Secure Code Review Assessment
Last Updated :
09 Oct, 2020
What is Code Review?
Developing robust and enterprise level applications is a time consuming task and making them completely secure is an impossible task. In reality, security is not about creating an impenetrable fortress but it is about managing and mitigating risk. Code review aims to identify security flaws in application related to its features and design, along with exact root cause. With increasing complexity of applications and introduction of new technologies, traditional way of testing may fail to detect all security flaws present in applications.
It is important to understand code of application, external components, and configurations to have a better chance of finding security vulnerabilities. Deep dive into application code also helps in determining exact mitigation techniques that can be used to avert security bugs. Code review is a way to ensure that application has been developed as “self-defending” in its environment and allows an organization to ensure that application developers are following secure development techniques.
It is best to weave code review assessment into SDLC processes so that organizations do not see security as a hindrance but as assistance and enables them to deliver a secure product. Spreading secure coding SMEs throughout an organization allows secure code review tasks to scale and reach to more development teams. As process grows more developers gain awareness of secure coding mechanism and frequency of secure coding vulnerabilities would drop.
How Code Review is different from Secure Code review?
Code Review is perceived as a software quality assurance activity in which analyst checks code for flaws related to functional or business requirement. It is usually done via peer review or quality assurance team.
Secure Code Review is an enhancement to standard code review practices and methodologies where structure of review process places security considerations such as company security standards at forefront of decision-making. Assessment is carried by cyber security team.
A security review of application should uncover common security vulnerabilities as well as issues specific to business logic of application. In order to effectively review a code it is important that reviewers understand business purpose of application and critical business impacts. Reviewers should understand attack surface; identify different threat agents and their motivations, and how they could potentially attack application.
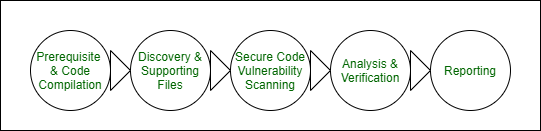
How to conduct Secure code Review ?
Secure code review is done via two ways :
- Manual Code Review –
Reviewer needs to go through complete code and understand workflow to identify vulnerabilities. Defining a generic checklist is a good barometer for level of security developers have attempted or thought of. Usually IDE(s) are used for manual review as it makes it easier to read code.
- Automated code review –
Reviewer needs to review report generated by SAST tool and identify reported vulnerabilities as false positive or true positives. Some popular tools are : Fortify, Checkmarx, IBM AppScan source, Bandit etc.
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...