How to Change User Password in Linux | passwd Command
Last Updated :
22 Dec, 2023
Securing user accounts is a fundamental aspect of maintaining a robust and secure Linux system. One essential task is changing user passwords regularly to prevent unauthorized access. The passwd command in Linux provides a straightforward and effective way to modify user passwords. This article will guide you through the process of changing user passwords using the passwd command, offering insights into its various options and best practices.
Understanding the `passwd` Command
The passwd command in Linux is a powerful tool that allows system administrators and users to manage password-related tasks. Its primary purpose is to change user passwords, but it offers additional functionalities such as updating password aging policies, unlocking accounts, and more.
Basic Syntax of `passwd` in Linux
passwd [options] [username]
Here,
[options] = include various parameters to customize the password-changing process.
[username] = the target user account for which you want to change the password.
Options Available in `passwd` Command in Linux
|
Deletes the user password, making the account password-less.
|
|
Immediately expires the account password, prompting the user to change it on the next login.
|
|
Displays help related to the `passwd` command.
|
|
Sets the number of days after password expiration before the account is deactivated.
|
|
Changes the password only if it is expired, keeping authentication tokens if not expired.
|
|
Locks the password of the user, preventing login with a password. Other authentication methods like SSH keys can still be used.
|
|
Changes the minimum number of days between password changes, preventing the user from changing the password for a specified period.
|
|
Enables quiet mode, suppressing the usual message “Changing password for $user” during password change.
|
|
Changes the password for a specified repository.
|
|
Applies changes in the specified directory and uses configuration files from that directory. This temporarily changes the root directory for the passwd process.
|
|
Shows the password status of a user, including last change date, minimum age, maximum age, warning period, and inactivity period.
|
|
Shows password status for all users. Requires the use of -S option.
|
|
Unlocks the password of an account, allowing login with the password.
|
|
Changes the number of days before password expiration to display a warning.
|
|
Sets the maximum number of days a password remains valid. After MAX_DAYS, the user is forced to change the password.
|
1. How to Change User Password in Linux
To change a user password using the passwd command, follow these steps:
Step 1: Open a terminal on your Linux system.
Step 2: Type the following command and press Enter:
passwd
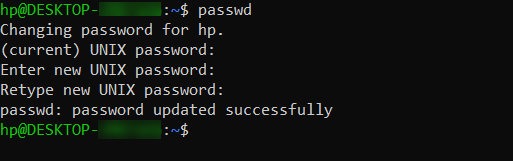
how to change user password in Linux
- If you are not the root user, you will be prompted to enter your current password to proceed.
- You will then be prompted to enter the new password. Type the new password and press Enter.
- Retype the new password when prompted to confirm.
- The password for the specified user account is now changed.
Note: Linux does not display any characters on the screen while you type the password for security reasons.
2. How to Change Another User’s Password in Linux
To change the password for a user other than the one currently logged in, you can use the following steps:
Step 1: Open a terminal on your Linux system.
Step 2: Type the following command and press Enter:
passwd user1
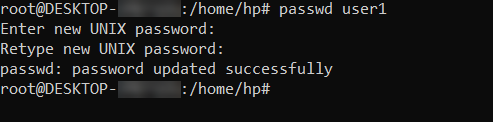
How to change another user password
- If you are not the root user, you may be prompted to enter your current password to proceed.
- You will then be prompted to enter the new password. Type the new password and press Enter. Linux does not display any characters on the screen while you type the password for security reasons.
- Retype the new password when prompted to confirm.
- The password for the user “john” is now changed.
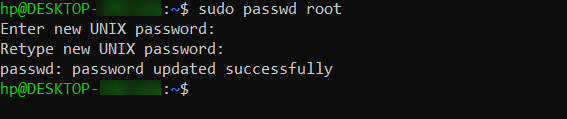
Note: sudo can be used to invoke root privileges by normal users, and can change the password for root itself. This is particularly helpful when a user is member of admin group (holds a position in sudoers list (/etc/sudoers) and can use commands with sudo) and the root password is not set, which is case with many common distributions of linux.
sudo passwd root
3. How to Change the User Password Forcely
To force a user to change their password at the next login, use the following command:
passed -e user1

changing the user password forcefully
This immediately expires the user’s password, requiring them to change it the next time they log in.
