Performing Advanced SSH
Last Updated :
24 Jul, 2020
While working on any network from a remote location, we find ourselves accessing some Linux servers in the network that we want to SSH into. We can jump from devices to devices in the network. The reason for this is that it makes securing the network a lot easier when our VTY ACL consists of one IP even though we have many admins. A network access control list or ACL specifies which system processes are granted access to objects and what operations are allowed them. There’s also a record of who was logged into what with the timestamp. SSH can be much fun with the power of Linux.
Setting Up Aliases
Open up .bashrc file (use vi or pico or any other text editor). Here is an example: .bashrc file is located in the home directory.
Enter the following command to edit the file
vi ~/.bashrc
Now do the following changes in the file.
alias s='ssh'
alias sc='ssh -l anyusername'
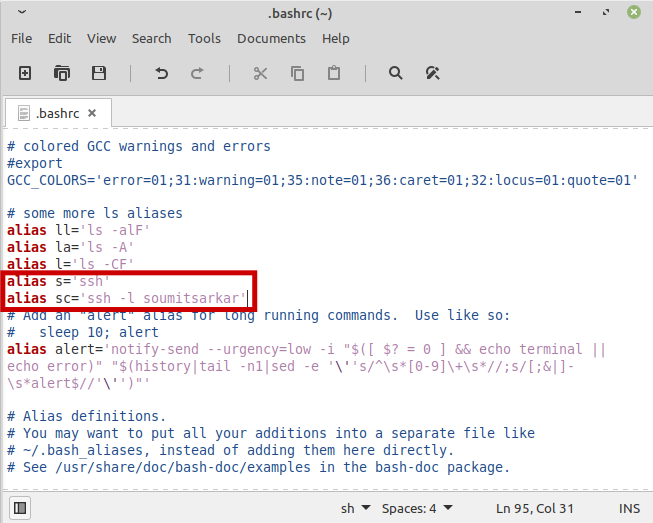
The reason for this smarter approach is to reduce character typed by 66%. We can simply use s 192.168.1.1 whenever we need to SSH into a device with the given IP. Also, for sc 192.168.1.1, ssh -l command will open a local port. Everything that we send to that port is put through the ssh connection and leaves through the server.
Editing /etc/ssh/ssh_config File
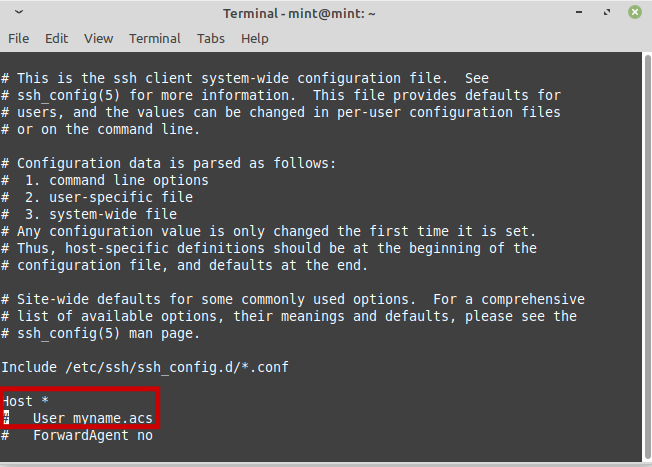
By default, our ssh username will be our username with which we logged into the Linux machine. The ssh_config file in the /etc/ssh/ssh_config is to be changed. Edit the file with the command:
vi /etc/ssh/ssh_config
Add the following lines in the file:
Host *
User myname.acs
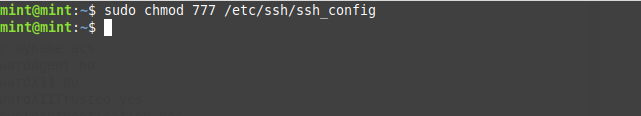
Change permission of the file with the following command:
sudo chmod 777 /etc/ssh/ssh_config
Now if we simply try to ssh into any device, and we’ll see the username has changed to myname.acs by default.
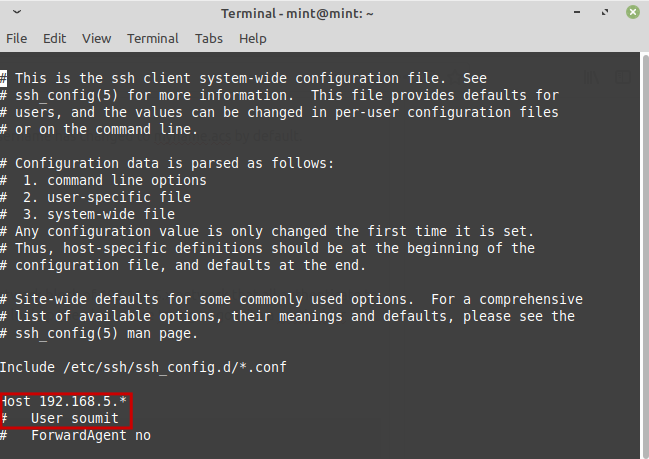
Username changing for a specific subnet
Now often we will find there are multiple devices under the network block of 192.168.5.x network that all authenticate to the same username ‘Henry.acs’. It’s possible to configure ssh to lookup the place we’re trying to go with a particular username before SSH. Go back into editing the file:
vi /etc/ssh/ssh_config
On top of the file add these lines:
Host 192.168.5.*
User adifferenetusername
Use keys To Log in Instead Of A Password
If you’re trying to ssh from one Linux machine to another it’s safer and more convenient to use authentication keys instead of a password. That makes the connection more secure from most external Man In Middle Attacks.
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...