Dorks Eye – Google Hacking Dork Scraping and Searching Script
Last Updated :
16 Jun, 2022
The Dorks Eye tool is developed in the Python3 language which can easily find Vulnerable links using Google Dorks. Dorks Eye tool gathers links to web pages and applications from the Internet which reveals some information. Now this information can be sensitive data like SQL queries of web pages, usernames and passwords, bank details, and many more. Dorks Eye also supports saving the results onto a text formatted file. This tool is also available on the GitHub platform for free and is open source to use.
What is Google Dorking?
Google Dorking is the advanced search technique that shows the accurate results of our query rather than showing irrelevant stuff or some ad-containing sites. Google Dorking is so powerful that we can also get the username and passwords containing files, robot.txt files, sensitive files conf files, and many more. One of the sample dorking queries look like: /modules/vwar/admin/admin.php?vwar_root=
Note: Make Sure You have Python Installed on your System, as this is a python-based tool. Click to check the Installation process: Python Installation Steps on Linux
Installation of Dorks Eye Tool on Kali Linux OS
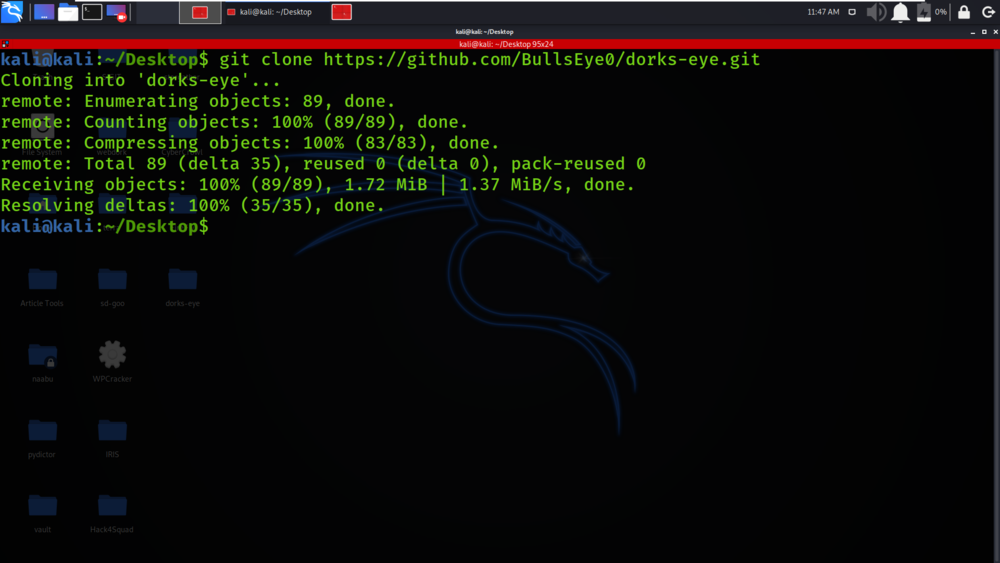
Step 1: Use the following command to install the tool in your Kali Linux operating system.
git clone https://github.com/BullsEye0/dorks-eye.git
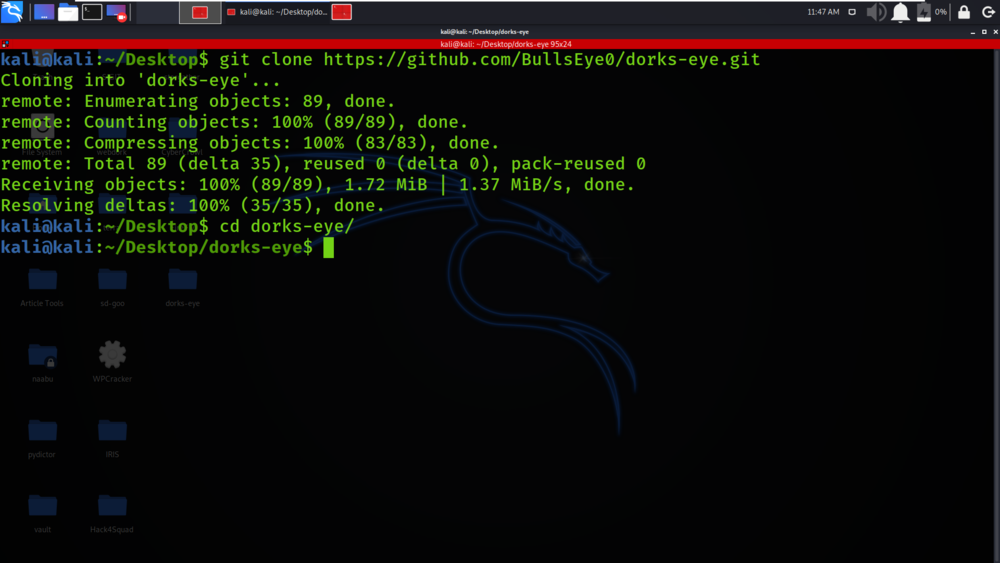
Step 2: Now use the following command to move into the directory of the tool. You have to move in the directory in order to run the tool.
