Various kind of Framing in Data link layer
Last Updated :
26 Aug, 2020
Framing is function of Data Link Layer that is used to separate message from source or sender to destination or receiver or simply from all other messages to all other destinations just by adding sender address and destination address. The destination or receiver address is simply used to represent where message or packet is to go and sender or source address is simply used to help recipient to acknowledge receipt.
Frames are generally data unit of data link layer that is transmitted or transferred among various network points. It includes complete and full addressing, protocols that are essential, and information under control. Physical layers only just accept and transfer stream of bits without any regard to meaning or structure. Therefore it is up to data link layer to simply develop and recognize frame boundaries.
This can be achieved by attaching special types of bit patterns to start and end of the frame. If all of these bit patterns might accidentally occur in data, special care is needed to be taken to simply make sure that these bit patterns are not interpreted incorrectly or wrong as frame delimiters.
Framing is simply point-to-point connection among two computers or devices that consists or includes wire in which data is transferred as stream of bits. However, all of these bits should be framed into discernible blocks of information.
Methods of Framing :
There are basically four methods of framing as given below –
1. Character Count
2. Flag Byte with Character Stuffing
3. Starting and Ending Flags, with Bit Stuffing
4. Encoding Violations
These are explained as following below.
- Character Count :
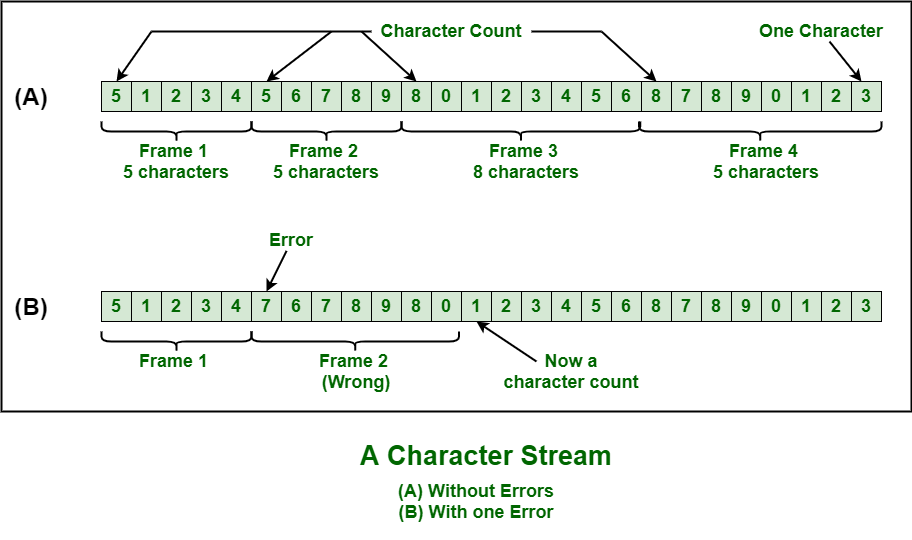
This method is rarely used and is generally required to count total number of characters that are present in frame. This is be done by using field in header. Character count method ensures data link layer at the receiver or destination about total number of characters that follow, and about where the frame ends.
There is disadvantage also of using this method i.e., if anyhow character count is disturbed or distorted by an error occurring during transmission, then destination or receiver might lose synchronization. The destination or receiver might also be not able to locate or identify beginning of next frame.
- Character Stuffing :
Character stuffing is also known as byte stuffing or character-oriented framing and is same as that of bit stuffing but byte stuffing actually operates on bytes whereas bit stuffing operates on bits. In byte stuffing, special byte that is basically known as ESC (Escape Character) that has predefined pattern is generally added to data section of the data stream or frame when there is message or character that has same pattern as that of flag byte.
But receiver removes this ESC and keeps data part that causes some problems or issues. In simple words, we can say that character stuffing is addition of 1 additional byte if there is presence of ESC or flag in text.

- Bit Stuffing :
Bit stuffing is also known as bit-oriented framing or bit-oriented approach. In bit stuffing, extra bits are being added by network protocol designers to data streams. It is generally insertion or addition of extra bits into transmission unit or message to be transmitted as simple way to provide and give signaling information and data to receiver and to avoid or ignore appearance of unintended or unnecessary control sequences.
It is type of protocol management simply performed to break up bit pattern that results in transmission to go out of synchronization. Bit stuffing is very essential part of transmission process in network and communication protocol. It is also required in USB.
- Physical Layer Coding Violations :
Encoding violation is method that is used only for network in which encoding on physical medium includes some sort of redundancy i.e., use of more than one graphical or visual structure to simply encode or represent one variable of data.
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...