PGP – Compression
Last Updated :
01 Nov, 2019
Everyday, more than 250 billion Emails are being exchanged over the Internet. A series of processings are involved for the transmission of an email from a sender to a recipient. The data about an email (typically about sender, receiver and domain) and of course the message ,has to be processed by the systems and servers involved in the transmission. It being done for all the 250 billion emails is a mammoth task. Sometimes it may also lead to Congestion. Hence, the email service providers use Compression as a mechanism to reduce the amount of data to be transferred.
Compression is basically converting a message of n bits to m bits (n > m) using a compression algorithm. Compression helps the email service providers to increase their productivity as the storage overhead, processing and labor spent on the maintenance of their servers is reduced.
Compression service in PGP is provided using ZIP Algorithm. The Compression is included in combined Authentication & Confidentiality of PGP as follows :
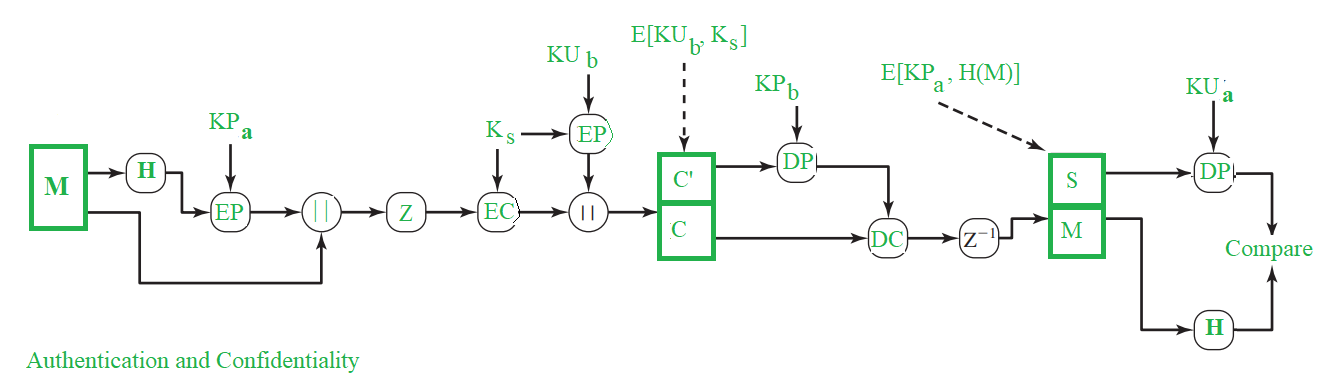
In the figure,
Z– Compression function
Z-1– Decompression function
In PGP, message is compressed only after the application of Signature. The compressed data is decompressed at the receiver’s end to obtain the original message and the signature. Then, we can extract the hash value from the signature and then we can directly determine the authenticity right away by simply calculating the message’s hash value and comparing it with the value obtained from the signature.
If compression was done before the signature was applied, which means that the hash value in the signature is not that of the original message but is of the compressed message. Thus,for checking the authenticity at the receiver’s end, we would have to either maintain the compressed message or to recompress the message. Because of the PGP algorithm we would have another problem at the time of recompression, as the algorithm may produce a variety of results for a input, based on it’s implementation and thus we may have inconsistency in the hash values obtained from them. Hence, there would be inconsistency in Authenticity verification.
Even though we get different outputs of compressed message with different implementations of algorithm, same output is produced for decompression when compressed message from any implementation is given as input. So, in order to achieve a consistent authenticity procedure we would have to implement compression with a single version. Thus for a safer use, PGP does the compression after the signature has been applied.
Normally, when both the message and signature are compressed, they are encrypted. It is to provide that extra layer of security from cryptoanalysis as there would be less redundancy than the plaintext.
Share your thoughts in the comments
Please Login to comment...