts in kernel mode and when the operating system is loaded, it starts user application in user mode. To provide protection to the hardware, we have privileged instructions which execute only in kernel mode. If the user attempts to run privileged instruction in user mode then it will treat instruction as illegal and traps to OS. Some of the privileged instructions are:
- Handling Interrupts
- To switch from user mode to kernel mode.
- Input-Output management.
Need for Dual Mode Operations:
Certain types of tasks do not require any type of hardware support, that’s why certain types of processes are to be made hidden from the user. These tasks can be deal separately by using the Dual Mode of the operating system.
The Kernel Level programs perform all the bottom level functions of the operating systems like memory management, process management etc, for this purpose the operating system needs to function in the Dual Mode. Dual Mode is necessary for specifying the access to the users only to the tasks of their use in an operating system.
Basically, whenever the operating system works on the user applications, it held in the user mode. When the user requests for some hardware services, a transition from User Mode to the Kernel Mode occurs which is done by changing the mode bit from 1 to 0. Also the mode bit again changed to 1 for returning back in the User Mode.
Advantages:
- Protection: Dual-mode operation provides a layer of protection between user programs and the operating system. In user mode, programs are restricted from accessing privileged resources, such as hardware devices or sensitive system data. In kernel mode, the operating system has full access to these resources, allowing it to protect the system from malicious or unauthorized access.
- Stability: Dual-mode operation helps to ensure system stability by preventing user programs from interfering with system-level operations. By restricting access to privileged resources in user mode, the operating system can prevent programs from accidentally or maliciously causing system crashes or other errors.
- Flexibility: Dual-mode operation allows the operating system to support a wide range of applications and hardware devices. By providing a well-defined interface between user programs and the operating system, it is easier to develop and deploy new applications and hardware.
- Debugging: Dual-mode operation makes it easier to debug and diagnose problems with the operating system and applications. By switching between user mode and kernel mode, developers can identify and fix issues more quickly and easily.
- Security: Dual-mode operation enhances system security by preventing unauthorized access to critical system resources. User programs running in user mode cannot modify system data or perform privileged operations, reducing the risk of malware attacks or other security threats.
- Efficiency: Dual-mode operation can improve system performance by reducing overhead associated with system-level operations. By allowing user programs to access resources directly in user mode, the operating system can avoid unnecessary context switches and other performance penalties.
- Compatibility: Dual-mode operation ensures backward compatibility with legacy applications and hardware devices. By providing a standard interface for user programs to interact with the operating system, it is easier to maintain compatibility with older software and hardware.
- Isolation: Dual-mode operation provides isolation between user programs, preventing one program from interfering with another. By running each program in its own protected memory space, the operating system can prevent programs from accessing each other’s data or causing conflicts.
- Reliability: Dual-mode operation enhances system reliability by preventing crashes and other errors caused by user programs. By restricting access to critical system resources, the operating system can ensure that system-level operations are performed correctly and reliably.
Disadvantages:
- Performance: Dual-mode operation can introduce overhead and reduce system performance. Switching between user mode and kernel mode requires a context switch, which can be time-consuming and can impact system performance.
- Complexity: Dual-mode operation can increase system complexity and make it more difficult to develop and maintain operating systems. The need to support both user mode and kernel mode can make it more challenging to design and implement system features and to ensure system stability.
- Security: Dual-mode operation can introduce security vulnerabilities. Malicious programs may be able to exploit vulnerabilities in the operating system to gain access to privileged resources or to execute malicious code.
- Reliability: Dual-mode operation can introduce reliability issues as it is difficult to test and verify the correct operation of both user mode and kernel mode. Bugs or errors in either mode can lead to system crashes, data corruption, or other reliability issues.
- Compatibility: Dual-mode operation can create compatibility issues as different operating systems may implement different interfaces or policies for user mode and kernel mode. This can make it difficult to develop applications that are compatible with multiple operating systems or to migrate applications between different systems.
- Development complexity: Dual-mode operation requires a higher level of technical expertise and development skills to design and implement the operating system. This can increase the development time and cost for creating new operating systems or updating existing ones.
- Maintenance complexity: Dual-mode operation can make maintenance and support more complex due to the need to ensure compatibility and security across both user mode and kernel mode. This can increase the cost and time required for system updates, patches, and upgrades.
Note: To switch from user mode to kernel mode bit should be 0.
FAQ:
What is the purpose of dual-mode operation?
Dual-mode operation is designed to provide a layer of protection and stability to computer systems by separating user programs and the operating system into two modes: user mode and kernel mode. User mode restricts access to privileged resources, while kernel mode has full access to these resources.
How does dual-mode operation improve system performance?
By allowing user programs to access resources directly in user mode, the operating system can avoid unnecessary context switches and other performance penalties, which can improve system performance.
What are some common privileged instructions in kernel mode?
Some common privileged instructions in kernel mode include handling interrupts, switching from user mode to kernel mode, and input-output management.
How can dual-mode operation enhance system security?
The dual-mode operation can enhance system security by preventing unauthorized access to critical system resources. User programs running in user mode cannot modify system data or perform privileged operations, reducing the risk of malware attacks or other security threats.
What are some potential drawbacks of dual-mode operation?
Some potential drawbacks of dual-mode operation include increased complexity and development/maintenance costs, security vulnerabilities, and potential performance issues due to context switching. However, these drawbacks are generally outweighed by the benefits of dual-mode operation in terms of system stability, security, and flexibility.
Read next – User Level thread Vs Kernel Level thread
Share your thoughts in the comments
Please Login to comment...