cd dorks-eye
Step 3: You are in the directory of the dorks-eye. Now you have to install a dependency of the dorks-eye using the following command.
sudo pip3 install -r requirements.txt
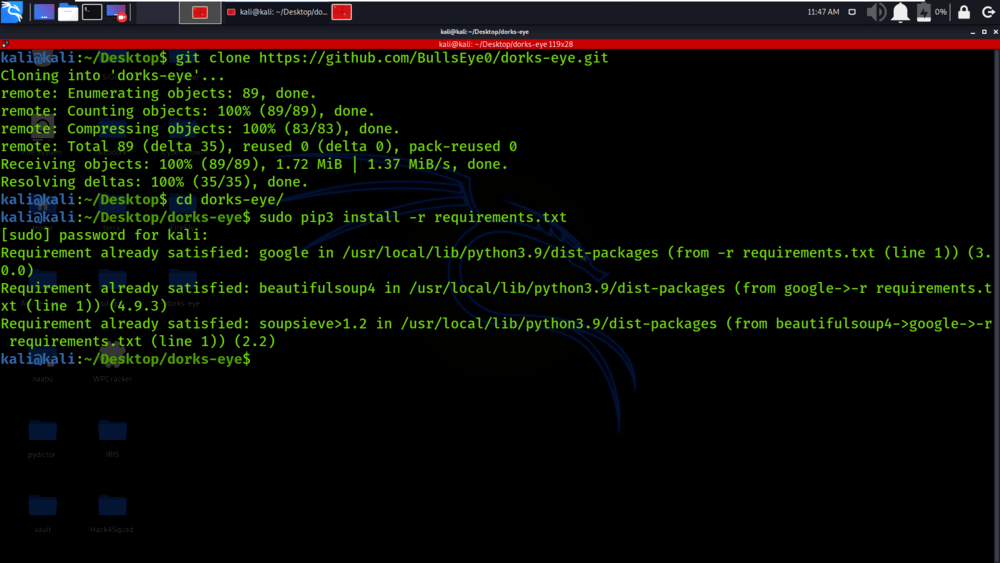
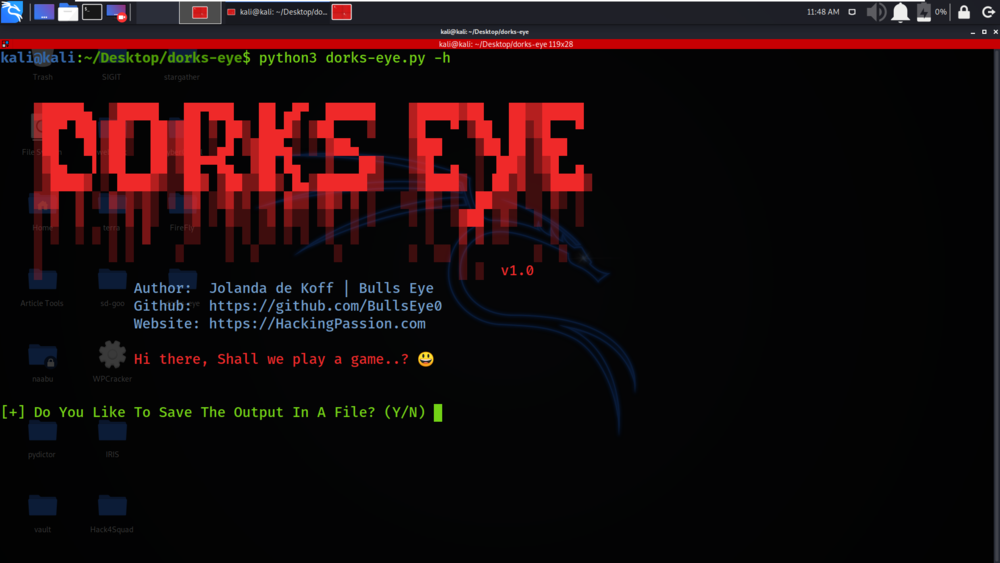
Step 4: All the dependencies have been installed in your Kali Linux operating system. Now run the tool.
