X.25 Structure
Last Updated :
26 Dec, 2022
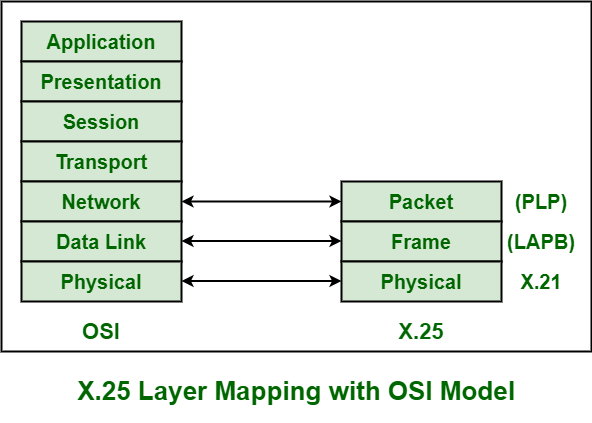
X.25 is generally a protocol that was developed by Telecommunication Standardization Sector (ITU-T) of International Telecommunication Union. It usually allows various logical channels to make use of same physical line. It basically defines a series of documents particularly issued by ITU. These documents are also known as X.25 Recommendations. X.25 also supports various conversations by multiplexing packets and also with the help of virtual communication channels. X.25 basically encompasses or suits to the lower three layers of the Open System Interconnection (OSI) reference model for networking. These three protocol layers are :
- Physical Layer
- Frame Layer
- Packet Layer
These are explained as following below.
- Physical Layer : This layer is basically concerned with electrical or signaling. The physical layer interface of X.25 also known as X.21 bis was basically derived from RS-232 interface for serial transmission. This layer provides various communication lines that transmit or transfer some electrical signals. X.21 implementer is usually required for linking.
- Data Link Layer : Data link layer is also known as Frame Layer. This layer is an implementation or development of ISO High-Level Data Link Layer (HDLC) standard which is known as LAPB (Link Access Procedure Balanced). It also provides a communication link and transmission that is error-free among any two physically connected nodes or X.25 nodes. LAPB also allows DTE (Data Terminal Equipment) or DCE (Data Circuit-Terminating Equipment) simply to start or end a communication session or start data transmission. This layer is one of the most important and essential parts of X.25 Protocol. This layer also provides a mechanism for checking in each hop during the transmission. This service also ensures a bit-oriented, error-free, and also sequenced and ordered delivery of data frames or packets. There are many protocols that can be used in frame-level as given below :
- Link Access Procedure Balanced (LAPB) – It is specified by ITU-T Recommendation X usually derived from HDLC. It is the most commonly used protocol that allows establishing a logical connection.
- Link Access Protocol (LAP) – This protocol is very rarely used. This is usually used for framing and transferring data packets across point-to-point links.
- Link Access Procedure D-channel (LAPD) – It is used to convey or transfer data over D-channel. It also enables and allows transmission of data among DTEs through D channel especially among a DTE and an ISDN node.
- Logical Link Control (LLC) – It is used to manage and ensure the integrity of transmissions of data. It also allows transmission of X.25 data packets or frames through a LAN (Local Area Network) channel.
- Packet Layer : Packet layer is also known as Network Layer protocol of X.25. This layer generally governs the end-to-end communications among various DTE devices. It also defines how to address and deliver X.25 packets among end nodes and switches on a network with the help of PVCs (Permanent Virtual Circuits) or SVCs (Switched Virtual Circuits). This layer also governs and manages set-up and teardown and also flow control among DTE devices as well as various routing functions along with multiplexing multiple logical or virtual connections. This layer also defines and explains the format of data packets and also the procedures for control and transmission of data frames. This layer is also responsible for establishing a connection, transmitting data frames or packets, ending or terminating a connection, error and flow control, transmitting data packets over external virtual circuits.

Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...