POP Full Form
Last Updated :
29 Jan, 2024
POP stands for Point of Presence (also known as Post Office Protocol).
It is a point where many devices share a connection and can communicate with each other. We can say that it is a man-made demarcation point (a point where the public network of a company ends and the private network of the customer begins for eg. the point at which your broadband cable enters the house) between communicating entities. It basically consists of high-speed telecommunications equipment and technologies that help in bringing together people from all over the internet. Post Office Protocol is referred to as the POP protocol. SMTP is employed as a message transfer agent, as is well known. When a message is sent, SMPT is used to transfer it from the client to the server and ultimately to the server of the recipient. However, the Message Access Agent facilitates the transmission of the message from the receiving server to the host server. POP3 and IMAP are the two types of protocols that are included in the Message Access Agent.
An example of this would be the local access point that connects customers via their internet service provider (ISP) to the rest of the world. The size of an ISP can be calculated by seeing the number of POPs that the service provider has. The normal houses routers, modems, servers, switches, and other such devices that have to share data over networks all use POPs. Internet Service Providers have multiple POPs.
Characteristics of POP
- Post Office Protocol is an open protocol, defined by Internet RFCs.
- It allows access to new mail from a spread of client platform types.
- POP can handle email access only while the emails are sent by SMTP.
RFC 918 got published in 1984 which defined the Post Office Protocol (POP). The explanation of why POP came in the picture was to supply a neater way for a client computer to retrieve e-mail on an SMTP (Simple Mail Transfer Protocol) server so that it can be used locally. POP Version 2 got published in 1985.
It improvised the capabilities of POP by defining a far impressive set of commands further as replies. RFC 1939 was published in 1996 and POP3 has not been improvised since that point.
Examples:
- Carrier hotels :
These buildings are extremely secure with size averaging around 54, 000 square feet. These hotels offer hardware and software installation, updation and several other services.
- Meet-me rooms :
Meet-Me Rooms (MMRs) are small space inside carrier hotels, averaging around 5, 000 square feet. These small rooms house interconnects networking equipment owned by many telecommunication companies.
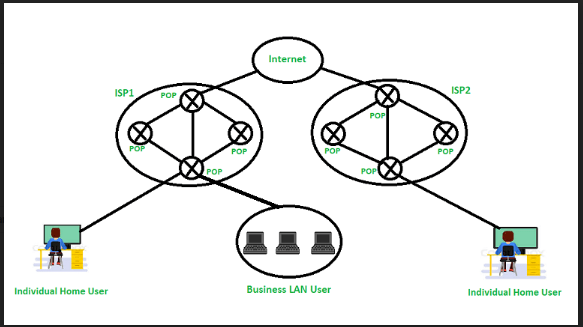
Figure – Post Office Protocol (POP)
History of POP
The Internet Engineering Task Force published the POP (post office protocol) in 1984. The backend developers wanted to simplify the layout, therefore it underwent two updates after that.
POP2, or the second version of POP, was created in 1985 and requires the SMTP protocol in order to push emails. Subsequently, the SMTP protocol was not necessary for POP3, or the third version of POP, which was published in 1988. POP 3, or Post Office Protocol, is also included in well-known email programmes like Outlook Express and Eudora.And the POP3 has been the current version ever since 1988.
Working
Until the user logs in using an email client and downloads the message to their computer, all incoming messages are kept on the POP server. The message is removed from the server once it has been downloaded by the user.
Since SMTP is known to be the method used to move email messages from one server to another, POP essentially serves as a way to retrieve emails from servers using an email client; it does not offer a way to send messages.
A POP3 connection will be made at the server-side whenever a user attempts to check all of their recent emails. In order to obtain the correct authentication, the user transmits the username and password to the server computer. Users can receive and keep all text-based emails on their local terminal (computer) after establishing a connection. They can subsequently delete any copies from the server and disconnect from the server. POP’s working is also based on below five important equipment which are:
- Base stations – A central point of reference to an access point and bandwidth management to ensure evenly distribution of the connection speed of the customer.
- Client equipment – Customers use client equipment to connect to base stations.
- Network switches – Used for proper distribution
- Routers – Provides multiple paths for the data to be shared in the network
- Firewall – Used for securing the network from threats (internal and external)
Advantages
- The latest version of Post Office Protocol (POP3) is the most widely used protocol and is being supported by most email clients. It provides a convenient and standard way for users to access mailboxes and download messages. An important advantage of this is that the mail messages get delivered to the client’s PC and they can be read with or without accessing the web.
POP3 has two modes:
- In Delete mode, the mail is deleted from the mailbox after each retrieval, in the keep mode, the mail remains in the mailbox after retrieval . The Delete mode is normally used when the user is working on a permanent computer and can save and organize the received mail after reading or replying.
- The keep mode is normally used when the user accesses mail away from the primary computer(eg, laptop). The mail is read but kept in the system for later retrieval and organization.
- The creation of the latest messages is impossible without being logged onto the web
- All messages get stored on the disc drive of your computer
- Easy to use and configure.
- There isn’t any maximum size on your mailbox, except as determined by the scale of your disc drive
Disadvantages
- Consumes large memory as all the messages are stored on the disc drive
- Opening attachments may be a fast process unless the attachment contains a virus
- Since all attachments get downloaded on your computer, there’s a danger of a virus attack if they’re not
scanned by antivirus software
- as these scans are only 60% effective
- Emails cannot be opened by other machines unless they are configured to do so.
- It is not easy to export a local mail folder to another physical machine or another mail client.
Commands Used in POP
There are basic commands used in Post Office Protocol, some of them are mention below:
- LOGIN: To establish a connection, use this command.
- STAT: This command shows all of the incoming and outgoing emails in the inbox.
- DELE: To delete a message from the system, use this command.
- RSET: This command is primarily used to set the session back to its initial configuration.
- QUIT: This command ends the user’s current session.
- LIST: This command is mostly used to retrieve a message’s summary, which is shown on the screen.
- RETR: The primary purpose of this command is to select a mailbox from which to see messages.
Frequently Asked Question on FAQs
What is POP?
Post Office Protocol is referred to as the POP protocol. SMTP is employed as a message transfer agent, as is well known. When a message is sent, SMPT is used to transfer it from the client to the server and ultimately to the server of the recipient.
Can I access my emails from multiple devices using POP?
No you can’t access emails from multiple devices if you are using POP , but this task can be done with the help of IMAP.
How does POP differ from POP3?
POP3 is the most recent version of the protocol, which is the primary distinction between it and POP. Similar to POP3, POP sends a local copy of your data to your email, and the emails disappear without the device.
Is POP still widely used, or is IMAP more popular?
POP is not as good of a choice as IMAP. Using an email client to receive mail over POP is somewhat outdated. You can only download your computer’s Inbox with this; additional folders cannot be downloaded.
Which port is suggested for secure POP connections?
The most common secure port is 995.
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...