Kali Linux – Vulnerability Analysis Tools
Last Updated :
20 Nov, 2021
Vulnerability Analysis is one of the most important phases of Hacking. It is done after Information Gathering and is one of the crucial steps to be done while designing an application. The cyber-world is filled with a lot of vulnerabilities which are the loopholes in a program through which hacker executes an attack. These vulnerabilities act as an injection point or a point that could be used by an attacker as a launchpad to execute the attack.
Kali Linux comes packed with 300+ tools out of which many are used for vulnerability analysis. Though there are many tools in Kali Linux for vulnerability analysis here is the list of most used tools.
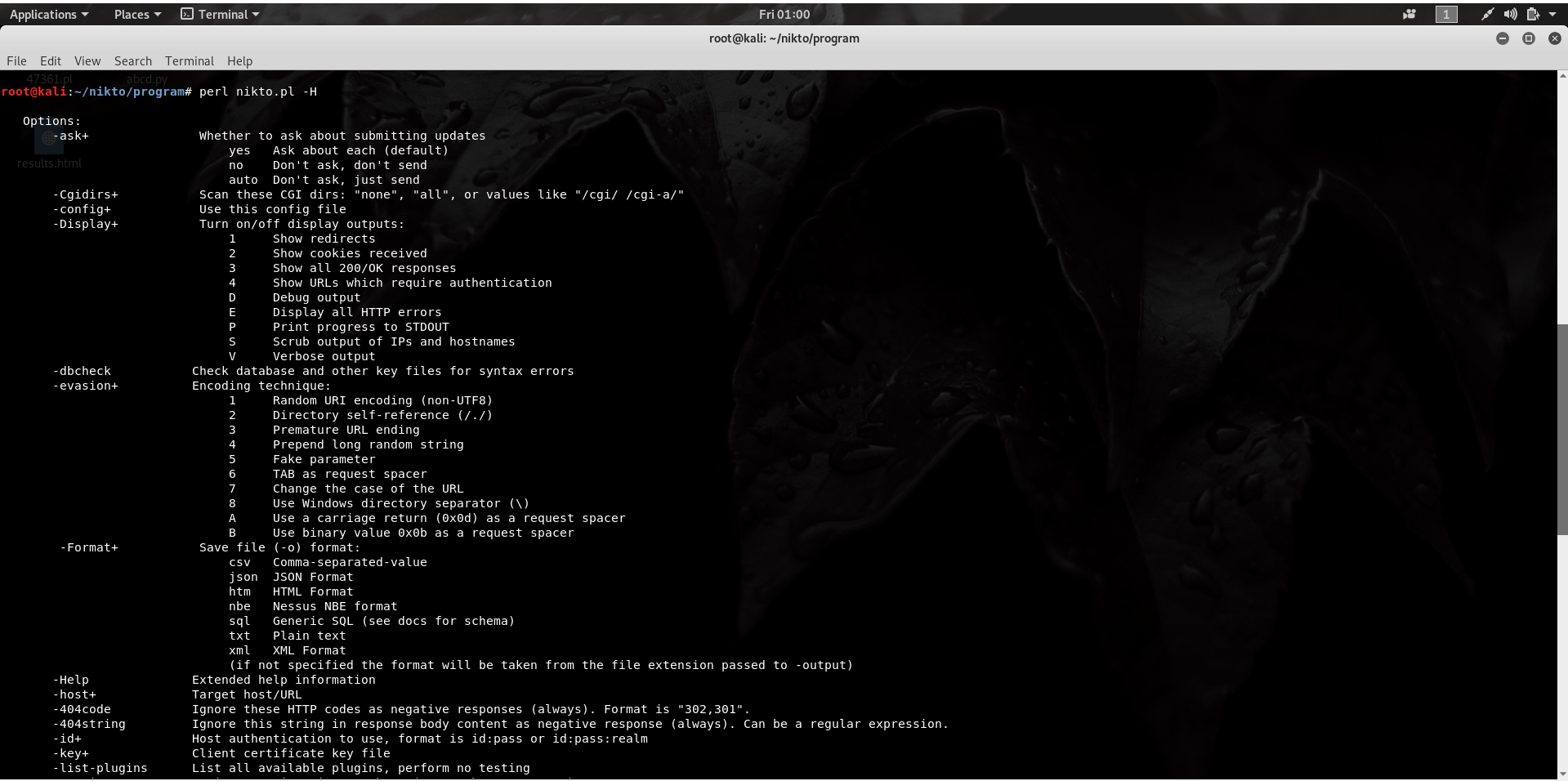
Nikto is an Open Source software written in Perl language that is used to scan a web-server for vulnerability that can be exploited and can compromise the server. It can also check for outdated version details of 1200 servers and can detect problems with specific version details of over 200 servers. It comes packed with many features, a few of them are listed below.
