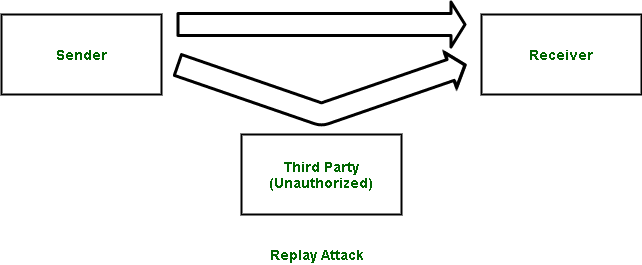
Replay Attack
Last Updated :
23 Jun, 2020
Data has become very important to us in recent times. Safety and Security of data is of paramount importance. There are several confidential and sensitive information, which we cannot risk getting into wrong hands. However, sometimes an unauthorized person gets access to our information. Any action by an unauthorized person or hacker which poses a threat on the integrity, confidentiality and authentication of data is called a security attack.
What is Replay Attack ?
Replay Attack is a type of security attack to the data sent over a network.
In this attack, the hacker or any person with unauthorized access, captures the traffic and sends communication to its original destination, acting as the original sender. The receiver feels that it is an authenticated message but it is actually the message sent by the attacker. The main feature of the Replay Attack is that the client would receive the message twice, hence the name, Replay Attack.
Note –
Arrows in the above image denote flow of communication.
Prevention from Replay Attack :
- Timestamp method –
Prevention from such attackers is possible, if timestamp is used along with the data. Supposedly, the timestamp on a data is more than a certain limit, it can be discarded, and sender can be asked to send the data again.
- Session key method –
Another way of prevention, is by using session key. This key can be used only once (by sender and receiver) per transaction, and cannot be reused.
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...