System Security
Last Updated :
16 Jun, 2022
Prerequisite – Basic Network Attacks, Types of Viruses
The security of a computer system is a crucial task. It is a process of ensuring the confidentiality and integrity of the OS. Security is one of most important as well as the major task in order to keep all the threats or other malicious tasks or attacks or program away from the computer’s software system.
A system is said to be secure if its resources are used and accessed as intended under all the circumstances, but no system can guarantee absolute security from several of various malicious threats and unauthorized access.
The security of a system can be threatened via two violations:
- Threat: A program that has the potential to cause serious damage to the system.
- Attack: An attempt to break security and make unauthorized use of an asset.
Security violations affecting the system can be categorized as malicious and accidental threats. Malicious threats, as the name suggests are a kind of harmful computer code or web script designed to create system vulnerabilities leading to back doors and security breaches. Accidental Threats, on the other hand, are comparatively easier to be protected against. Example: Denial of Service DDoS attack.
Security can be compromised via any of the breaches mentioned:
- Breach of confidentiality: This type of violation involves the unauthorized reading of data.
- Breach of integrity: This violation involves unauthorized modification of data.
- Breach of availability: It involves unauthorized destruction of data.
- Theft of service: It involves the unauthorized use of resources.
- Denial of service: It involves preventing legitimate use of the system. As mentioned before, such attacks can be accidental in nature.
Security System Goal:
Henceforth, based on the above breaches, the following security goals are aimed:
- Integrity:
The objects in the system mustn’t be accessed by any unauthorized user & any user not having sufficient rights should not be allowed to modify the important system files and resources.
- Secrecy:
The objects of the system must be accessible only to a limited number of authorized users. Not everyone should be able to view the system files.
- Availability:
All the resources of the system must be accessible to all the authorized users i.e. only one user/process should not have the right to hog all the system resources. If such kind of situation occurs, denial of service could happen. In this kind of situation, malware might hog the resources for itself & thus preventing the legitimate processes from accessing the system resources.
Threats can be classified into the following two categories:
- Program Threats:
A program was written by a cracker to hijack the security or to change the behavior of a normal process. In other words, if a user program is altered and further made to perform some malicious unwanted tasks, then it is known as Program Threats.
- System Threats:
These threats involve the abuse of system services. They strive to create a situation in which operating-system resources and user files are misused. They are also used as a medium to launch program threats.
Types of Program Threats:
- Virus:
An infamous threat, known most widely. It is a self-replicating and malicious thread that attaches itself to a system file and then rapidly replicates itself, modifying and destroying essential files leading to a system breakdown.
Further, Types of computer viruses can be described briefly as follows:
– file/parasitic – appends itself to a file
– boot/memory – infects the boot sector
– macro – written in a high-level language like VB and affects MS Office files
– source code – searches and modifies source codes
– polymorphic – changes in copying each time
– encrypted – encrypted virus + decrypting code
– stealth – avoids detection by modifying parts of the system that can be used to detect it, like the read system
call
– tunneling – installs itself in the interrupt service routines and device drivers
– multipartite – infects multiple parts of the system
- Trojan Horse:
A code segment that misuses its environment is called a Trojan Horse. They seem to be attractive and harmless cover programs but are really harmful hidden programs that can be used as the virus carrier. In one of the versions of Trojan, the User is fooled to enter confidential login details on an application. Those details are stolen by a login emulator and can be further used as a way of information breaches. One of the major as well as a serious threat or consequences of the Trojan horse is that it will actually perform proper damage once installed or run on the computer’s system but at first, a glance will appear to be useful software and later turns out to be maliciously unwanted one.
Another variance is Spyware, Spyware accompanies a program that the user has chosen to install and download ads to display on the user’s system, thereby creating pop-up browser windows and when certain sites are visited by the user, it captures essential information and sends it over to the remote server. Such attacks are also known as Convert Channels.
- Trap Door:
The designer of a program or system might leave a hole in the software that only he is capable of using, the Trap Door works on similar principles. Trap Doors are quite difficult to detect as to analyze them, one needs to go through the source code of all the components of the system. In other words, if we may have to define a trap door then it would be like, a trap door is actually a kind of a secret entry point into a running or static program that actually allows anyone to gain access to any system without going through the usual security access procedures.
- Logic Bomb:
A program that initiates a security attack only under a specific situation. To be very precise, a logic bomb is actually the most malicious program which is inserted intentionally into the computer system and that is triggered or functions when specific conditions have been met for it to work.
- Worm: A computer worm is a type of malware that replicates itself and infects other computers while remaining active on affected systems. A computer worm replicates itself in order to infect machines that aren’t already infested. It frequently accomplishes this by taking advantage of components of an operating system that are automatic and unnoticed by the user. Worms are frequently overlooked until their uncontrolled replication depletes system resources, slowing or stopping other activities.
Types of System Threats –
Aside from the program threats, various system threats are also endangering the security of our system:
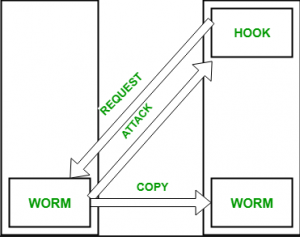
1. Worm:
An infection program that spreads through networks. Unlike a virus, they target mainly LANs. A computer affected by a worm attacks the target system and writes a small program “hook” on it. This hook is further used to copy the worm to the target computer. This process repeats recursively, and soon enough all the systems of the LAN are affected. It uses the spawn mechanism to duplicate itself. The worm spawns copies of itself, using up a majority of system resources and also locking out all other processes.
The basic functionality of the worm can be represented as:
2. Port Scanning:
It is a means by which the cracker identifies the vulnerabilities of the system to attack. It is an automated process that involves creating a TCP/IP connection to a specific port. To protect the identity of the attacker, port scanning attacks are launched from Zombie Systems, that is systems that were previously independent systems that are also serving their owners while being used for such notorious purposes.
3. Denial of Service:
Such attacks aren’t aimed for the purpose of collecting information or destroying system files. Rather, they are used for disrupting the legitimate use of a system or facility.
These attacks are generally network-based. They fall into two categories:
– Attacks in this first category use so many system resources that no useful work can be performed.
For example, downloading a file from a website that proceeds to use all available CPU time.
– Attacks in the second category involve disrupting the network of the facility. These attacks are a result of the abuse of some fundamental TCP/IP principles.
the fundamental functionality of TCP/IP.
Security Measures Taken –
To protect the system, Security measures can be taken at the following levels:
- Physical:
The sites containing computer systems must be physically secured against armed and malicious intruders. The workstations must be carefully protected.
- Human:
Only appropriate users must have the authorization to access the system. Phishing(collecting confidential information) and Dumpster Diving(collecting basic information so as to gain unauthorized access) must be avoided.
- Operating system:
The system must protect itself from accidental or purposeful security breaches.
- Networking System:
Almost all of the information is shared between different systems via a network. Intercepting these data could be just as harmful as breaking into a computer. Henceforth, Network should be properly secured against such attacks.
Usually, Anti Malware programs are used to periodically detect and remove such viruses and threats. Additionally, to protect the system from Network Threats, a Firewall is also be used.
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...