Rake Receiver
Last Updated :
27 Feb, 2023
The dictionary meaning of rake is to gather or collect together something and actually is a garden tool to collect leaves. But in the terms of computer network, it is for the purpose of collecting signals from multiple paths arriving at the receiver end and used specially in CDMA cellular systems. A Rake Receiver is a radio receiver which is designed for the purpose to counter the effects of multipath fading. Due to reflections from multiple obstacles in the environment, the radio channel can consist of multiple copies of the transmitted signal having different amplitude, phases or delays. A rake receiver can resolve this issue and combine them. For this purpose, several sub-receivers are used which are known as “fingers”. The idea of a basic rake receiver was first proposed by Price and Green.
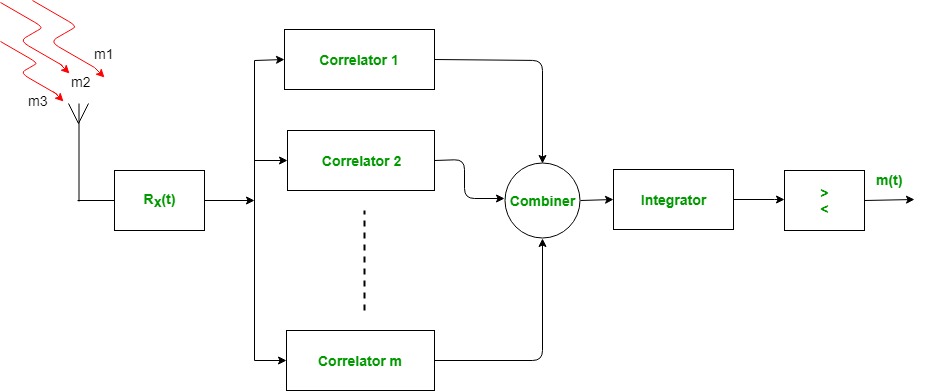
When the transmitter transmits the signal then it travels through the environment which consists of various obstacles and the transmitted signal is reflected by them and is received by the rake receiver from multiple paths. Rake receiver then feeds them to different fingers (correlators). The delays in each received signal are compensated and are feeded to the Combiner, Integrator and Comparator which combines them suitably with different appropriate time delays.
Working of Rake Receiver:
- The received signal from multiple paths arrives at the antenna with different delays and phases.
- The signal is first passed through a bank of matched filters, each of which corresponds to a specific path.
- The output of each matched filter is sampled at the symbol rate and the resulting samples are combined.
- The combining process is done using a technique called maximum ratio combining (MRC) which gives more weight to the signals that have higher signal-to-noise ratio (SNR).
- The combined signal is then demodulated to obtain the transmitted symbols.
- The rake receiver also performs channel estimation by estimating the complex gains of each path using a technique called pilot symbols.
- The channel estimates are used to adjust the weights in the combining process to ensure optimal performance.
- The rake receiver also uses a technique called diversity combining to reduce the effect of fading by combining the signals from multiple antennas.
- The combined signal from each antenna is then passed through the matched filter and combined using maximum ratio combining.
- The rake receiver is able to recover the transmitted signal even in the presence of severe multipath fading and interference.
Some key applications of Rake receiver are:
- CDMA Systems: Rake receivers are extensively used in CDMA systems, where they are used to combat the effects of multipath fading.
- Wireless Networks: Rake receivers are also used in wireless networks to improve the performance of the system, especially in environments where the signal is weak.
- Satellite Communications: In satellite communication systems, Rake receivers are used to detect and extract weak signals that have traveled long distances.
- Mobile Communications: Rake receivers are used in mobile communication systems to improve the quality of the received signal by minimizing the effects of multipath fading.
- High-Speed Data Transmission: Rake receivers are used in high-speed data transmission systems to reduce errors caused by the transmission of signals over long distances.
Some key advantages of rake receiver are:
- Multipath mitigation: The rake receiver mitigates the effect of multipath propagation by combining multiple replicas of the same signal, which have been transmitted over different paths.
- Diversity gain: By combining multiple replicas of the same signal, the rake receiver provides diversity gain, which helps to improve the signal-to-noise ratio (SNR) and reduce the bit error rate (BER) of the received signal.
- Interference rejection: The rake receiver can also be used to reject interference from other signals that are transmitted over the same frequency band.
- Simple implementation: The rake receiver is a simple and effective technique that can be implemented using digital signal processing (DSP) algorithms.
- Compatibility: The rake receiver is compatible with different modulation schemes and can be used in various wireless communication systems, such as code division multiple access (CDMA), time division multiple access (TDMA), and frequency division multiple access (FDMA).
- Improvement in system capacity: The use of a rake receiver in a wireless communication system can increase the system capacity by allowing the use of more frequency bands or by increasing the number of users that can be supported.
Some key disadvantages of rake receiver are:
- Complex implementation: The Rake receiver is a complex receiver with a large number of matched filters, which makes it difficult to implement.
- High power consumption: The Rake receiver requires a lot of power to operate, which can be a problem in battery-powered devices.
- Limited performance in deep fades: The Rake receiver is not very effective in deep fades, where the signal is severely attenuated. In such cases, other techniques such as diversity combining may be more effective.
- Sensitivity to multipath delay spread: The Rake receiver is designed to work in the presence of multipath, but it is sensitive to the delay spread of the channel. In channels with large delay spreads, the performance of the Rake receiver may degrade.
- Limited applicability to narrowband systems: The Rake receiver is designed to work with wideband systems that have significant multipath propagation. In narrowband systems with little or no multipath, the Rake receiver may not be necessary or effective.
The Rake receiver is an important solution to the problem of multipath fading in wireless communication. It is designed to improve the signal quality and reduce the effects of fading by using multiple copies of the transmitted signal that arrive at the receiver at different times. Although the Rake receiver is more complex, more power-consuming, and more expensive than other types of receivers, it provides better coverage and improved data rates, making it an attractive solution for high-speed wireless communication.
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...