Wireless Local Loop
Last Updated :
22 Aug, 2023
Local loop is a circuit line from a subscriber’s phone to the local central office (LCO). But the implementation of local loop of wires is risky for the operators, especially in rural and remote areas due to less number of users and increased cost of installation. Hence, the solution for it is the usage of wireless local loop (WLL) which uses wireless links rather than copper wires to connect subscribers to the local central office.
WLL Architecture:
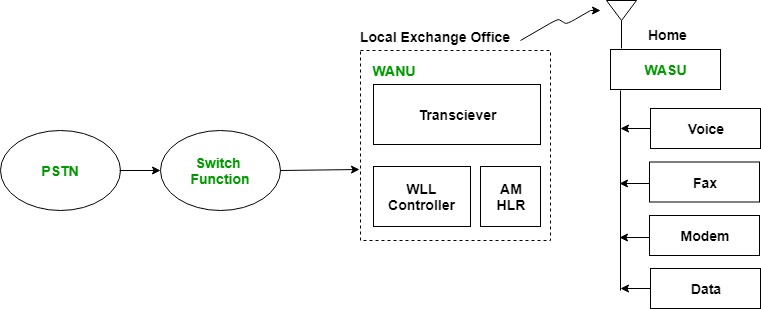
The Wireless Local Loop (WLL) architecture replaces traditional copper wires with wireless links, connecting subscribers to the local central office. It consists of several components, including the PSTN (Public Switched Telephone Network), Switch Function, WANU (Wireless Access Network Unit), and WASU (Wireless Access Subscriber Unit).
The PSTN serves as a circuit-switched network, while the Switch Function manages connections between WANUs. The WANU takes care of authentication, operation, routing, and data transmission, whereas the WASU is installed at the subscriber’s location. With its cost-effectiveness, enhanced security through digital encryption, scalability options, and various features like internet access, voice services, data transfer capabilities, and fax services – WLL proves to be a dependable solution for telecommunication requirements specifically in remote or rural areas.
WLL components:
- PSTN: It is Public Switched Telephone Network which is a circuit switched network. It is a collection of world’s interconnected circuit switched telephone networks.
- Switch Function: Switch Function switches the PSTN among various WANUs.
- WANU: It is short for Wireless Access Network Unit. It is present at the local exchange office. All local WASUs are connected to it. Its functions includes: Authentication, Operation & maintenance, Routing, Transceiving voice and data. It consists of following sub-components:
- Transceiver: It transmits/receives data.
- WLL Controller: It controls the wireless local loop component with WASU.
- AM: It is short for Access Manager. It is responsible for authentication.
- HLR: It is short for Home Location Register. It stores the details of all local WASUs.
- WASU: It is short for Wireless Access Subscriber Units. It is present at the house of the subscriber. It connects the subscriber to WANU and the power supply for it is provided locally.
- Advantages of WLL:
-
- It eliminates the first mile or last mile construction of the network connection.
- Low cost due to no use of conventional copper wires.
- Much more secure due to digital encryption techniques used in wireless communication.
- Highly scalable as it doesn’t require the installation of more wires for scaling it.
- Features of WLL:
-
- Internet connection via modem
- Data service
- Voice service
- Fax service
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...