4. How to Lock and Unlock User Account in Linux
To lock or unlock a user account, use the following commands:
To lock the account:
passwd -l user2
The password for the user “user2” is now locked, preventing login.
To unlock the account:
passwd -u user2
The password for the user “user2” is now unlocked, allowing login again.
5. How to Set Password Expiry
The -x option allows you to set the maximum number of days a password is valid. Example:
passwd -x 30 user3
This sets a maximum password age of 30 days for the user “user3”
Processing in passwd command:
- Verify current user password : Once the user enters passwd command, it prompts for current user password, which is verified against the password stored in /etc/shadow file user. The root user can bypass this step and can directly change the password, so as the forgotten passwords may be recovered.
- Verify password aging information : In Linux, a user password can be set to expire after a given period of time. Also, a user can be prohibited to change his/her password for a period. This password aging information (and the password itself) is stored in a file /etc/shadow.
- Change the password : After authentication, the user is prompted to enter the new password and verify it by retyping the password.
- /etc/shadow file: The shadow file is a list of colon separated values with 9 fields, as shown below:
user1:$6$x8wAJRpP$EWC97sXW5tqac10Q2TQyXkR.1l1jdK4VLK1pkZKmA2mbA6UnSGyo94Pis074viWBA3sVbkCptSZzuP2K.y.an/:17887:0:99999:7:::
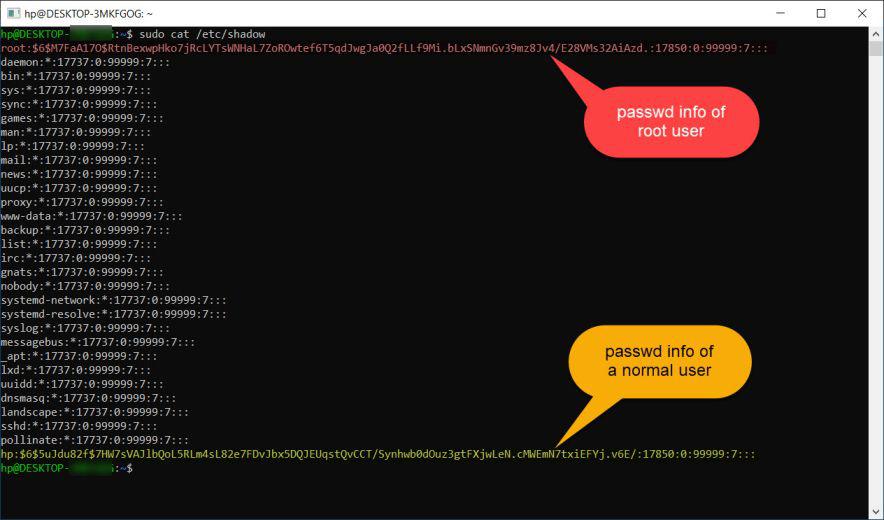
Processing in passed Command
- field 1: User name.
- field 2: Encrypted Password.
- field 3: Number of days since January 1, 1970 to when the password was last changed.
- field 4: Minimum number of days for which password can not be changed. (value 0 means it can be changed anytime).
- field 5: Number of days after password must be changed. (value 99999 means that the password never expires).
- field 6: Number of days to warn user for expiring password.
- field 7: Number of days after password expires that the account is disabled.
- field 8: The number of days from January 1, 1970 to the date when an account was disabled.
- field 9: This field is reserved for some possible future use.
Conclusion
In this article, we learned how to change user passwords in Linux using the passwd command. We explored its various features, from basic password changes to more advanced options like forcing updates, locking and unlocking accounts, and setting password expiry. By understanding these functionalities, Linux users and administrators can strengthen the security of their systems. Regularly updating passwords and following best practices play a crucial role in safeguarding against unauthorized access. The passwd command serves as a handy tool for managing these aspects, making it an essential part of maintaining a secure Linux environment.
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...