Recover password of password protected zip file
Last Updated :
31 Oct, 2022
In this article, we will get to know about how to get the password of a zip file. I’m using Linux I went with a quick search and came across fcrackzip. This is a free program that allows for both dictionary and brute force cracking of zip file passwords. It is not difficult to use and offers a wide range of options.
Let’s make a zip file then we will copy-paste it into Linux after that we will try to break this password by fcrackzip. I created a zip file. This zip file’s password is 12345678.
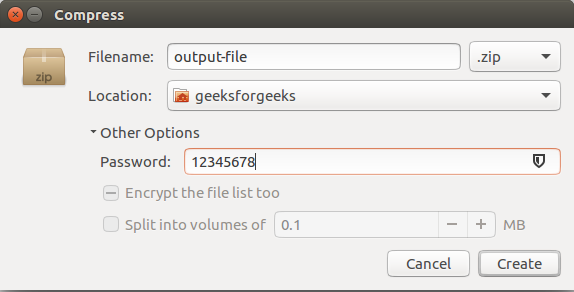
Creating password protected secret.zip
In Terminal type fcrackzip –help this command will open help options for fcrackzip
USAGE: fcrackzip
[-b|--brute-force] use brute force algorithm
[-D|--dictionary] use a dictionary
[-B|--benchmark] execute a small benchmark
[-c|--charset characterset] use characters from charset
[-h|--help] show this message
[--version] show the version of this program
[-V|--validate] sanity-check the algorithm
[-v|--verbose] be more verbose
[-p|--init-password string] use string as initial password/file
[-l|--length min-max] check password with length min to max
[-u|--use-unzip] use unzip to weed out wrong passwords
[-m|--method num] use method number "num" (see below
[-2|--modulo r/m] only calculate 1/m of the password
file... the zipfiles to crack
There are 2 methods to get the password of the zip file
1. Brute force attack: If you wanted to use a brute force attack from 4-8 characters on “secret.zip” you would use the following command:
$fcrackzip -v -m -l 4-8 -u secret.zip
To break the command down:
- v is for verbose and gives you better output
- m specifies the mode to use, in this case, zip6
- l specifies the minimum password length to maximum password length
- u tells the program to test the password with unzip before declaring it correct
2. Dictionary-based Attack: Using a dictionary-based attack is as easy as brute force attack
Syntax:
$ fcrackzip -v -D -u -p /usr/share/dict/words secret.zip
Here: /usr/share/dict/words is the wordlists and secret.zip is the zipped file that is encrypted.
Example:
fcrackzip -v -D -u -p /usr/share/wordlists/rockyou.txt 16162020_backup.zip
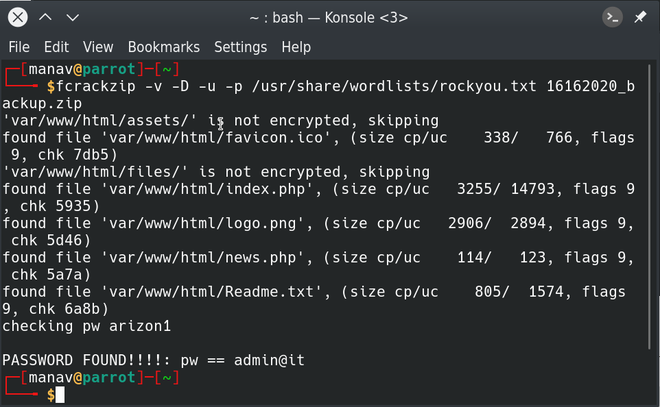
Here the only difference is the -D to specify a dictionary-based attack and -p which is used to specify the password file. This file should contain one word per line and on Linux systems, there’s a nice dictionary included in /usr/share/dict/words or you can use any other password dictionaries.
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...