python3 dorks-eye.py
Working with Dorks Eye Tool on Kali Linux OS
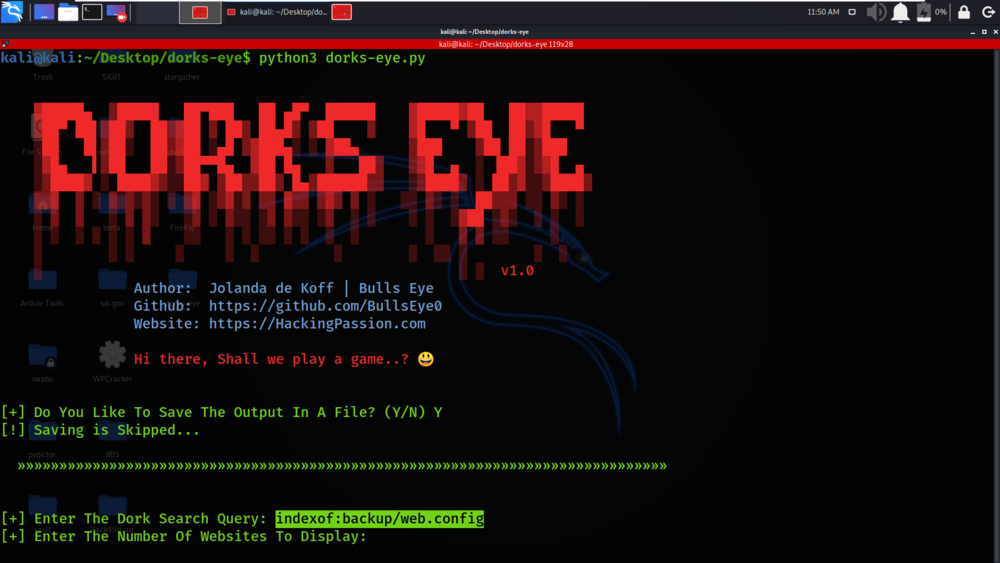
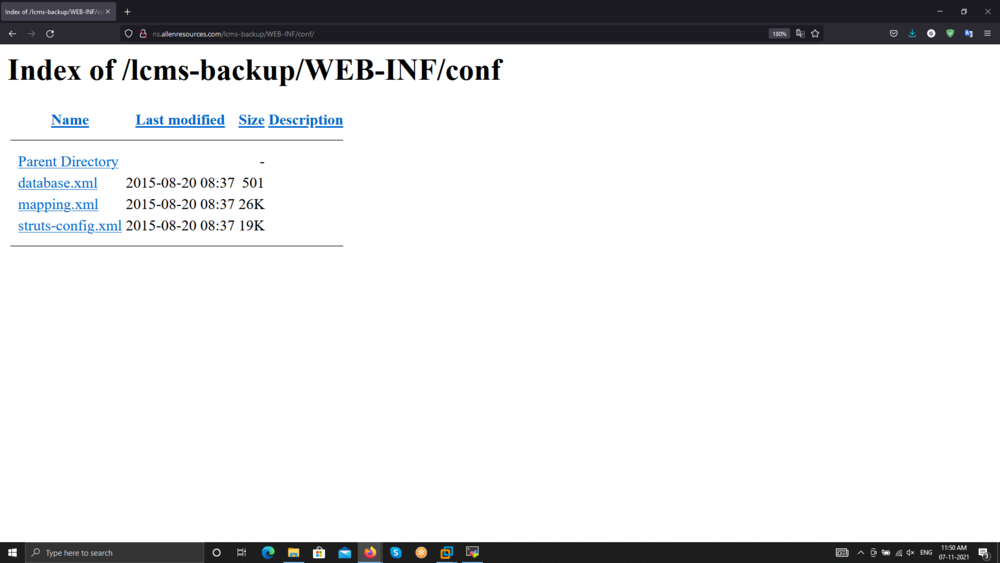
Example/Usage: Finding config files by using dork query
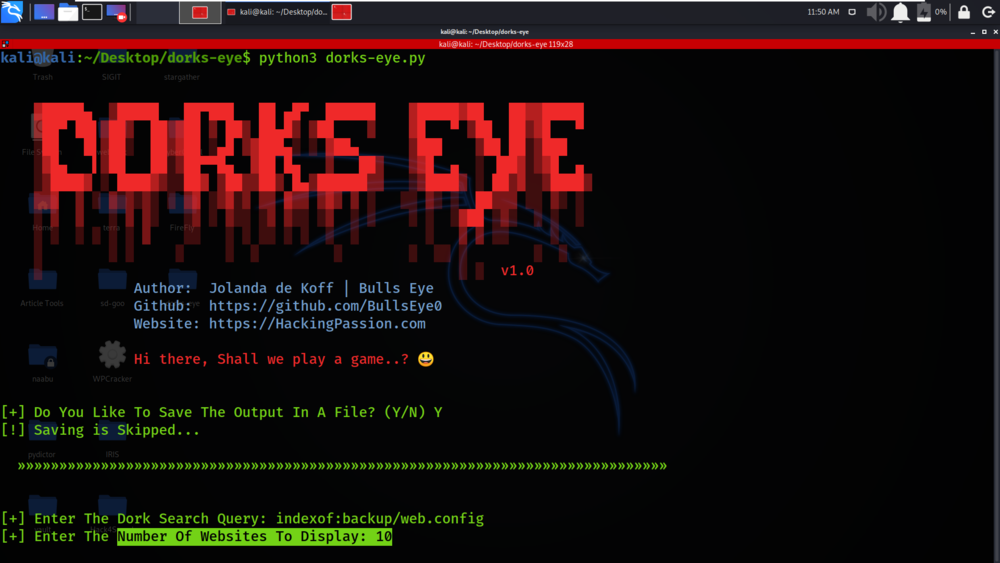
Query used -> indexof:backup/web.config
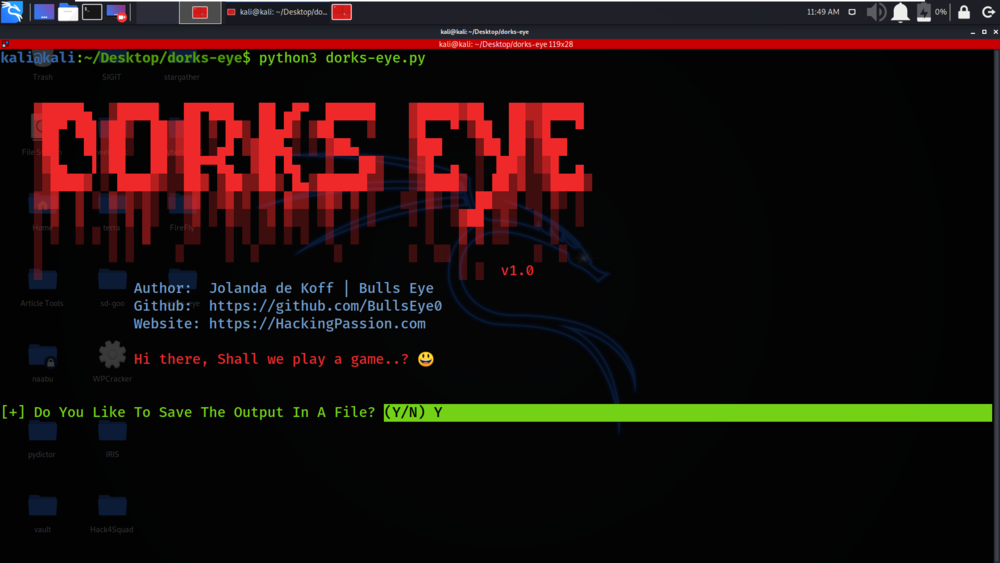
We have specified the dork query through which we will get vulnerable site links.