- Full support for SSL
- Looks for subdomains
- Supports full HTTP Proxy
- Outdated component report
- Username Guessing
To use Nikto, download nikto, and enter the following command:
perl nikto.pl -H
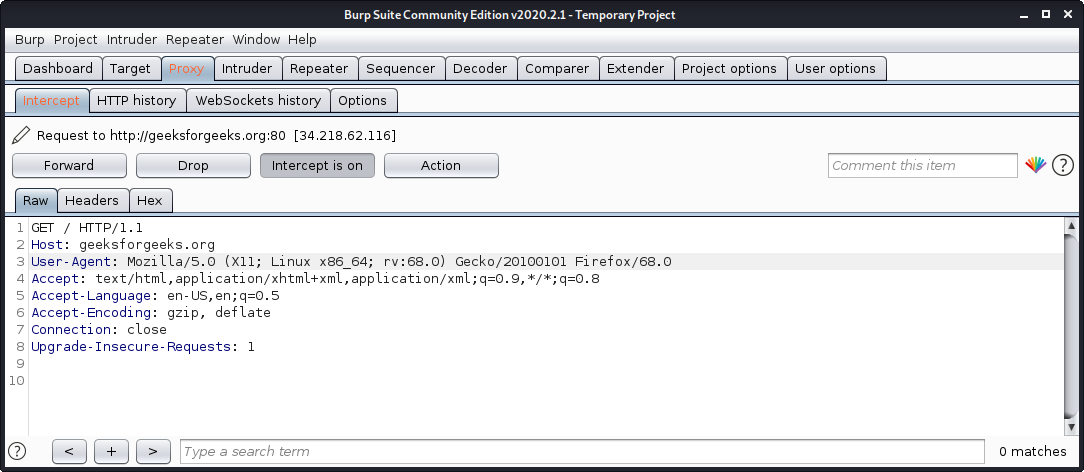
2. Burp Suite
Burp Suite is one of the most popular web application security testing software. It is used as a proxy, so all the requests from the browser with the proxy pass through it. And as the request passes through the burp suite, it allows us to make changes to those requests as per our need which is good for testing vulnerabilities like XSS or SQLi or even any vulnerability related to the web. Kali Linux comes with burp suite community edition which is free but there is a paid edition of this tool known as burp suite professional which has a lot many functions as compared to burp suite community edition.
To use burp suite:
- Read this to learn how to setup burp suite.
- Open terminal and type “burpsuite” there.
- Go to the Proxy tab and turn the interceptor switch to on.
- Now visit any URL and it could be seen that the request is captured.
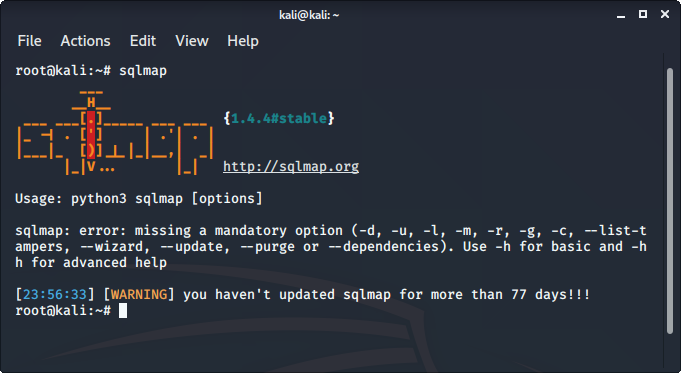
SQLMap is an open-source tool that is used to automate the process of manual SQL injection over a parameter on a website. It detects and exploits the SQL injection parameters itself all we have to do is to provide it with an appropriate request or URL. It supports 34 databases including MySQL, Oracle, PostgreSQL, etc.
To use sqlmap tool:
- sqlmap comes pre-installed in Kali Linux
- Just type sqlmap in the terminal to use the tool.
