Remote File System (RFS) in File Management
Last Updated :
25 May, 2020
Files can be shared across the network via variety of methods –
- Using FTP i.e., file transfer protocol is used to transfer file from one computer to other.
- Using distributed file system (DFS) in which remote directories are visible from local machine.
- Using Remote File System (RFS) in which the arrival of networks has allowed communication between remote computer. These networks allows various hardware and software resources to be shared throughout the world.
Remote file sharing (RFS) is a type of distributed file system technology. It was developed in 1980 by AT&T. Later, it was delivered with UNIX System version V (five) release 3 (SVR3). It enables file and/or data access to multiple remote users over the Internet or a network connection. It is also known as a general process of providing remote user access to locally stored files and/or data.
It was relied on the STREAMS Transport Provider Interface feature of the operating system.
To implement remote file system we use client-server model. It was one of the basic application of Remote File System.
Client-Server Model in RFS :
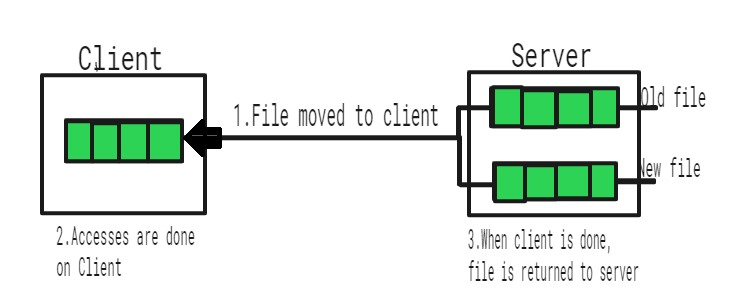
RFS allows a computer to support one or more file systems from one or more remote machines. In this case, the machine containing the files is server and the machine wanting access to the files is the client. The server specifies which file can be accessed by a particular client(s). Files are usually specified on a partition level.
A server can serve multiple clients, and a client can access multiple servers, depending on the implementation details of a given client-server facility. Once it is mounted, file operation requests are sent on the behalf of the user to the server, via network.
For example, a user sends a file open request to the server along with its ID. The server then check file access to determine if the user has rights to access the file requested mode. This request is either allowed or denied. If it is allowed, a file is returned to the client application, and the application then may perform read, write and other operations on file.
After the required operation is performed, the client closes the files.
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...