We will be displaying the 10 vulnerable sites on the terminal. You can display more than 10 websites.
We have got the links of vulnerable sites which match the dork query.
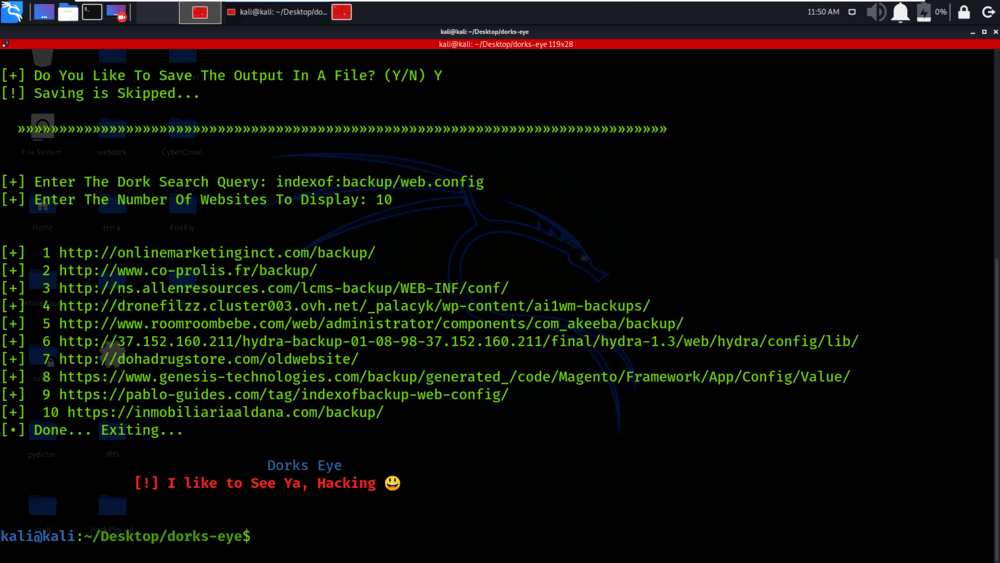
We have visited the link and we have got the conf directory contents which include various .xml files.
Share your thoughts in the comments
Please Login to comment...