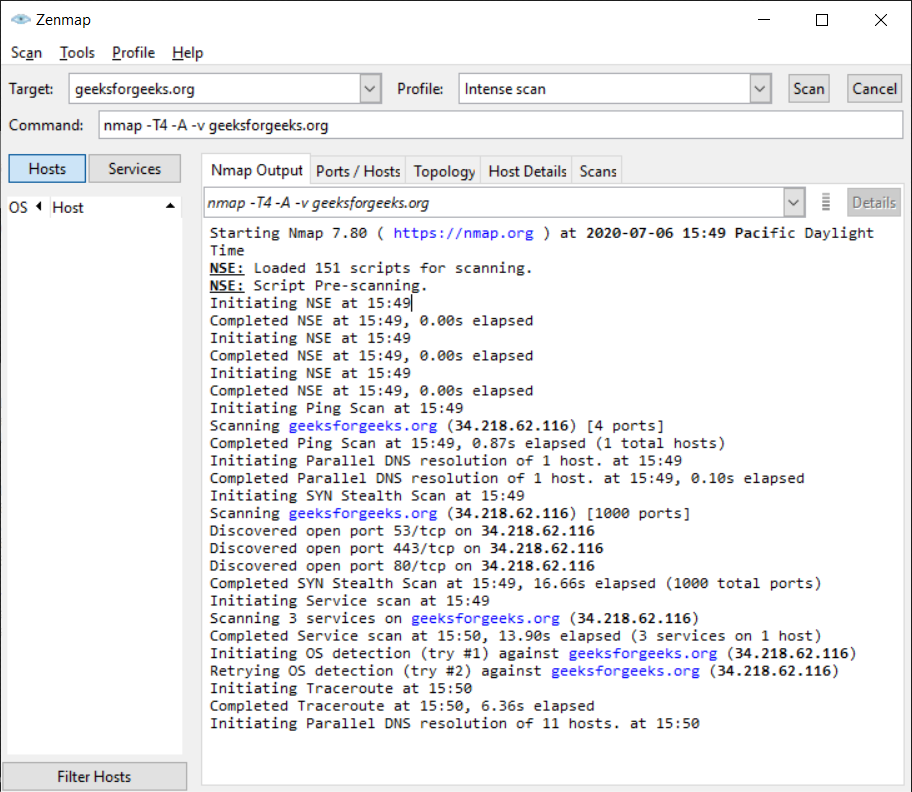
4. ZenMAP
It is another useful tool for the scanning phase of Ethical Hacking in Kali Linux. It uses the Graphical User Interface. It is a great tool for network discovery and security auditing. It does the same functions as that of the Nmap tool or in other words, it is the graphical Interface version of the Nmap tool. It uses command line Interface. It is a free utility tool for network discovery and security auditing. Tasks such as network inventory, managing service upgrade schedules, and monitoring host or service uptime are considered really useful by systems and network administrators.
To use Zenmap, enter the target URL in the target field to scan the target.
Nmap is an open-source network scanner that is used to recon/scan networks. It is used to discover hosts, ports, and services along with their versions over a network. It sends packets to the host and then analyzes the responses in order to produce the desired results. It could even be used for host discovery, operating system detection, or scanning for open ports. It is one of the most popular reconnaissance tools.
To use Nmap:
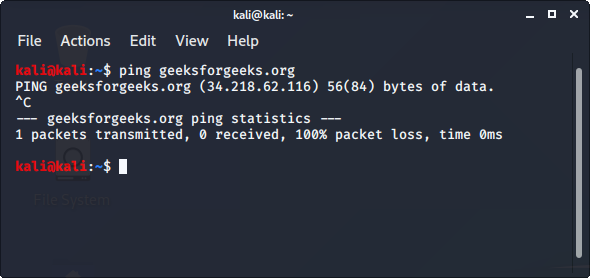
- Ping the host with ping command to get the IP address
ping hostname
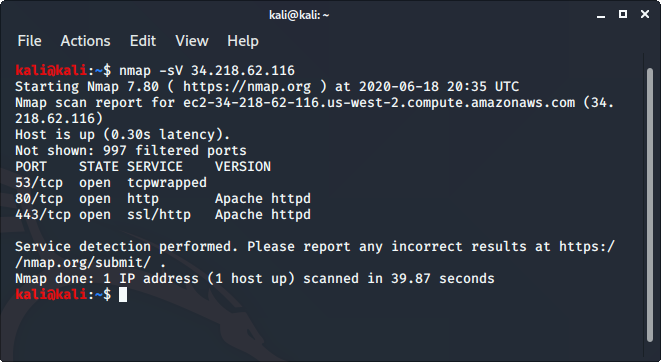
- Open the terminal and enter the following command there:
nmap -sV ipaddress
- Replace the IP address with the IP address of the host you want to scan.
It will display all the captured details of the host.
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...